Phishing Protection
unphish quickly detects phishing and automatically removes it, protecting your business from customer harm, financial loss, and reputational damage.
Disrupt Phishing Infrastructure Before It Impacts Your Users
Phishing remains one of the most persistent digital threats facing organisations. Attackers impersonate brands, executives, and trusted communications to capture credentials, financial data, and sensitive information.
Modern campaigns are automated and infrastructure-driven. Domains are rapidly registered, websites cloned, and lures distributed across multiple channels. unphish focuses on identifying and dismantling the infrastructure that enables these campaigns.
Why Phishing Protection Is Essential for Every Brand
Phishing campaigns exploit trust, speed, and brand recognition.
Customer Fraud
Credential harvesting and payment diversion directly impact customers and erode long term brand trust.
Brand Impersonation
Lookalike domains and cloned login pages misuse brand assets to deceive victims into sharing sensitive information.
Reputational & Regulatory Risk
Delayed disruption increases fraud losses, heightens regulatory scrutiny, and creates sustained operational strain across security and fraud teams.
How Modern Phishing Campaigns Operate
Phishing operations are multi-channel and short-lived.
Attackers deploy lookalike domains, cloned login pages, and brand misuse across email, SMS, messaging platforms, social media, and search advertising. Infrastructure is frequently rotated to evade detection.
This creates ongoing exposure where customers and employees are targeted before traditional controls respond.

How unphish Reduces Phishing Exposure at Scale
Detection
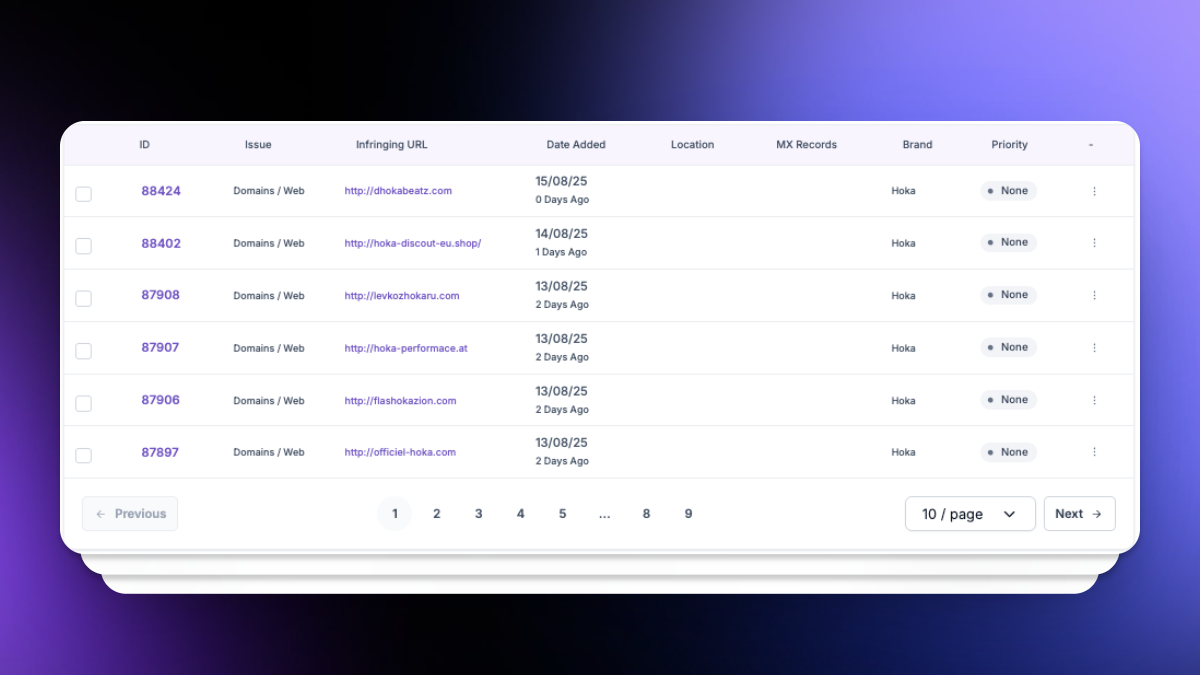
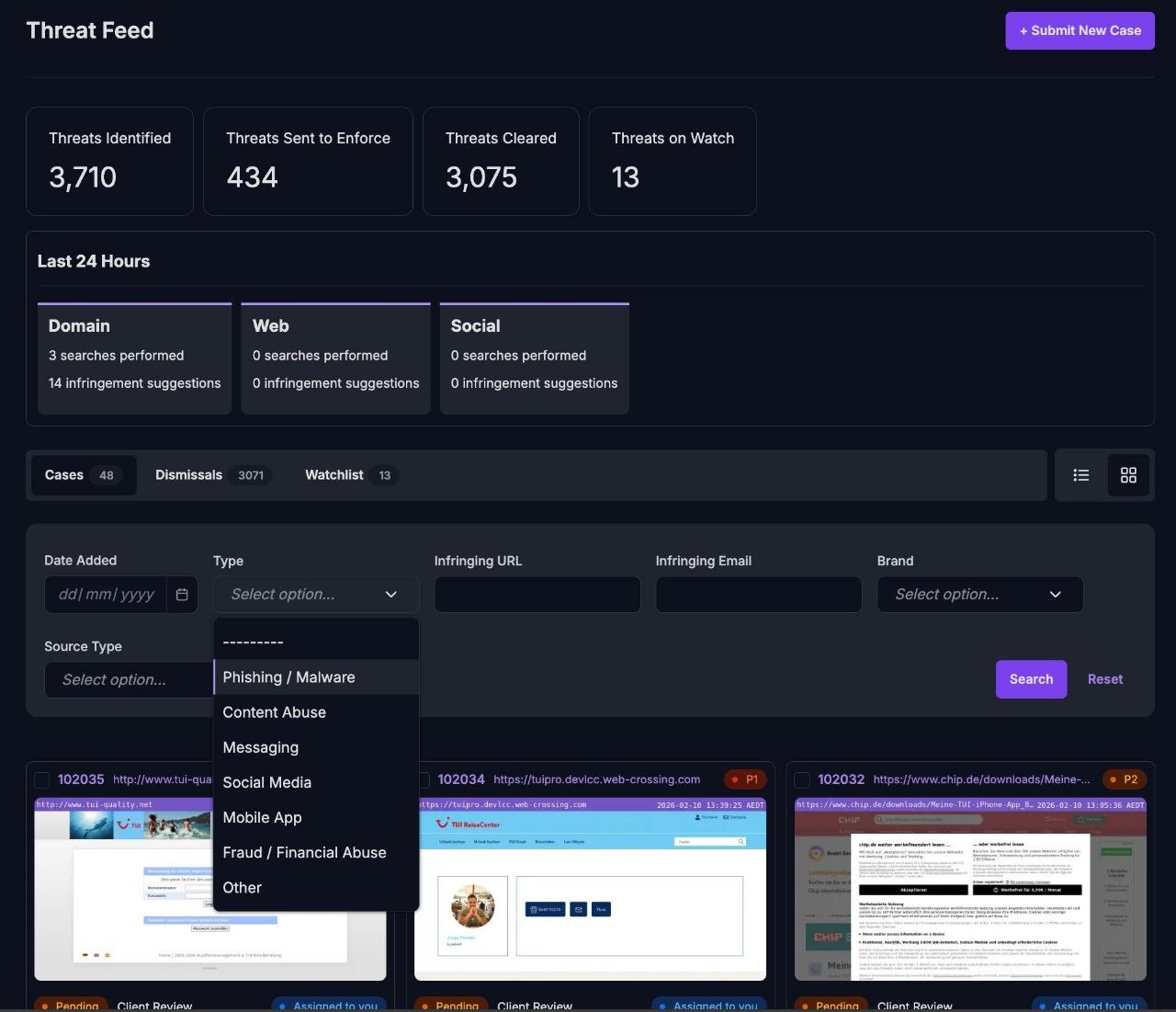
unphish continuously monitors the internet for phishing activity targeting your brand, products, executives, and digital assets. Automated analysis is combined with intelligence-led techniques to identify malicious domains, cloned websites, and active campaign infrastructure early, before exposure escalates.
