Mobile Applications
Detect and remove malicious or impersonating mobile apps that misuse your brand across major app stores. Protect users from scams, credential theft, and fraudulent services while preserving brand trust in mobile ecosystems.
Mobile App Impersonation & Malicious App Threats Protection
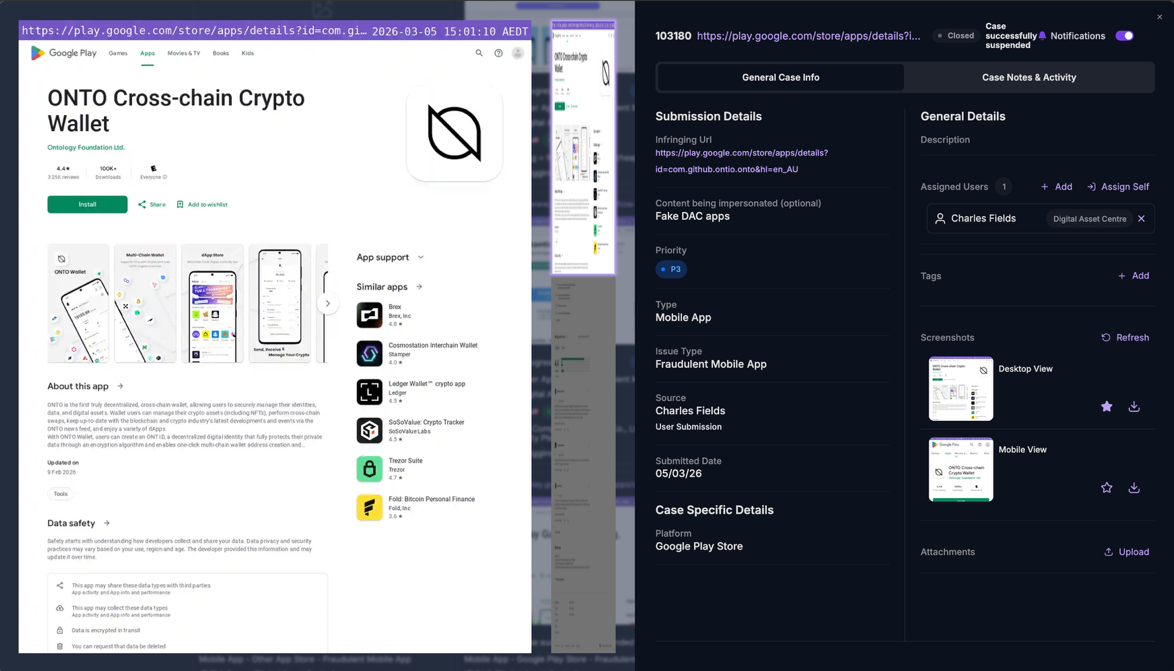
Mobile apps have become a primary channel for customer engagement, payments, and account access. This has made app stores a high value target for cybercriminals seeking to exploit brand trust and user behaviour. Malicious and impersonating mobile apps are routinely published to mimic legitimate brands, deliver scams, harvest credentials, or redirect users to fraudulent services.
These apps often appear polished and credible, using official branding, copied descriptions, and fake reviews to evade detection and convince users to install them.
