
Stay Ahead of Digital Threats
Act Fast. Scale Further. Stay in Control.
Every minute a threat stays live, the damage grows. unphish automates detection, response, and verification at speed. No compromises on visibility or control.
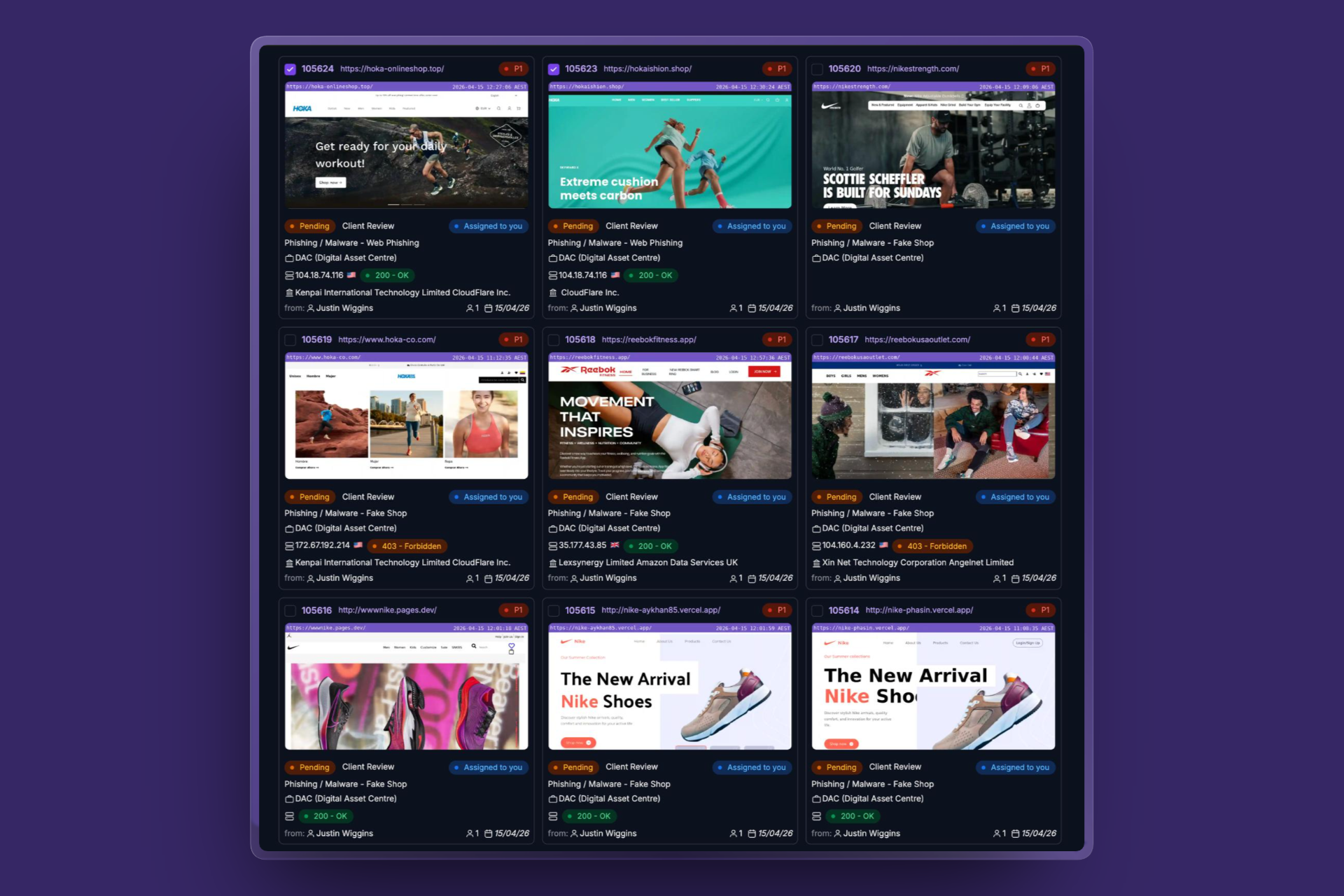
Faster Detection and Disruption
Reduce exposure by automating the time between identifying threats and taking action. Minimise dwell time and limit impact with rapid, coordinated response.
End-to-End Automation
From detecting malicious infrastructure to evidence collection and takedown execution, automation is embedded across every stage for consistent and efficient outcomes.
Operate at Scale with Control
Scale operations without fragmented tools or manual workflows. Maintain full visibility, governance, and accountability across all enforcement actions.
Built for a Changing Threat Landscape
Cyber-enabled scams, phishing, and brand abuse are constantly evolving. Attackers adapt their infrastructure, techniques, and distribution channels to bypass controls and exploit trust at scale.
A solution that worked yesterday is often ineffective today.
unphish is designed for this reality.
We help organisations stay ahead by continuously evolving how threats are detected, prioritised, and disrupted across digital environments.
Stay Ahead as Threats Evolve
Threats will continue to change. New platforms will emerge, and attackers will constantly adapt their tactics.
unphish is not a static solution. It is built to continuously evolve how threats are detected, prioritised, and disrupted so your organisation stays ahead of what comes next.