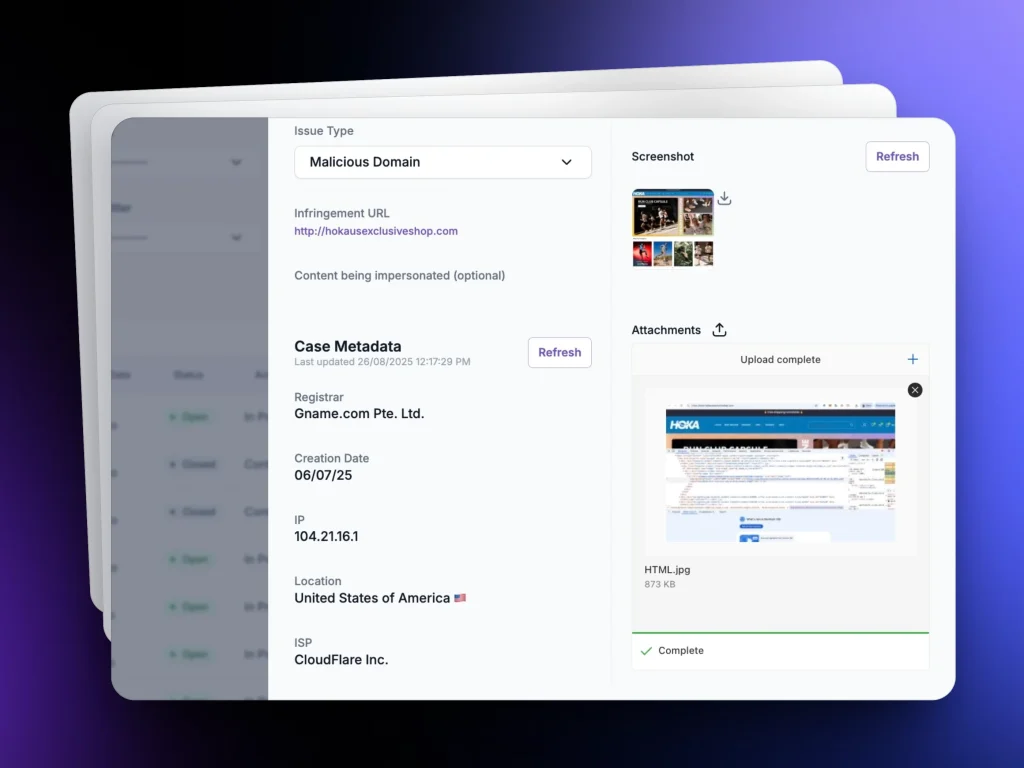
Evidence
For every confirmed phishing threat, unphish automatically generates a complete, platform-ready evidence pack. Screenshots, source data, hosting intelligence, and registrar details are captured and structured to meet enforcement requirements, reducing preparation time and manual effort.
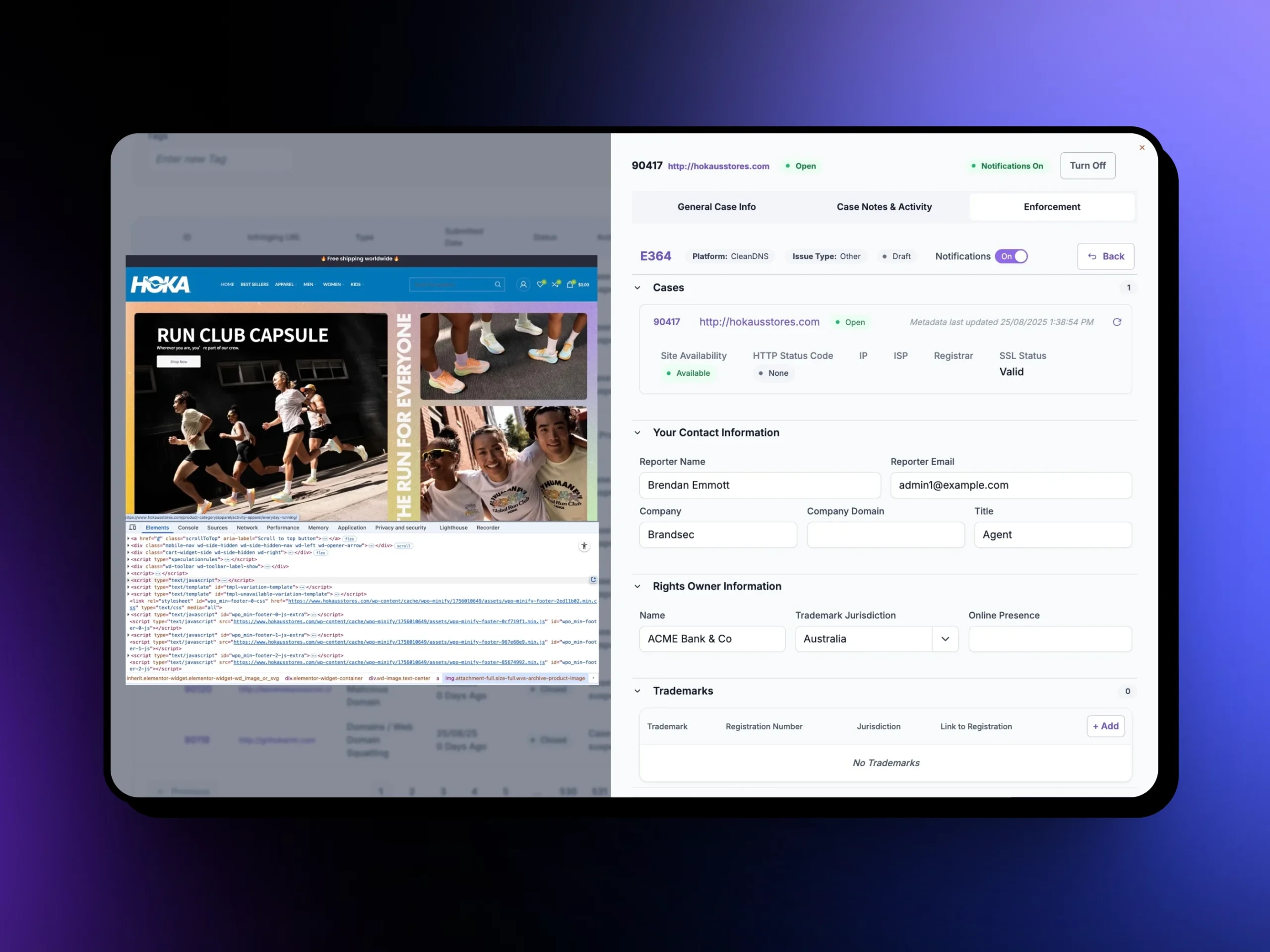
Takedown
Enforcement is built directly into the platform. Using established escalation pathways, unphish coordinates takedown actions across registrars, hosting providers, content delivery networks (CDN), and online platforms, disrupting phishing campaigns quickly and at scale.
Verification
After enforcement, unphish validates removal and continues monitoring for campaign rebuilds or re-registration attempts. This ongoing verification limits repeat abuse and reduces the likelihood of attackers reusing the same infrastructure.
Core Capabilities of unphish Phishing Protection
Intelligent Threat Detection
Identify phishing domains, cloned websites, and impersonation infrastructure using automated analysis combined with intelligence-led validation.
Integrated Takedown Engine
Accelerate disruption with built-in enforcement workflows that coordinate action across registrars, hosting providers, and online platforms.
Structured Evidence Collection
Automatically generate enforcement-ready evidence including screenshots, registrar data, hosting intelligence, and network indicators.
Global Infrastructure Coverage
Monitor phishing activity across domains, hosting environments, content delivery networks, and social platforms worldwide.