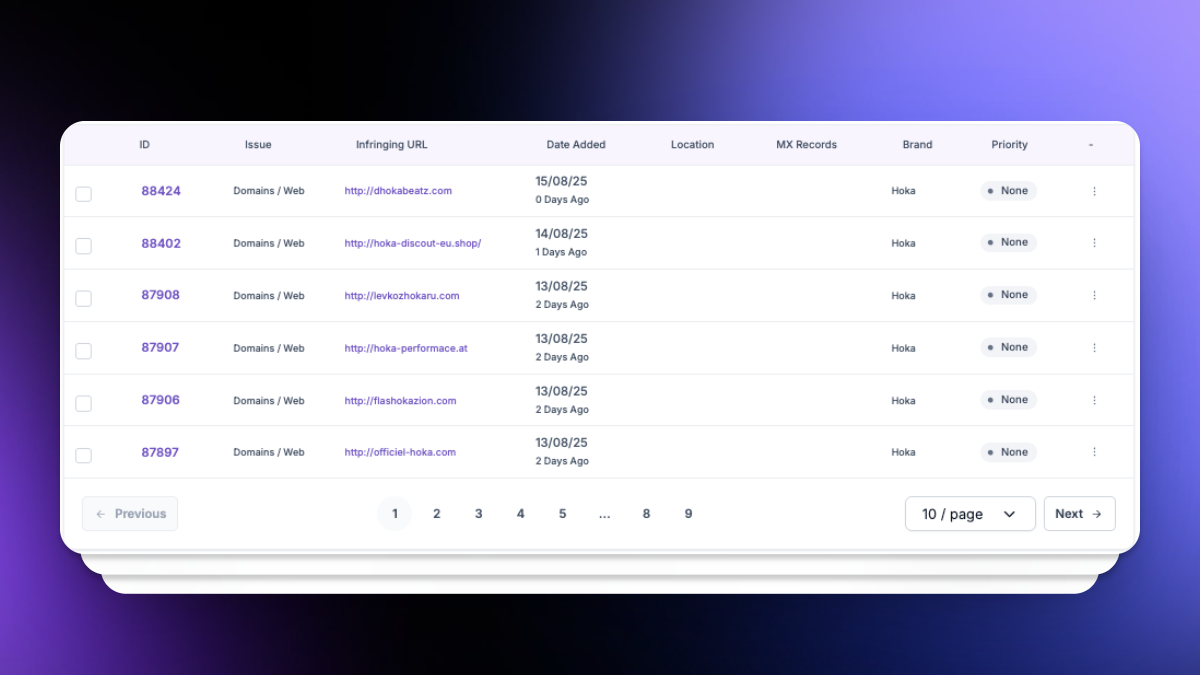
unphish helps organisations detect and disrupt malicious and impersonating mobile apps across major app stores and mobile ecosystems.Common mobile app based threats
Mobile app abuse takes multiple forms, depending on the organisation and industry. Common threats include:
Fake Brand Apps
Malicious apps designed to impersonate legitimate brands, services, or financial products. These apps mimic official branding and functionality to deceive users into believing they are authentic.
Fraudulent Service Apps
Scam apps promoting fake investment platforms, reward programs, or payment services. These apps exploit brand trust to lure users into fraudulent financial transactions.
Data Harvesting Apps
Apps built to collect sensitive user data such as login credentials, personal information, or payment details through deceptive interfaces and fake service features.
Cloned or Repackaged Apps
Modified or duplicated versions of legitimate apps using stolen branding and intellectual property, often used to redirect users to phishing sites or scam communications.
How unphish detects malicious and impersonating apps
unphish continuously monitors social media platforms for impersonation activity targeting your organisation, brands, and key individuals. Detection combines automated analysis with intelligence led techniques.
App Store Monitoring
App Evidence Analysis
Identification of cloned app descriptions, imagery, and naming conventions.
Developer & Distribution Investigation
Threat Infrastructure Correlation
Correlation of app findings with phishing campaigns, domains, and social media activity.
