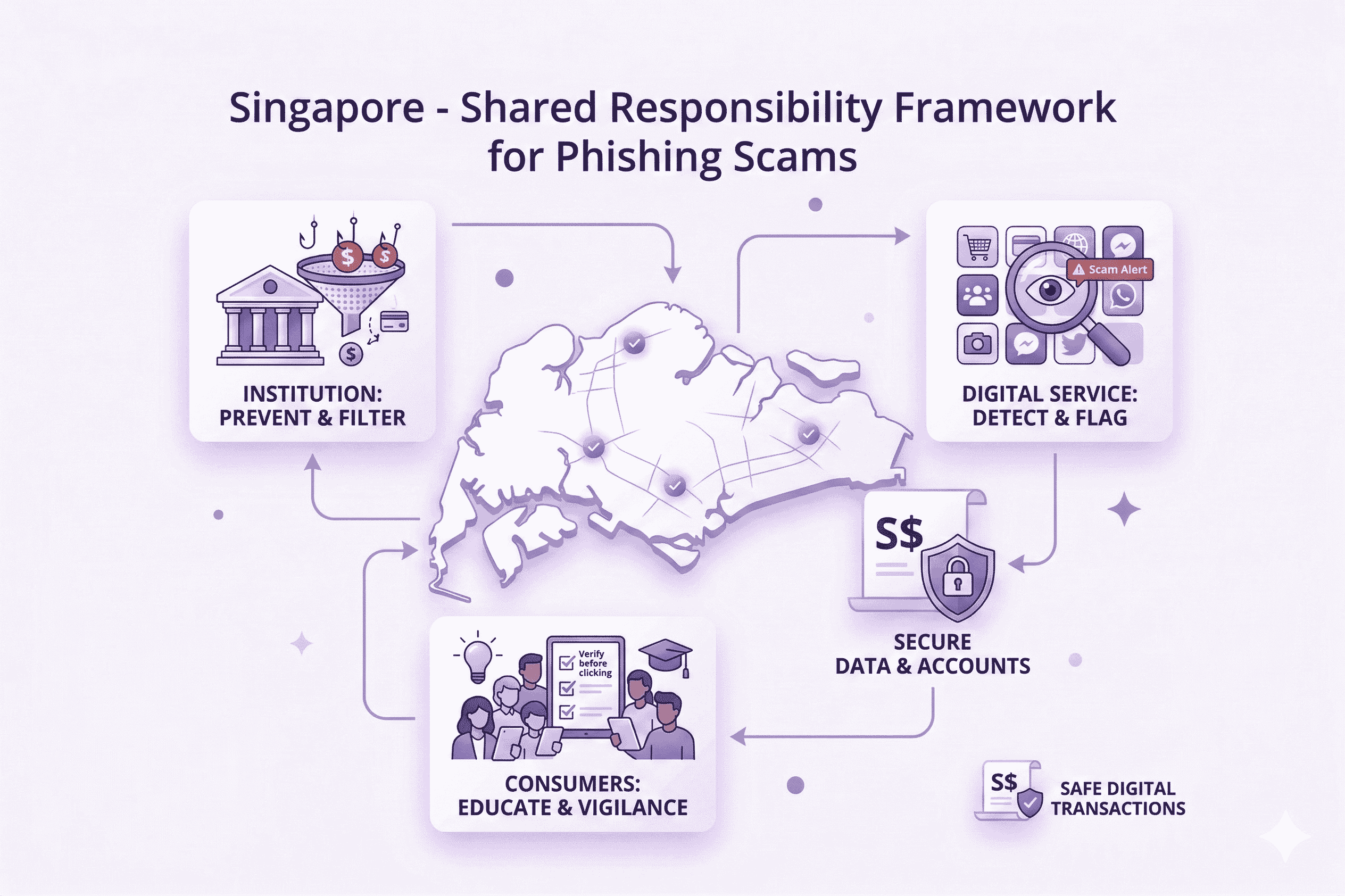
Singapore – Shared Responsibility Framework for Phishing Scams
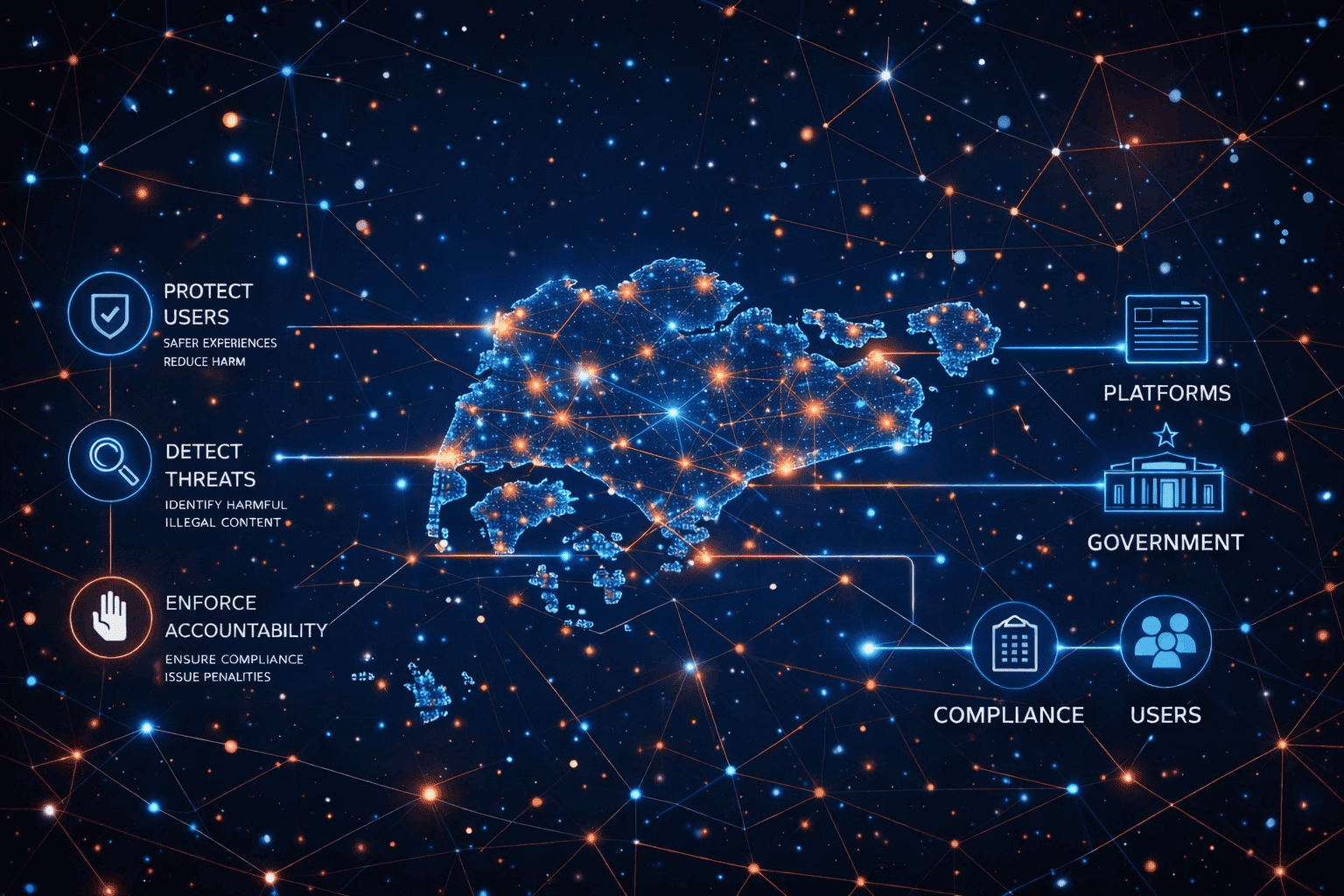
A Targeted Accountability Framework for Phishing Scams in Singapore
Singapore’s Shared Responsibility Framework (SRF) establishes a structured approach to mitigating phishing scams by clearly defining responsibilities across financial institutions and telecommunications providers.
The framework introduces a coordinated duty model where each stakeholder is expected to implement specific preventive and responsive controls. Where these obligations are not met, the framework provides clarity on how financial losses may be allocated, creating a strong incentive for proactive risk management.
Jointly implemented by the Monetary Authority of Singapore (MAS) and the Infocomm Media Development Authority (IMDA), the SRF comes into effect from 16 December 2024. It represents a shift toward measurable accountability, combining prevention, response, and liability into a unified regulatory model.
Key Regulatory Shifts Under the Shared Responsibility Framework
The SRF introduces enforceable expectations designed to reduce phishing risks while strengthening accountability across the ecosystem.
Defined Institutional Responsibilities
Obligations for financial institutions and telecom providers to implement anti-scam controls.
Liability & Loss Allocation Model
Structured guidance on how losses are distributed when prescribed duties are not fulfilled.
Proactive Risk Mitigation Requirements
Focus on preventive controls such as detection, disruption, and safeguards.
Cross-Entity Coordination
Alignment between banks, telcos, and enforcement workflows to reduce gaps exploited by attackers.
Operational Accountability
Requirement to demonstrate that reasonable measures were in place and effectively executed.
Enforcement-Backed Compliance
Regulatory oversight ensuring adherence to prescribed duties and response standards.
What This Means for Organisations
The Shared Responsibility Framework requires organisations to move beyond reactive fraud handling toward structured, accountable anti-scam operations.
Organisations must:
-
