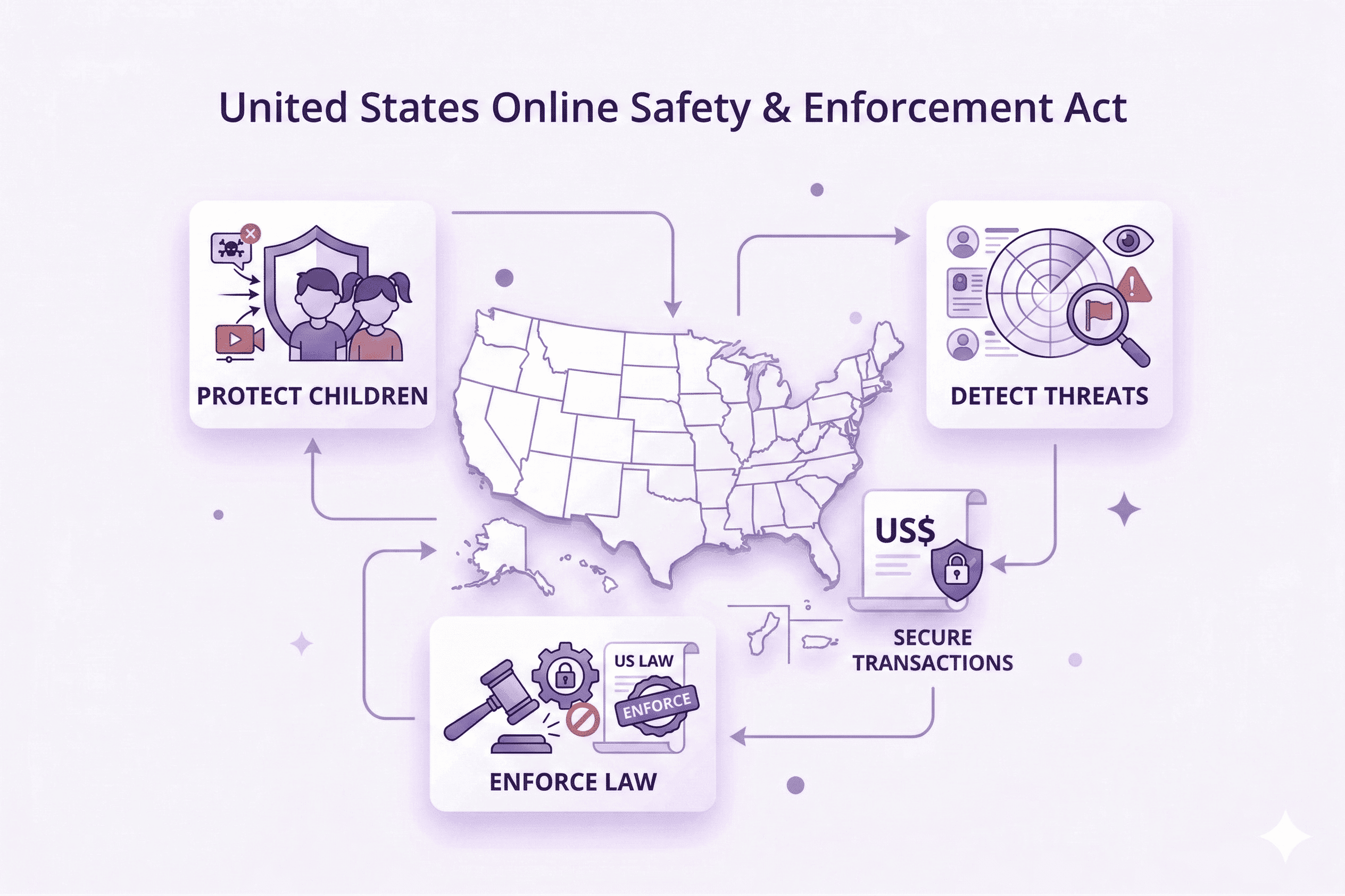
United States – Online Safety & Enforcement Landscape
Understanding the fragmented but rapidly evolving US enforcement approach to impersonation, scams, and unlawful communications . And how organisations can operationalise protection with confidence.