Why Customers Choose unphish
| unphish | Fragmented / Reactive Approach | |
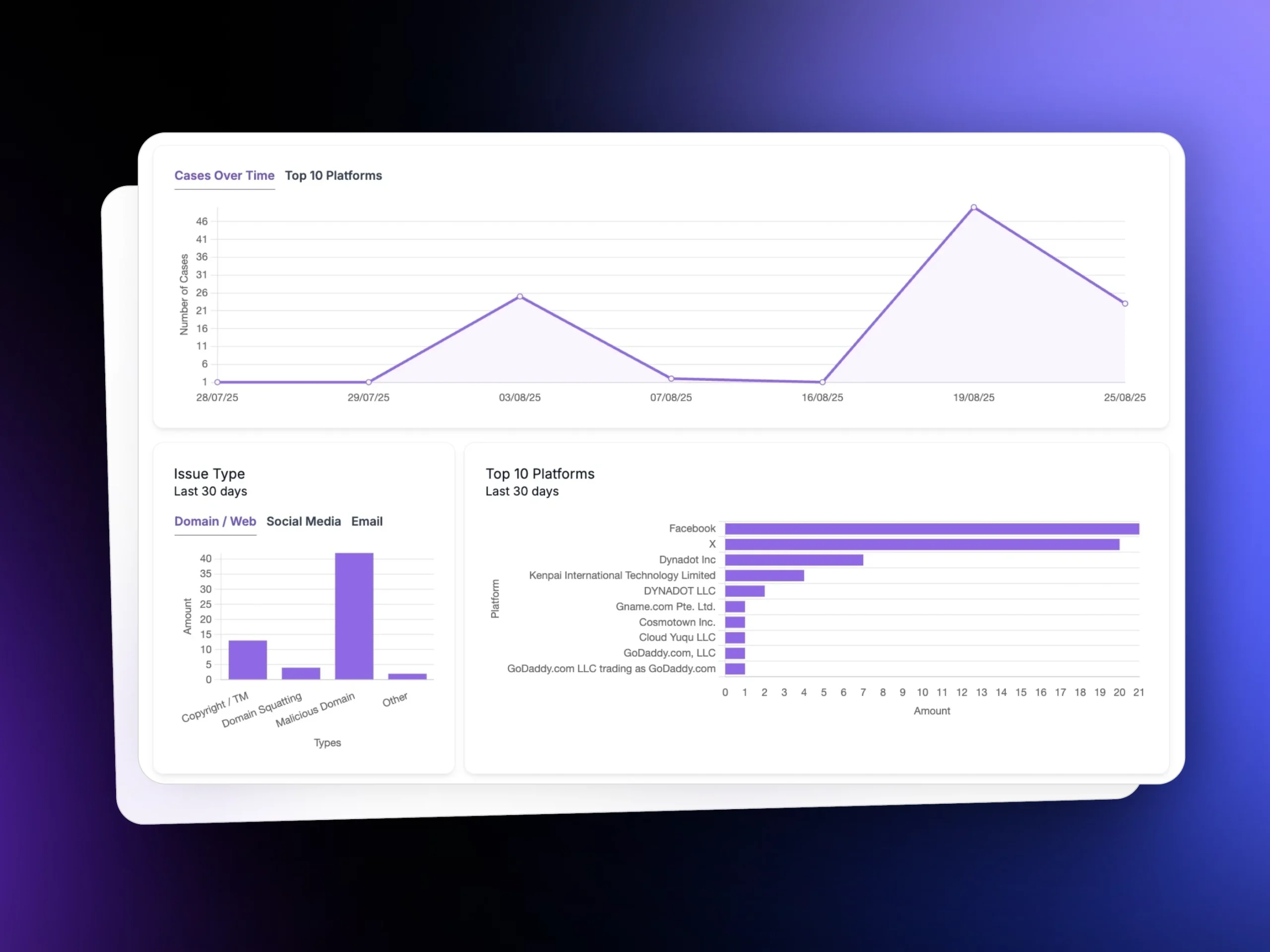
| Threat Visibility | Continuous monitoring across domains, hosting, social platforms, and attacker infrastructure. | Limited visibility based on complaints or isolated alerts. |
| Detection Speed | Automated detection and risk scoring identify