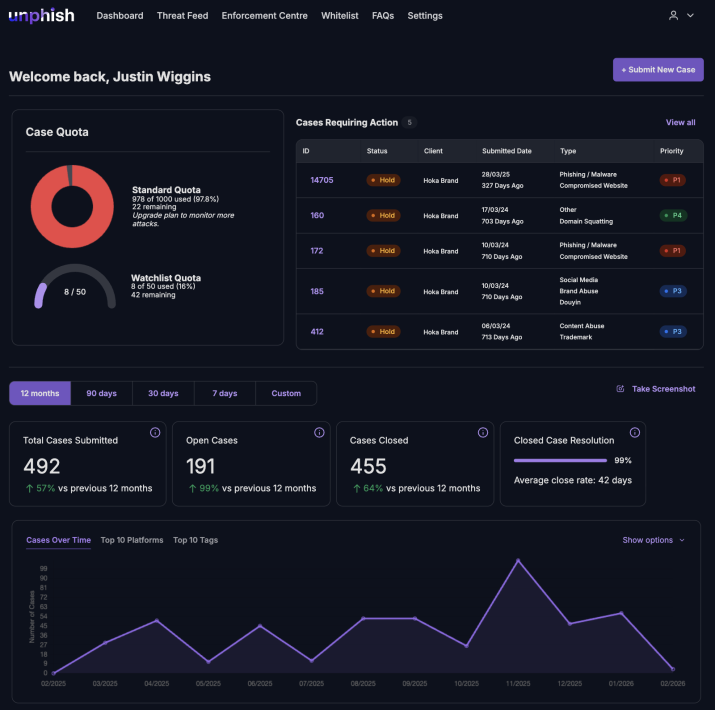
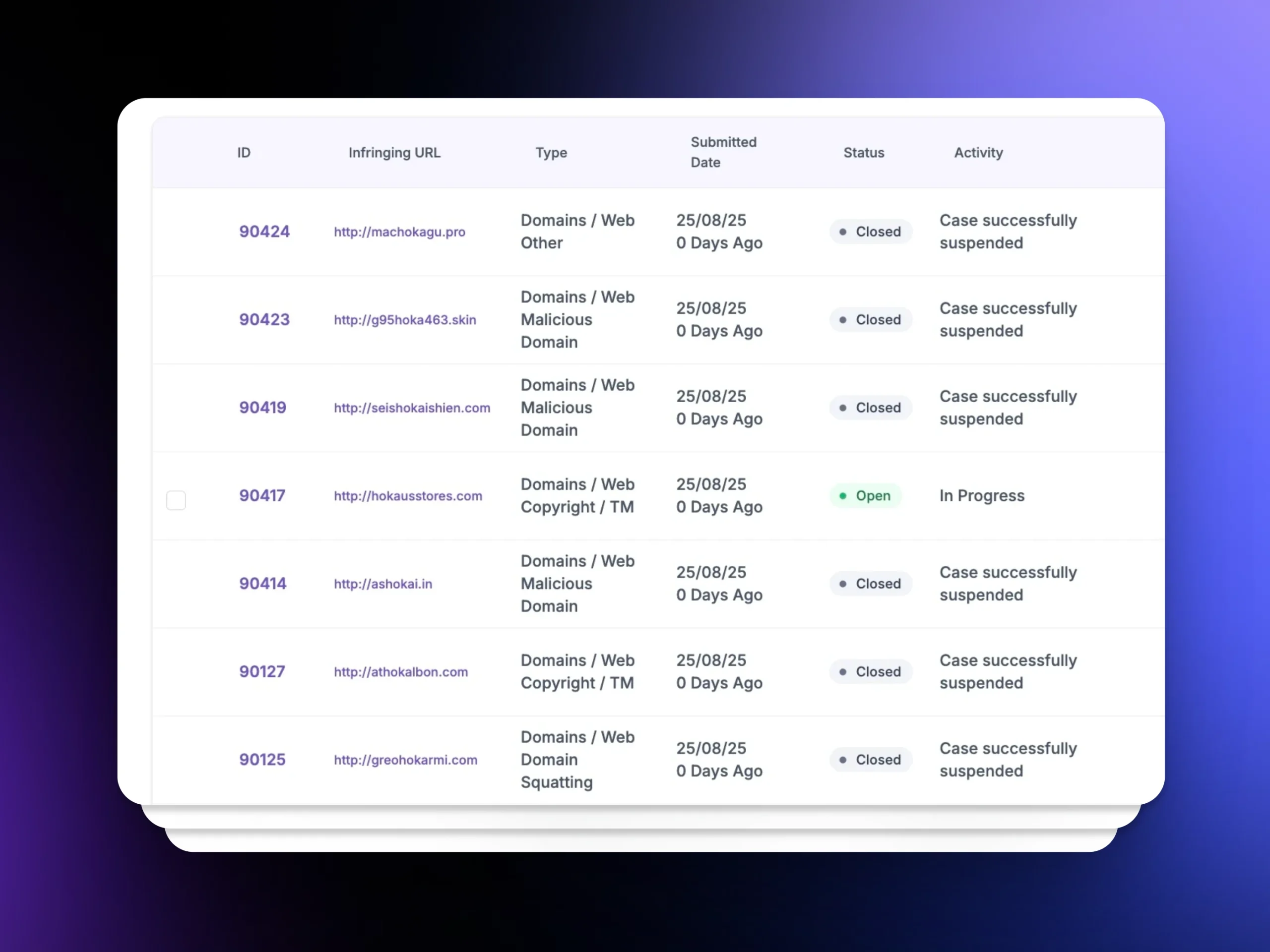
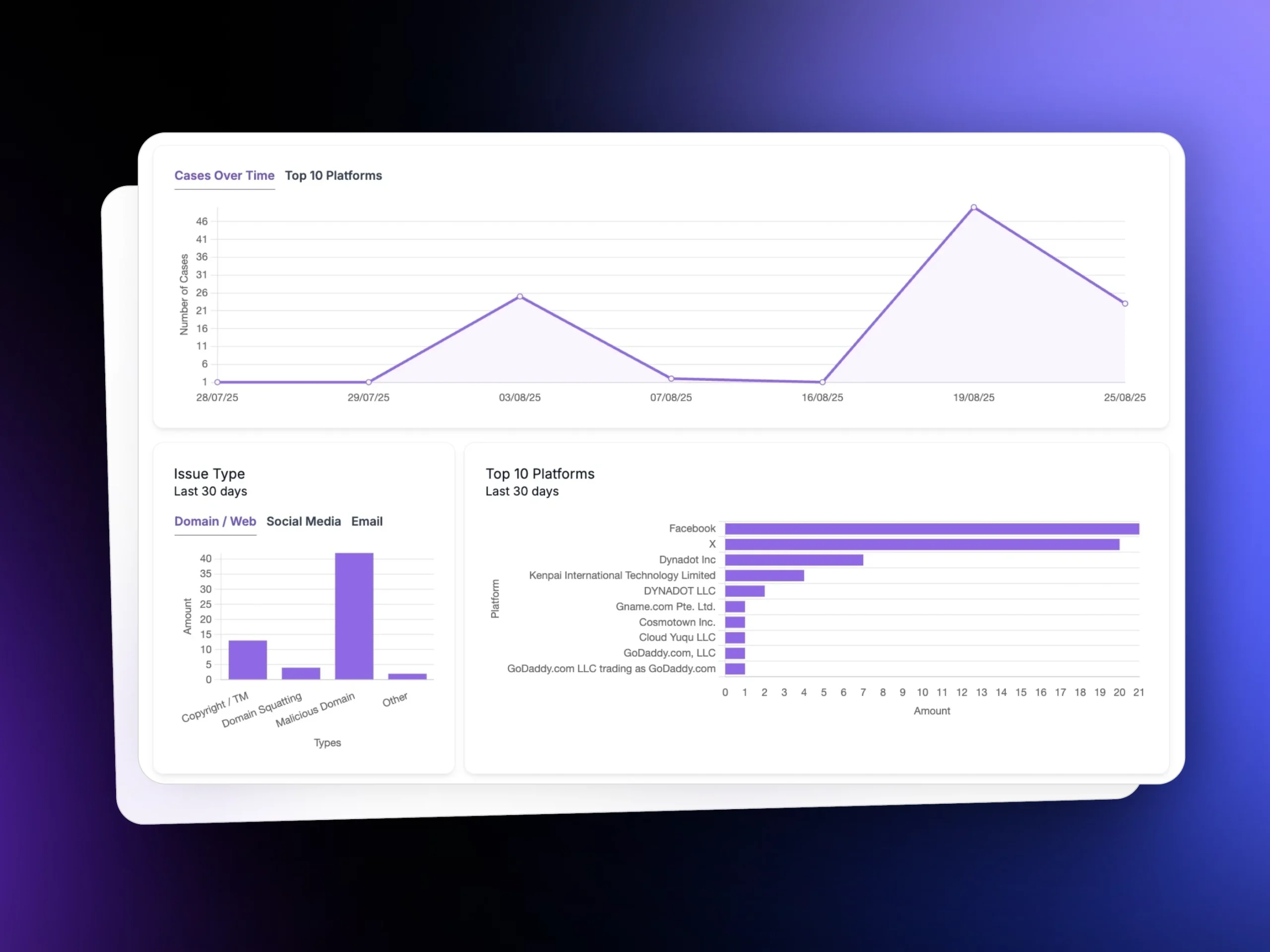
Operational Dashboard
Gain real-time visibility into active threats, enforcement progress, exposure windows, and disruption outcomes.
Audit and Compliance Reporting
Produce structured reports that demonstrate mitigation efforts, enforcement timelines, and measurable risk reduction.