Implement continuous monitoring across phishing vectors and infrastructure.
-
Enable rapid disruption capabilities to minimise victim exposure.
-
Maintain clear audit trails and evidence supporting enforcement actions.
-
Ensure cross-functional coordination between fraud, security, and compliance teams.
-
Demonstrate operational readiness aligned with regulatory expectations.
This shifts phishing mitigation from isolated response efforts to an integrated, compliance-driven operational model.
Core Operational Obligations Under the SRF
Monitoring & Detection
Ongoing identification of phishing infrastructure, impersonation campaigns, and scam delivery channels.
Rapid Enforcement & Disruption
Timely takedown of phishing sites, domains, and supporting infrastructure to reduce victim exposure.
Evidence & Case Management
Structured documentation of actions, timelines, and outcomes to support investigation and claims processes.
Intelligence & Pattern Detection
Identification of repeat campaigns, infrastructure reuse, and evolving phishing tactics.
Cross-Stakeholder Workflow Integration
Alignment with referral and reporting flows across financial institutions, telcos, and enforcement bodies.
Regulatory Readiness
Preparedness to demonstrate compliance with SRF obligations through clear operational records.
How unphish Aligns with the Shared Responsibility Framework
unphish supports the SRF operating model by strengthening the enforcement layer that sits alongside referral and claims processes, reducing scam persistence and repeat victimisation.
Rapid Takedown & Disruption
Immediate removal of phishing sites, impersonation domains, and malicious infrastructure used in scam journeys.
Referral-Driven Enforcement Workflows
Ingest reports from financial institutions, telecommunications providers, and frontline teams, converting them into structured enforcement actions with supporting evidence.
Continuous Monitoring & Re-Disruption
Detect reactivation, cloning, and infrastructure reuse to ensure sustained disruption beyond initial takedowns.
Compliance-Ready Evidence & Audit Trails
Generate clear artefacts, timelines, and documentation to support investigations and demonstrate that appropriate controls and actions were in place.