threats early. | Threats are discovered late, often after impact. |
| Infrastructure Insight | Deep analysis reveals campaign links, infrastructure reuse, and attacker patterns. | Little or no visibility into shared infrastructure or repeat activity. |
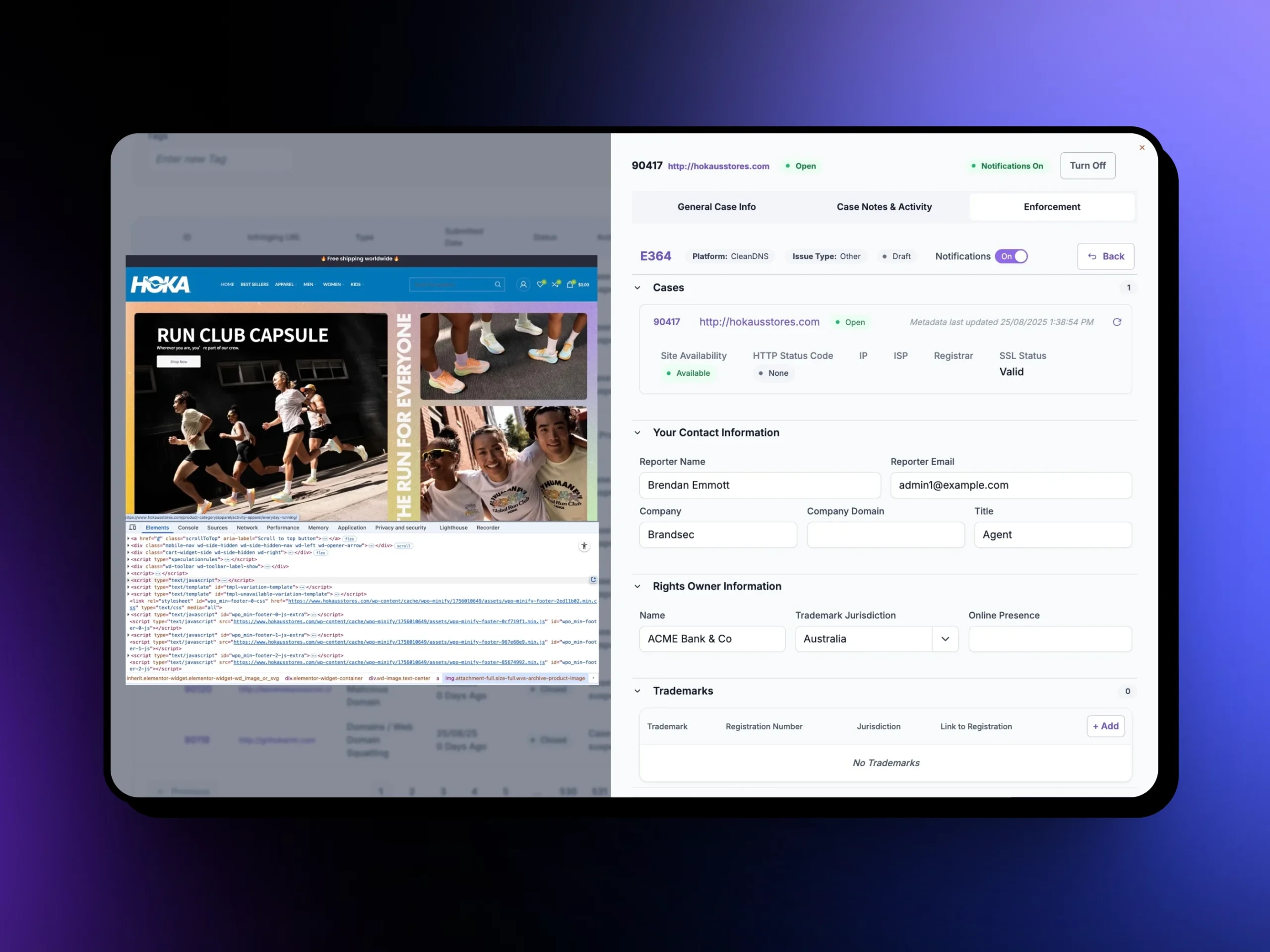
| Enforcement Execution | Coordinated workflows enable faster, consistent