AI-Driven Detection and Decision Making
Better signals. Smarter decisions. Stronger outcomes.
unphish applies artificial intelligence to improve both detection accuracy and response effectiveness.
- Identifying emerging scam patterns and infrastructure reuse
- Analysing content, branding, and behavioural signals across channels
- Prioritising threats based on risk, exposure, and potential impact
- Continuously refining detection models as attacker tactics evolve
Designed for Modern Scam Operations
Modern scam operations are multi-channel, infrastructure-driven, and highly coordinated.
- Open web environments
- Social platforms
- Mobile and app ecosystems
- Underground and attacker-controlled infrastructure
The platform built for modern threat response
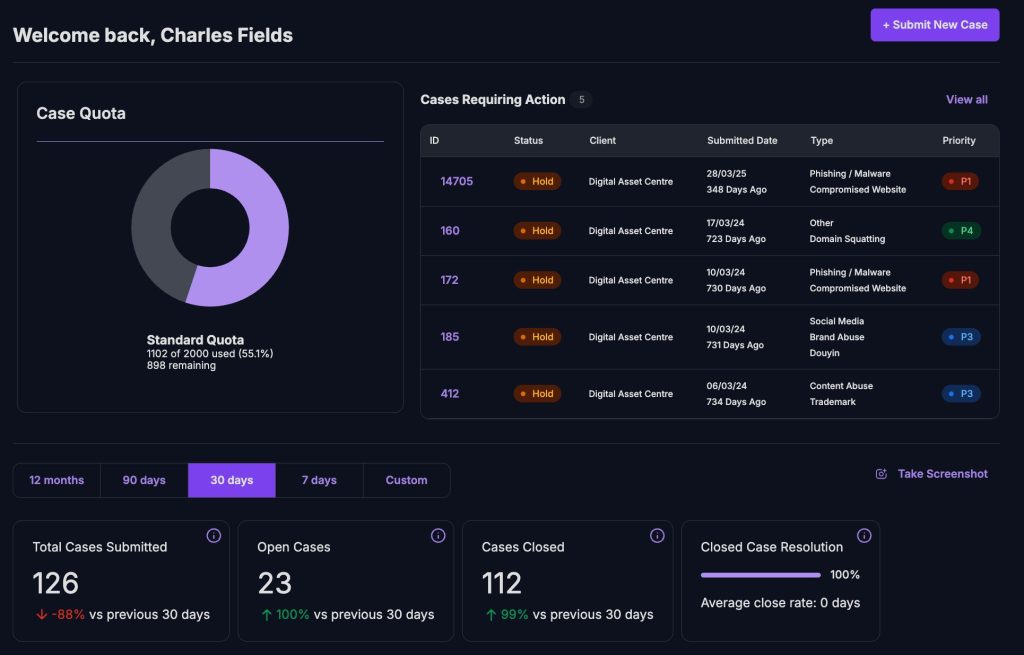
Threats don’t wait. unphish gives security teams the visibility to spot them, the automation to act instantly, and the control to prove it.
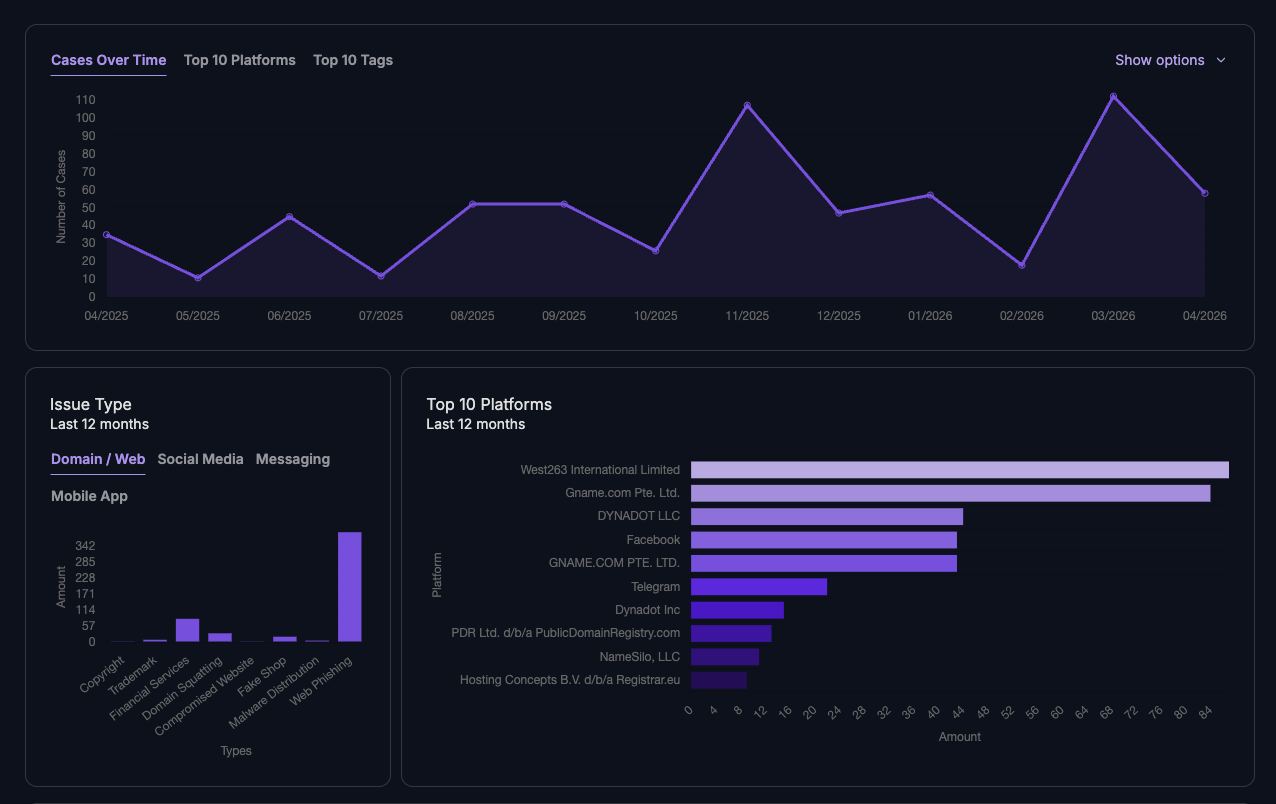
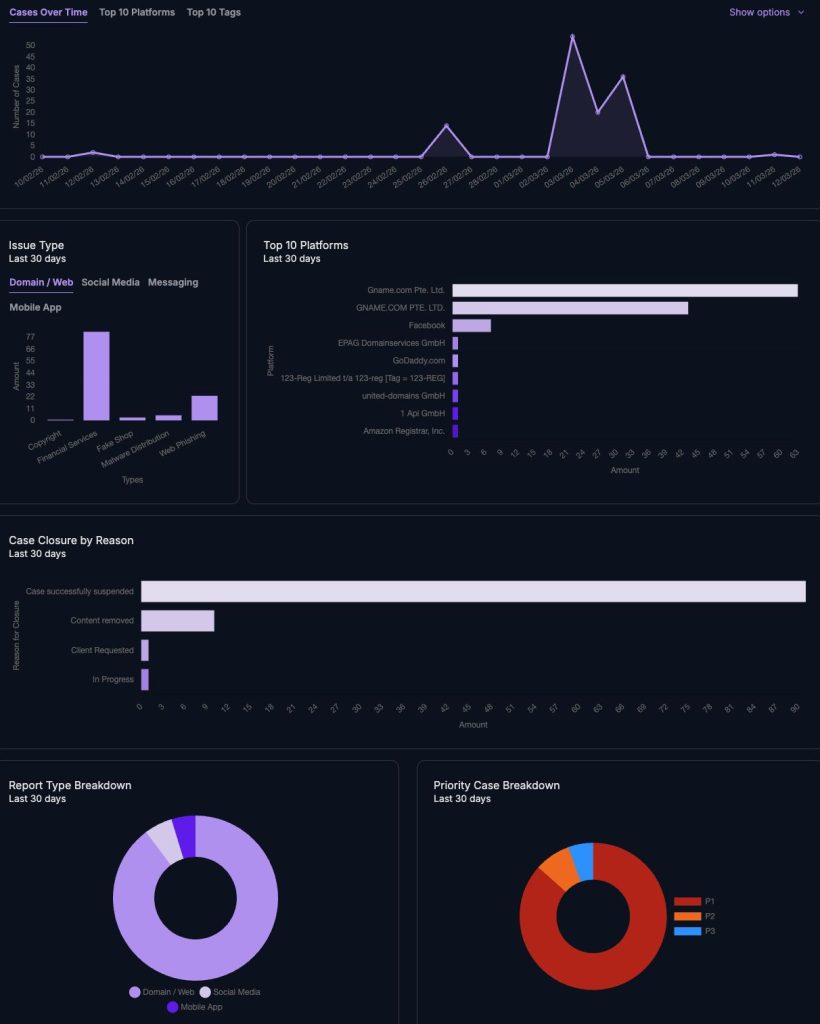
Unified Threat Visibility
Gain centralised visibility across phishing, impersonation, and malicious infrastructure with structured intelligence and expert oversight.
Faster Time to Disruption
Reduce time from detection to takedown with automated workflows that accelerate response and minimise exposure.
Scalable Operations
Handle increasing threat volumes without expanding teams by automating repetitive tasks and standardising enforcement processes.
Accurate Threat Prioritisation
Improve decision-making with enriched intelligence that helps identify, prioritise, and act on the most critical threats first.
Continuous Monitoring & Outcomes
Track threats and enforcement actions with measurable results, ensuring ongoing visibility into performance and impact.
Controlled & Auditable Enforcement
Maintain full control with structured workflows, clear accountability, and audit-ready records across every action taken.
Adaptable by Design
Every organisation faces a unique threat landscape.
unphish is adaptable by design, allowing detection, prioritisation, and enforcement to align with specific industries, risk profiles, and customer environments.
As business priorities or threat conditions change, the platform evolves without requiring new tooling or structural changes.


 Editor’s Pick
Editor’s Pick 


