Brand Abuse
unphish detects and disrupts unauthorised use of brand across domains, social platforms, and digital infrastructure, removing impersonation, fake services, and misleading content before they erode customer trust or brand value.
Protect Your Brand Across the Digital Ecosystem
Brand abuse occurs when criminals exploit your organisation’s name, trademarks, products, or reputation to mislead customers and generate profit from trust you have built over time. It extends beyond traditional phishing and includes fake websites, impersonation accounts, misleading advertising, counterfeit services, and unauthorised digital content.
Unlike isolated phishing emails, brand abuse is persistent, distributed, and platform-driven. It often operates outside the visibility of traditional security tools, quietly eroding customer trust and brand equity.
unphish enables organisations to continuously detect, prioritise, and disrupt brand abuse across domains, social platforms, marketplaces, and hosting infrastructure.
Common Forms of Brand Abuse
Brand abuse adapts to your industry, customer base, and digital footprint. Common examples include:
Lookalike Domains
Lookalike domains and websites impersonating official brand properties.
Social Impersonation
Fake social media profiles and posts using logos and brand identity.
Content Misuse
Unauthorised use of trademarks, product imagery, and marketing content.
Fraudulent Offers
Scam services, investment offers, or partnerships falsely presented as legitimate.
How unphish Detects Brand Abuse
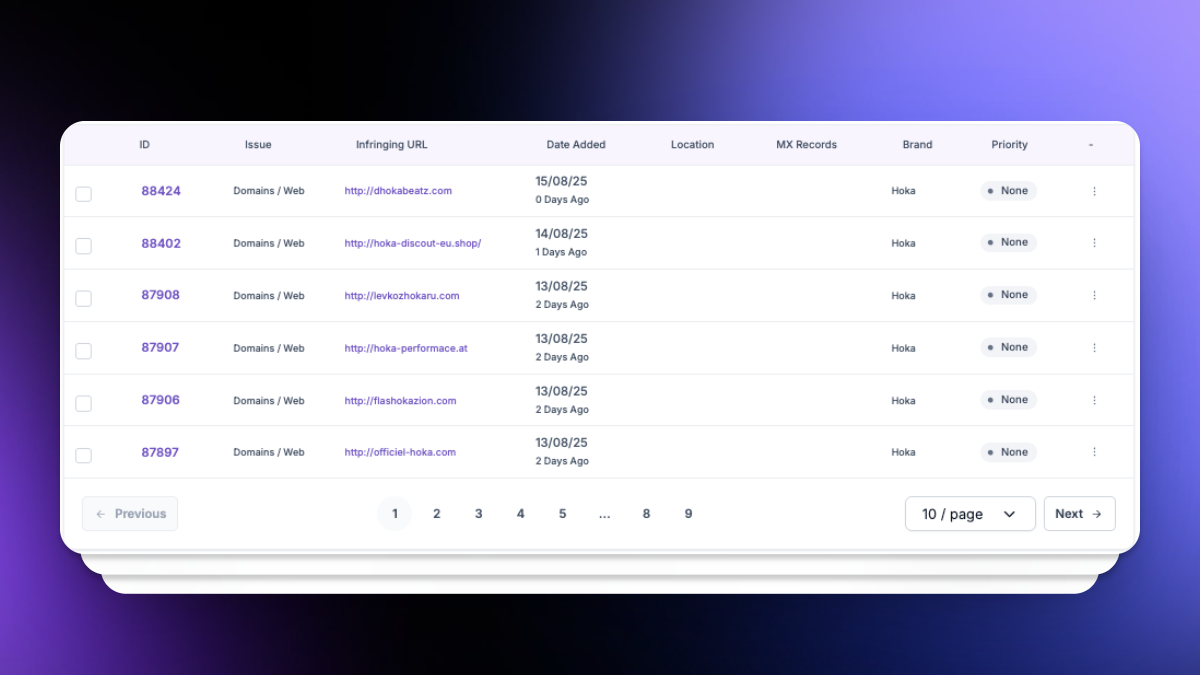
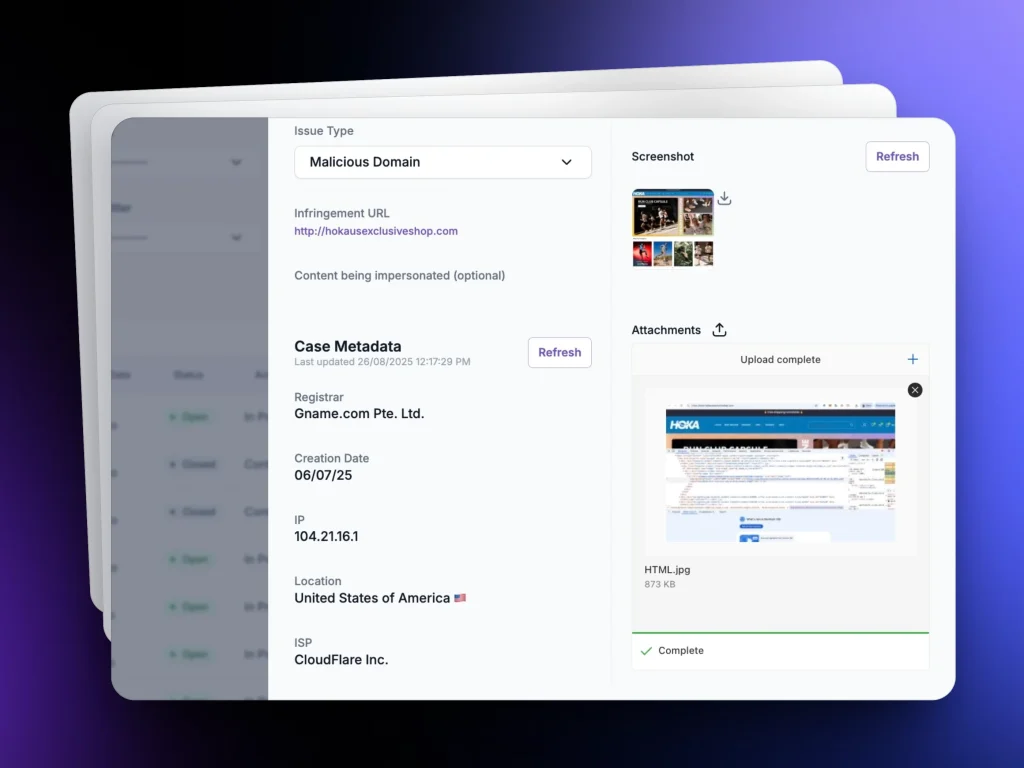
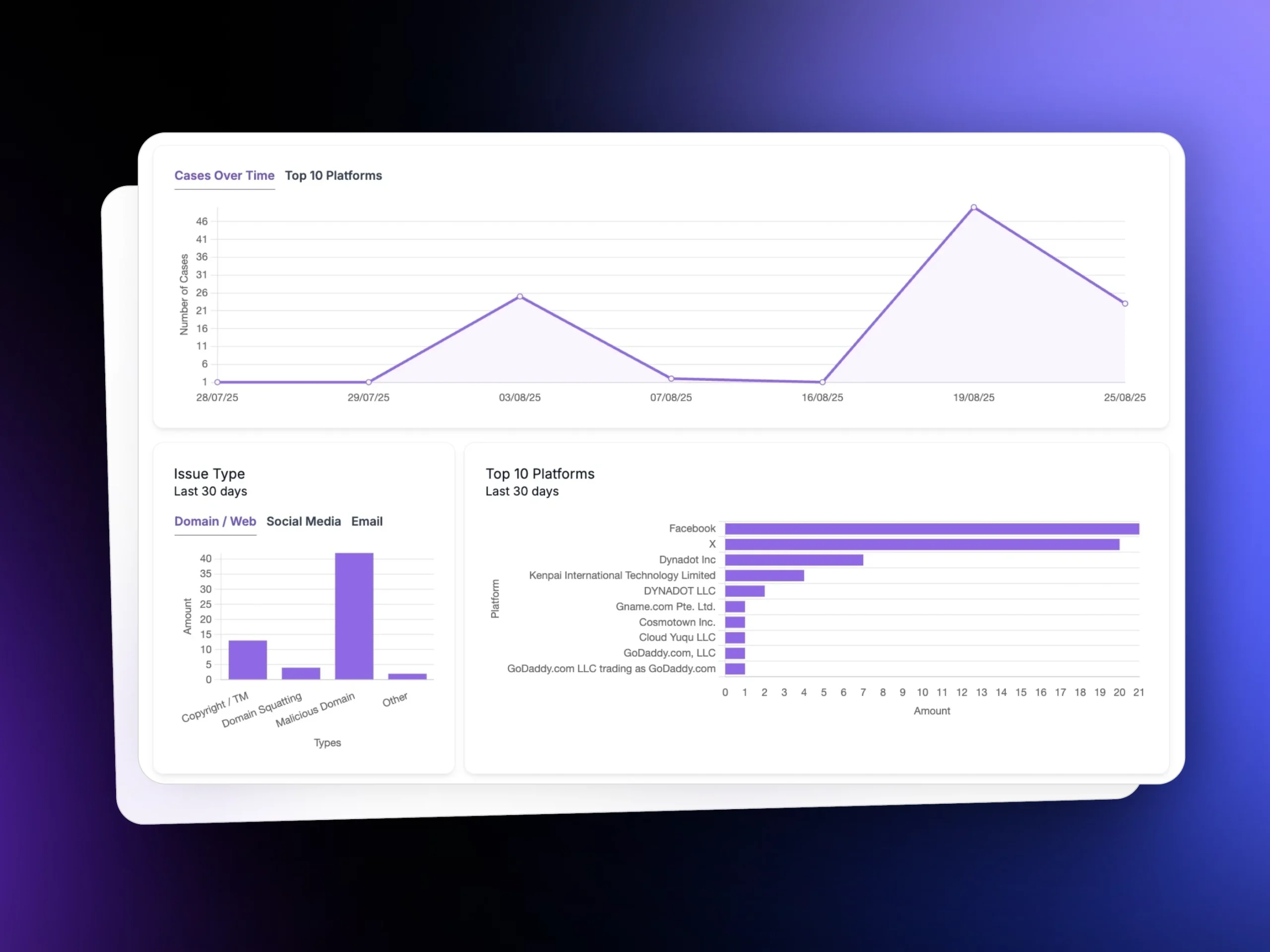
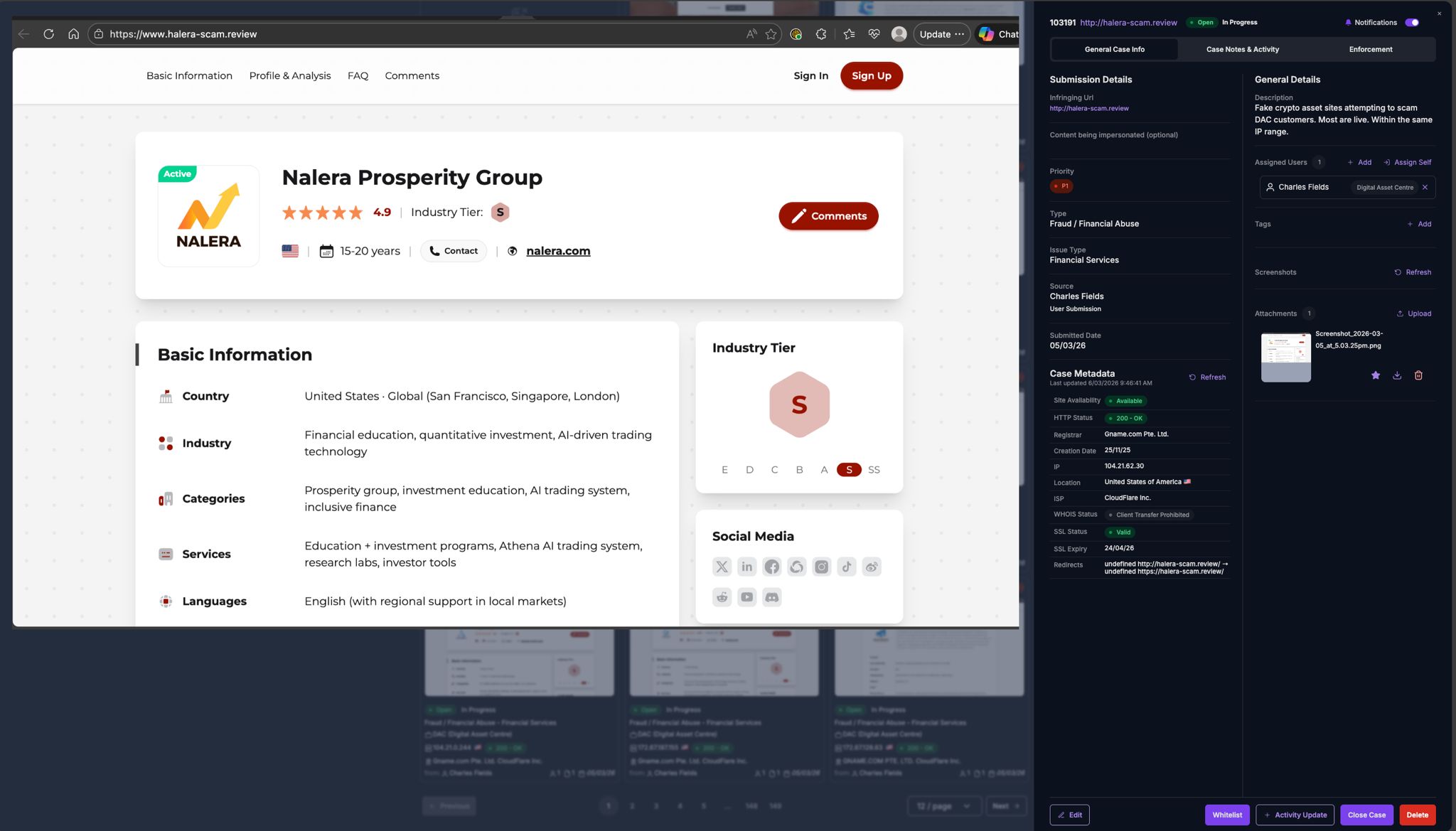
unphish continuously scans for unauthorised brand use across domains, websites, social platforms, and related infrastructure. Detection combines automated brand recognition, infrastructure analysis, and intelligence correlation.
Brand Monitoring
Evidence Collection
Detection of cloned or misleading websites that replicate official branding and content.
Enforcement
Infrastructure Analysis