takedown across platforms. | Manual submissions slow down response and create inconsistent outcomes. |
| Verification & Control | Automated validation confirms removal and tracks reappearance. | No structured verification or monitoring after takedown. |
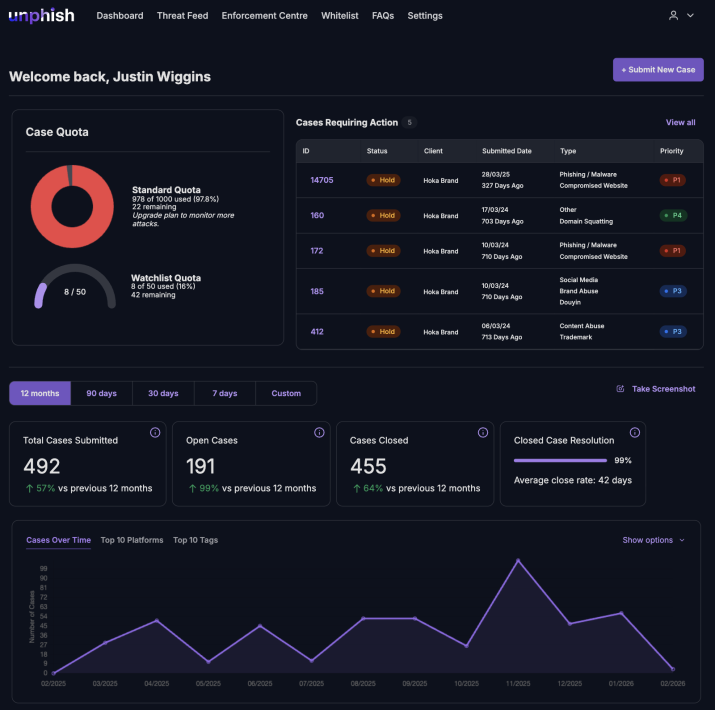
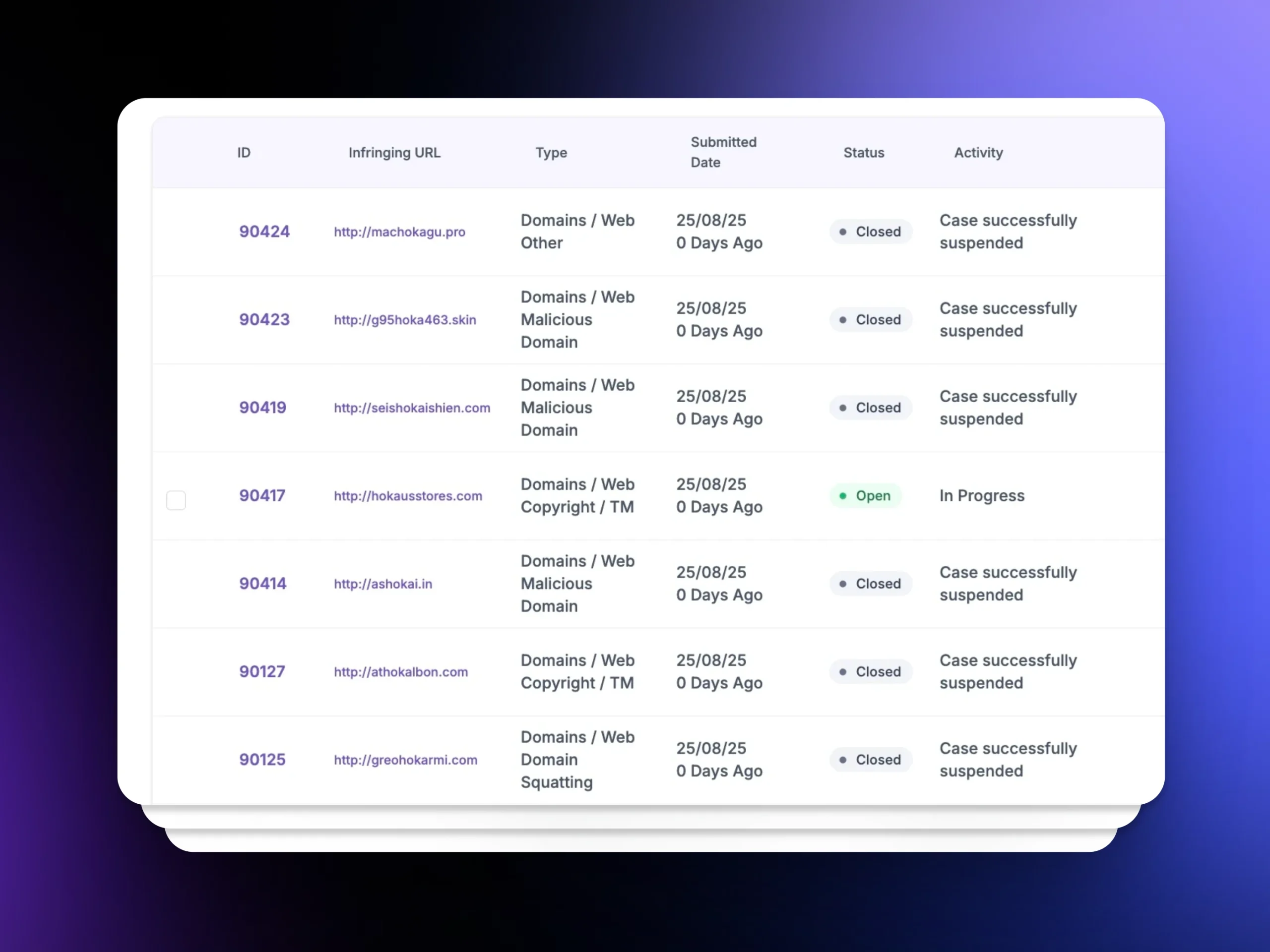