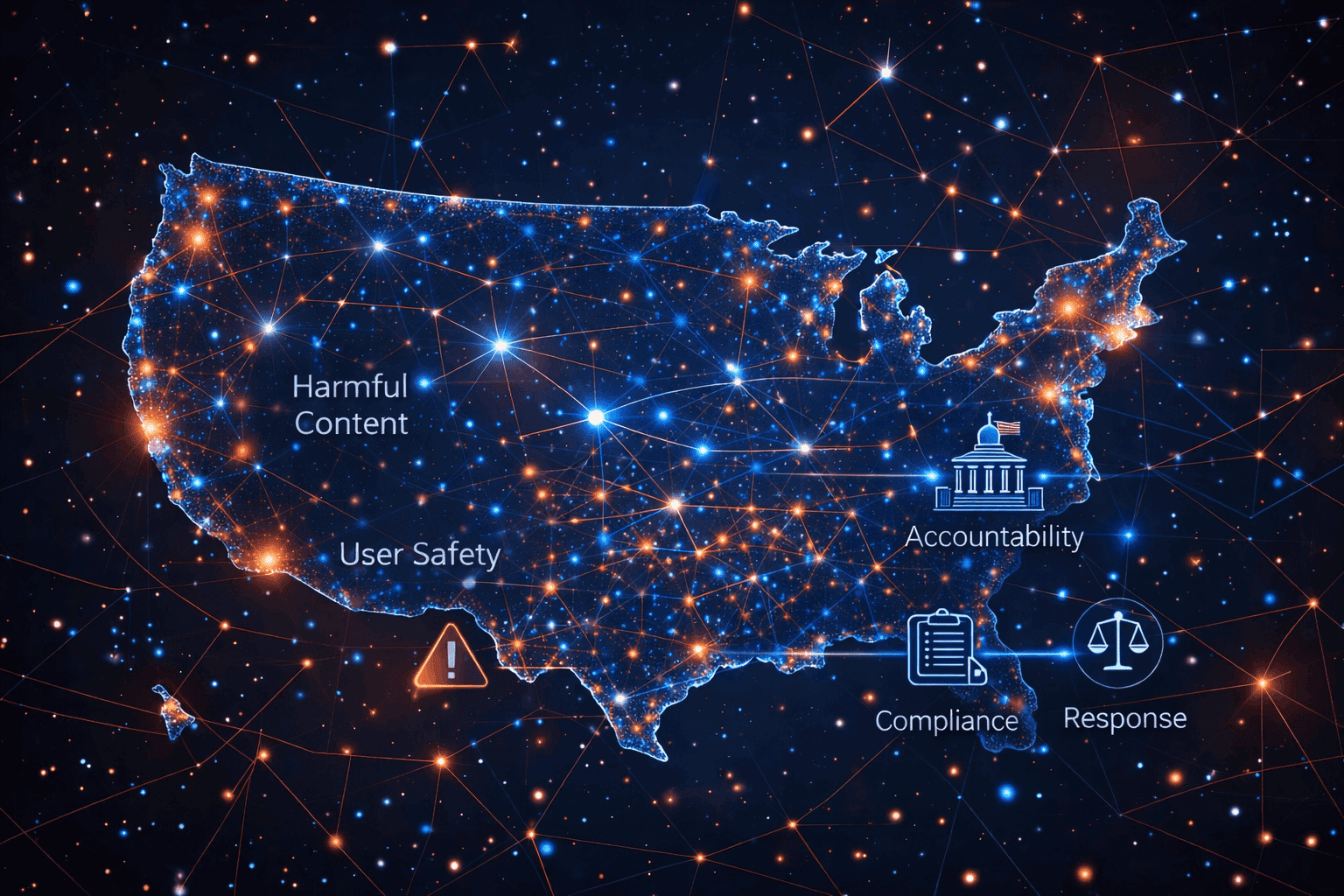
A Fragmented but Strengthening Enforcement Framework
The United States does not operate under a single unified online safety statute equivalent to the Digital Services Act or the UK Online Safety Act. Instead, enforcement is distributed across multiple regulatory bodies, with a strong focus on consumer protection, fraud prevention, and unlawful communications.
Regulatory momentum is increasingly directed toward addressing the underlying behaviours that enable scams and impersonation. This includes targeted rulemaking, enforcement actions, and cross-agency collaboration designed to disrupt fraudulent infrastructure and protect consumers at scale.
Key Enforcement Priorities in the United States
US regulators are intensifying action against impersonation, scam delivery mechanisms, and deceptive communications through coordinated enforcement and rulemaking.
Impersonation Enforcement (FTC)
Clear prohibition of impersonating government entities, businesses, or their representatives, with enforcement mechanisms targeting fraud at its source.
Scam Infrastructure Disruption
Increased focus on identifying and dismantling the digital infrastructure used to facilitate scams and deceptive campaigns.
Robocall & Robotext Regulation (FCC)
Expanded rules and initiatives aimed at reducing illegal robocalls and smishing, including stronger blocking capabilities.
Caller ID Authentication & Spoofing Controls
Regulatory efforts to combat caller ID spoofing and deceptive identity masking in communications.
Consumer Protection Enforcement
Heightened enforcement actions targeting unfair or deceptive practices impacting consumers across digital channels.
Cross-Agency Coordination
Collaboration between regulatory bodies to improve enforcement efficiency and address evolving fraud patterns.
What This Means for Organisations
Organisations operating in the US must navigate a multi-layered enforcement environment that increasingly prioritises proactive detection and disruption of scam activity.
-
Continuous monitoring for impersonation across web, messaging, and communication channels.
-
Rapid identification and takedown of scam infrastructure targeting consumers.
-
Alignment with telecom and regulatory reporting frameworks for smishing and robocalls.
-
Evidence collection to support enforcement actions and regulatory escalations.
-
Ongoing intelligence to track repeat offenders and infrastructure reuse.
Core Operational Requirements in the US Landscape
Monitoring & Detection
Continuous identification of impersonation, scam campaigns, and fraudulent communication channels.
Risk Assessment & Prioritisation
Evaluation of threats based on consumer impact, scale, and regulatory relevance.
Enforcement & Disruption
Execution of takedowns across domains, hosting providers, and communication channels.
Audit & Evidence Management
Structured evidence capture to support legal escalation and enforcement actions.
Intelligence & Pattern Detection
Analysis of repeat offenders, infrastructure reuse, and evolving scam tactics.
Regulatory Reporting Readiness
Preparedness to support reporting obligations across FTC, FCC, and partner ecosystems.
How unphish Aligns with the US Enforcement Model
unphish enables practical disruption of scam ecosystems while supporting enforcement, legal escalation, and consumer protection objectives.
Continuous Detection of Impersonation Infrastructure
Detection and takedown of impersonation websites, scam landing pages, and brand abuse infrastructure aligned with FTC enforcement priorities.
Smishing & Communication Scam Disruption
Referral-driven workflows supporting telco ecosystems and enterprise reporting pipelines for text-based scam campaigns.
Enforcement-Ready Evidence Capture
Structured evidence collection designed for escalation, enforcement actions, and legal proceedings.
Threat Intelligence & Repeat Offender Mapping
Identification of infrastructure reuse and coordinated campaigns to enable consistent disruption of scam networks.