Analysis of campaign infrastructure to uncover related abuse and repeat offenders.
Why Customers Choose unphish
| unphish | Fragmented / Reactive Approach | |
| Threat Visibility | Continuous monitoring across domains, hosting, social platforms, and attacker infrastructure. | Limited visibility based on complaints or isolated alerts. |
| Detection Speed | Automated detection and risk scoring identify threats early. | Threats are discovered late, often after impact. |
| Infrastructure Insight | Deep analysis reveals campaign links, infrastructure reuse, and attacker patterns. | Little or no visibility into shared infrastructure or repeat activity. |
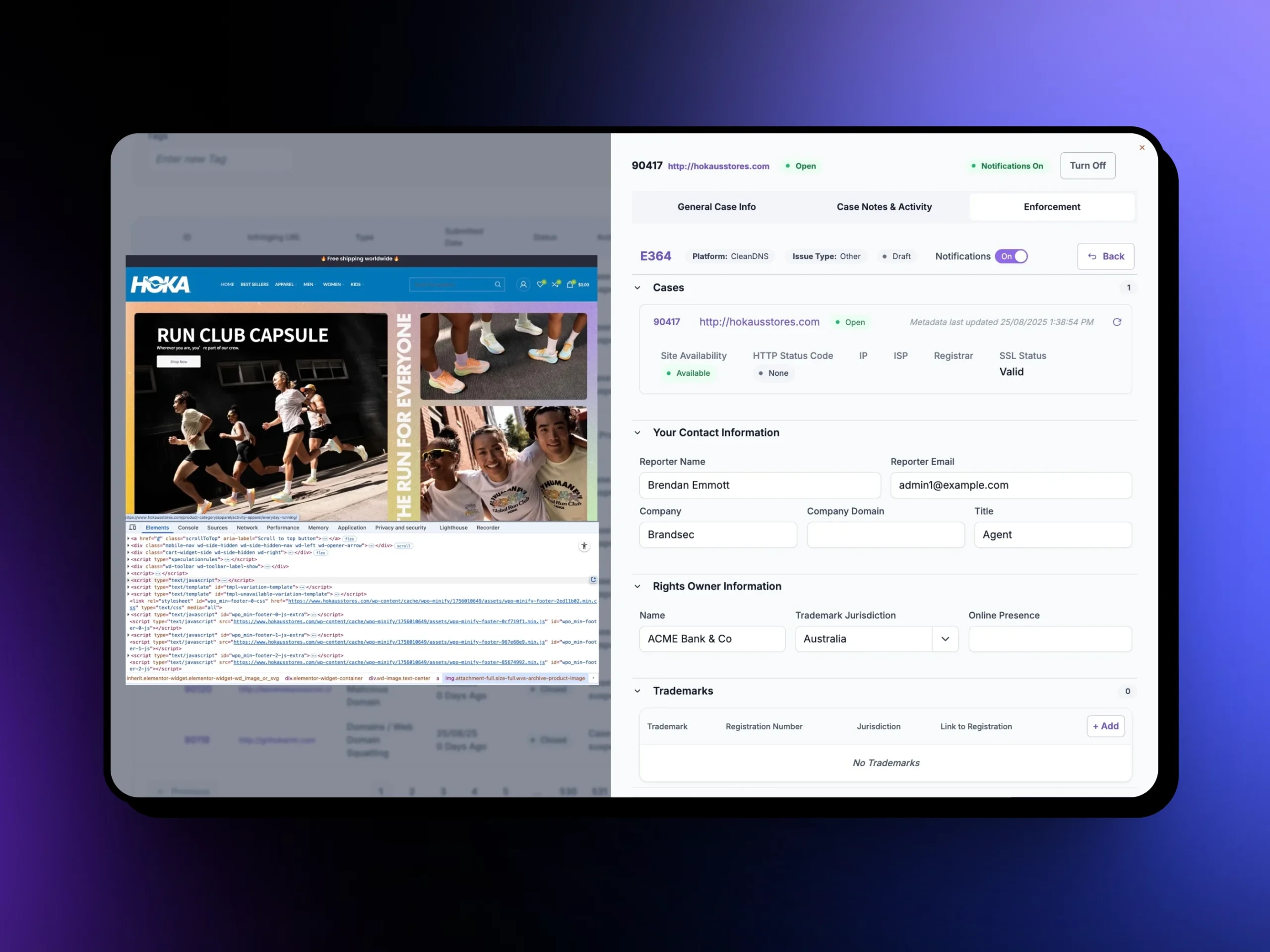