| Operational Visibility | Unified dashboards provide clear status, timelines, and reporting. | Siloed tools limit visibility and create operational gaps. |
How unphish enforces against malicious apps
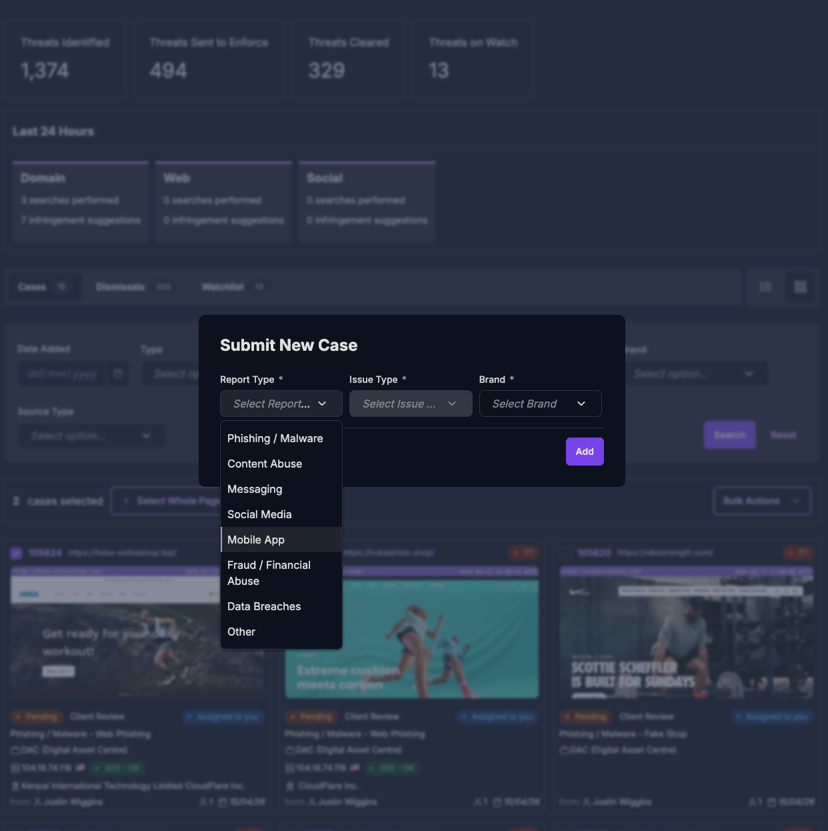
unphish streamlines enforcement by managing the end to end process required to remove malicious or impersonating apps from app stores.
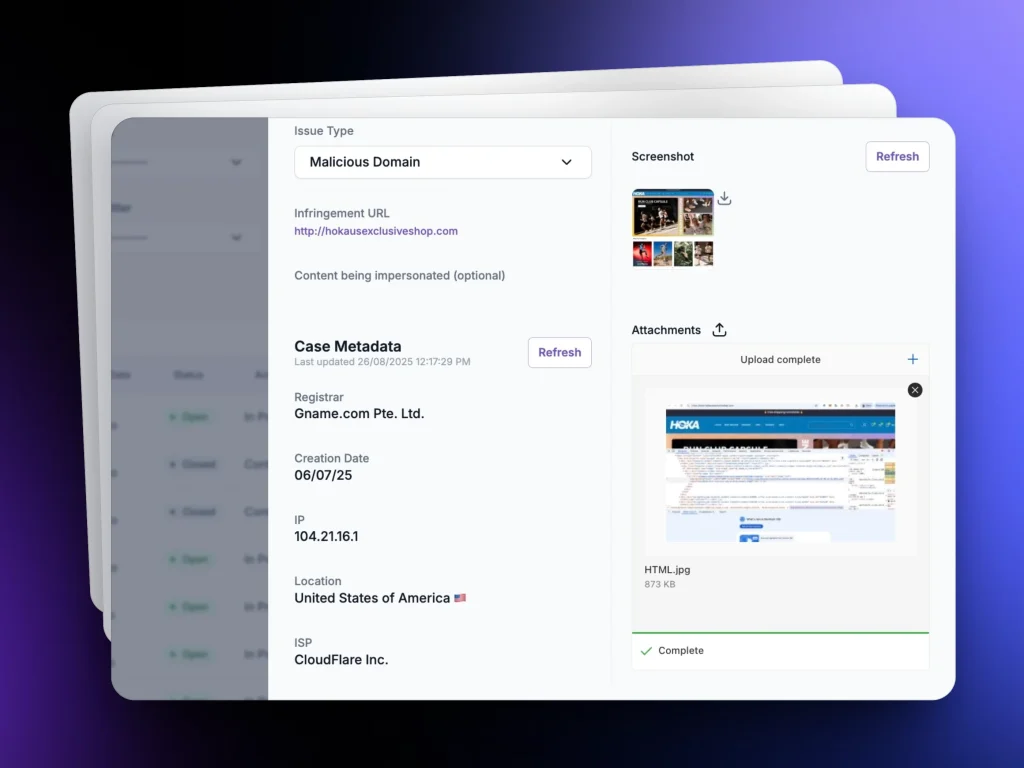
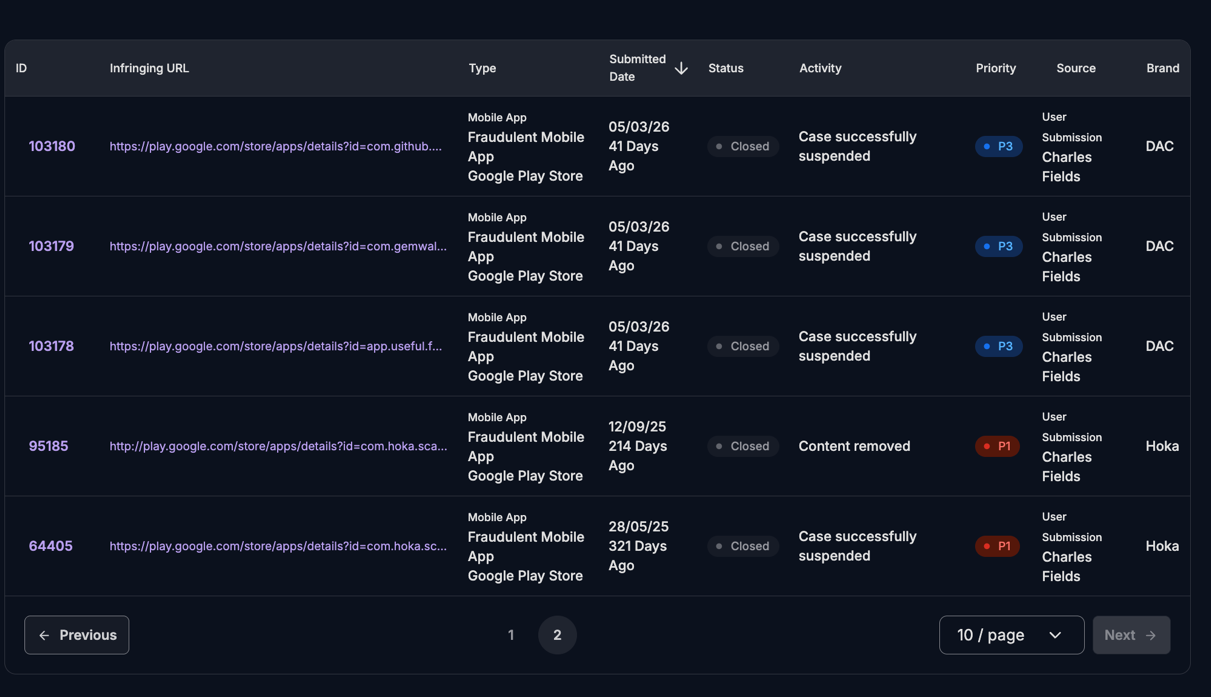
For each app identified, unphish automatically collects and preserves evidence, including app metadata, screenshots, descriptions, developer details, and linked infrastructure. This evidence supports efficient and defensible takedown requests aligned to app store policies.Enforcement actions include
unphish enables rapid enforcement to remove malicious or impersonating apps and disrupt mobile-based fraud targeting your brand and users.
Impersonating
App Removal
Removal of fake or impersonating apps from official app stores
Coordinated App Abuse Disruption
Suspension of developer accounts with repeat abuse
Repeat Developer Enforcement
Disruption of coordinated app based scam campaigns
Priority Scam App Takedowns
Prioritised takedown of apps posing risk to customers
Why mobile app protection matters
Customers expect official apps to be safe and trustworthy. When malicious apps appear alongside legitimate offerings, the risk of fraud, data loss, and reputational damage increases significantly.
unphish helps organisations protect their mobile presence by reducing exposure to fake apps, limiting the lifespan of app based scams, and maintaining confidence in official digital channels.
By extending brand and threat protection into mobile ecosystems, unphish provides a more complete defence against modern, multi channel scam activity.
FAQs
Key questions about how unphish detects, investigates, and disrupts malicious or impersonating mobile apps across app stores.
1. How does unphish detect malicious or impersonating mobile apps?
2. What happens after a malicious app is identified?
3. Can unphish handle large scale or coordinated app abuse?
4. Which app stores and mobile platforms are monitored?
Stop Fake Apps Before They Harm Your Users
Detect and remove impersonating or fraudulent mobile apps targeting your brand across major app stores and mobile platforms.