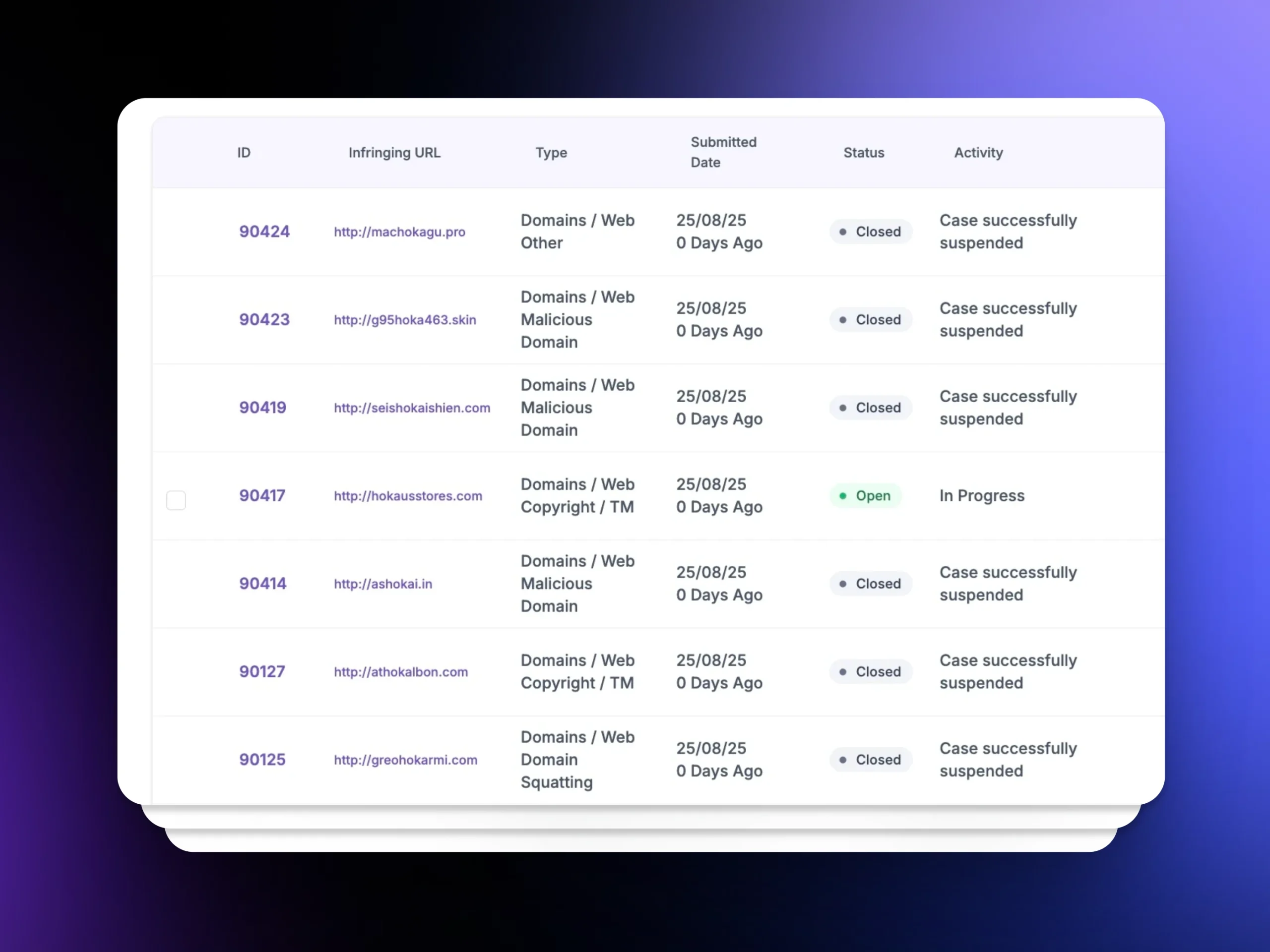
| Enforcement Execution | Coordinated workflows enable faster, consistent takedown across platforms. | Manual submissions slow down response and create inconsistent outcomes. |
| Verification & Control | Automated validation confirms removal and tracks reappearance. | No structured verification or monitoring after takedown. |
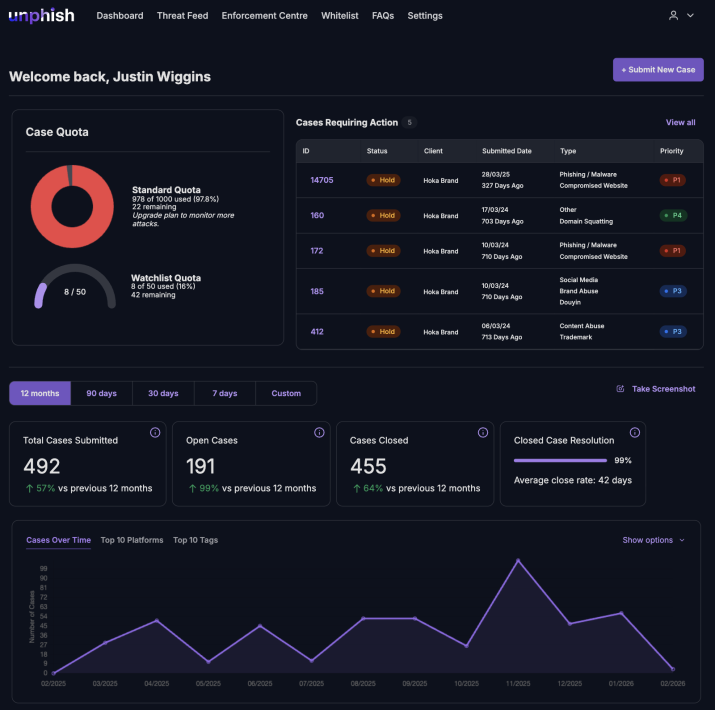
| Operational Visibility | Unified dashboards provide clear status, timelines, and reporting. | Siloed tools limit visibility and create operational gaps. |
How unphish Enforces and Remediates Brand Abuse
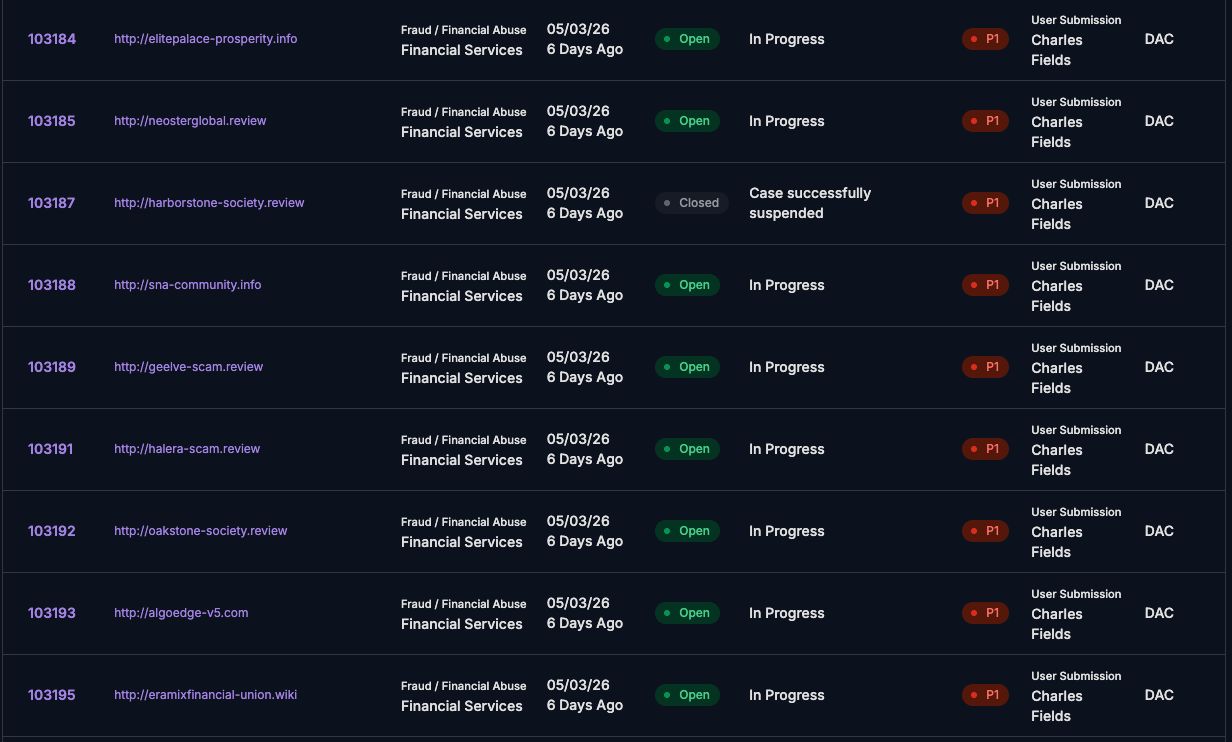
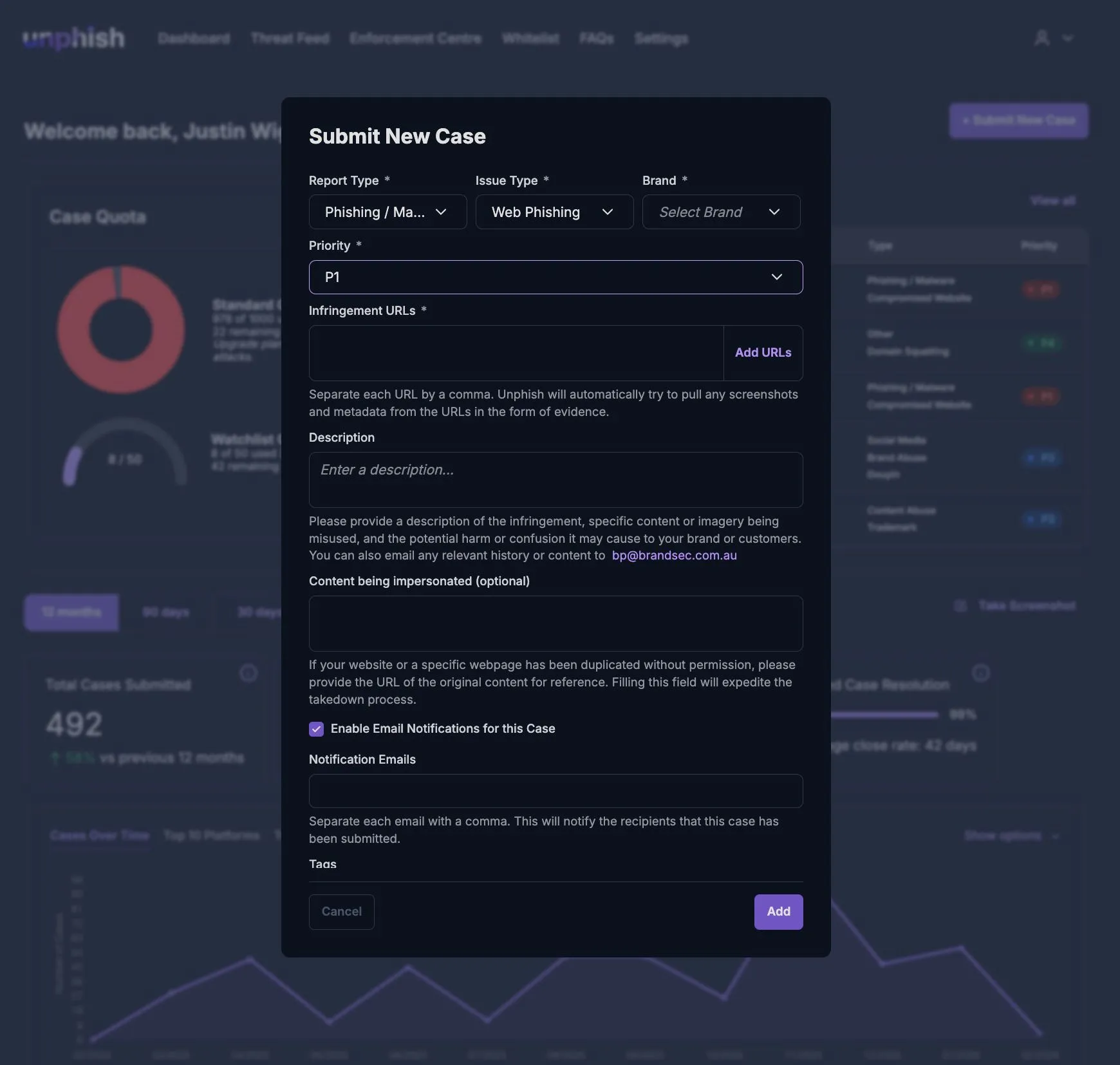
unphish integrates enforcement directly into the platform, allowing organisations to move from identification to remediation without delay. For every brand abuse incident, the platform automatically collects and preserves enforcement-ready evidence, including visual captures, hosting information, domain data, and platform-specific artefacts. This enables efficient and defensible takedown actions across registrars, hosting providers, social platforms, and digital services.
Enforcement actions may include
unphish enables rapid enforcement actions to remove abusive assets and disrupt ongoing brand abuse.
Impersonation Website Takedown
Takedown of impersonation websites and fraudulent services
Infringing Domain Suspension
Suspension of lookalike or infringing domains
Fake Social
Profile Removal
Removal of fake social media profiles and pages
Repeat Offender Escalation
Escalation of repeat offenders using shared infrastructure or assets
Why Brand Abuse Protection Matters
Brand trust is a strategic asset. When customers encounter fake websites, misleading ads, or impersonation accounts, the impact extends beyond a single incident and undermines long-term confidence.
unphish reduces the visibility and lifespan of brand abuse campaigns, protects customers from deception, and provides compliance, legal, and risk teams with auditable records of action taken.
By treating brand abuse as an ongoing operational threat rather than isolated incidents, unphish enables organisations to defend their digital presence with consistency, speed, and measurable disruption.
FAQs
Key questions about how unphish detects, investigates, and disrupts brand abuse across digital channels.
1. How quickly can brand abuse assets be removed?
2. Does unphish detect abuse across domains, websites, and social platforms?
3. Can enforcement actions be prioritised based on brand risk?
4. How does unphish identify coordinated or repeat brand abuse campaigns?
Stop Brand Abuse Before It Spreads
Move beyond detection and take decisive action to remove impersonation assets and disrupt ongoing brand abuse across digital channels.