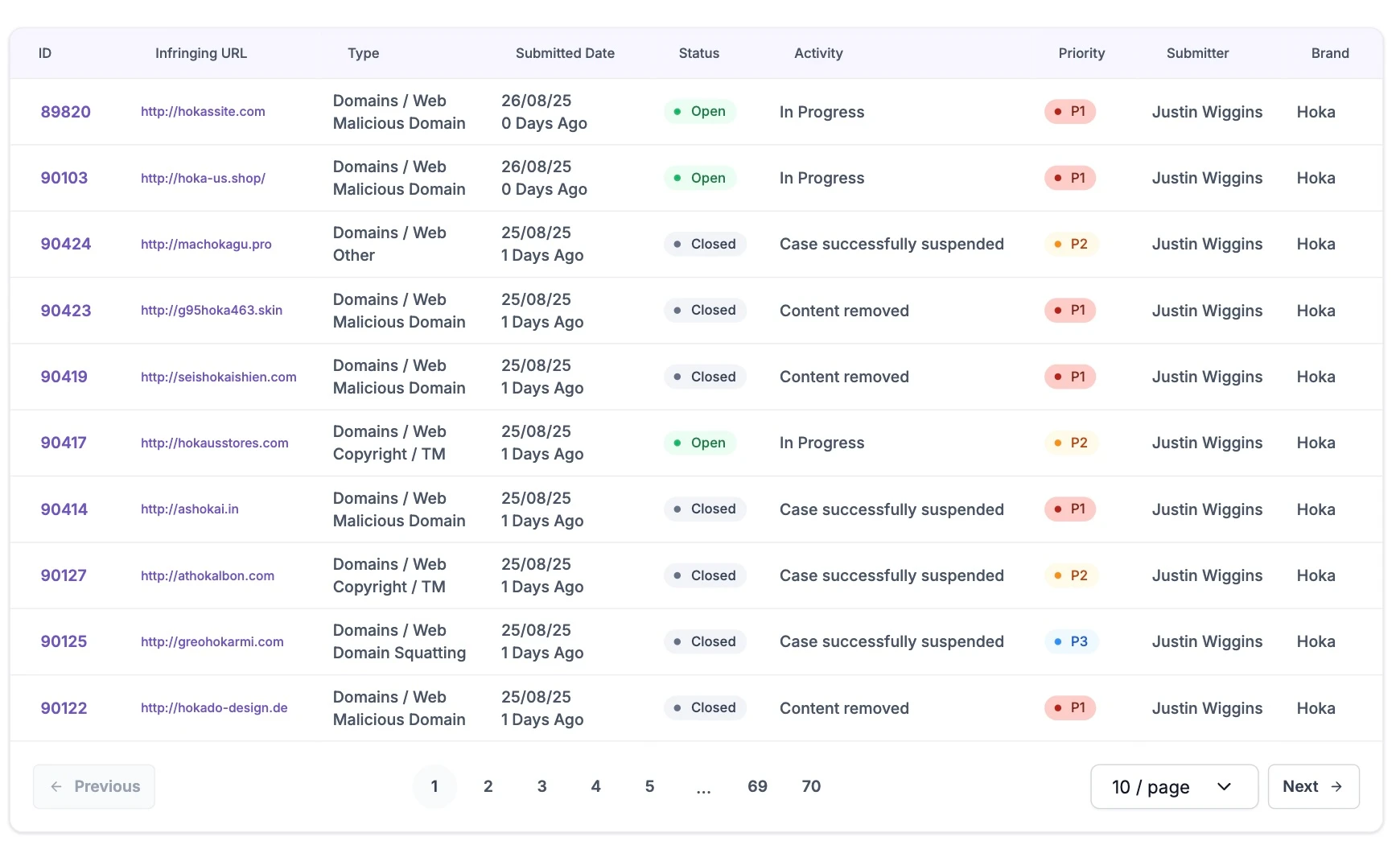
Phishing Detection and Takedown in Practice
Explore how unphish detects active phishing campaigns, generates enforcement-ready evidence, and drives takedown actions through a single operational workflow. View live dashboards, case progression, and measurable disruption outcomes in real time.
Why Customers Choose unphish
| unphish | Fragmented / Reactive Approach | |
| Threat Visibility | Continuous monitoring across domains, hosting, social platforms, and attacker infrastructure. | Limited visibility based on complaints or isolated alerts. |
| Detection Speed | Automated detection and risk scoring identify threats early. | Threats are discovered late, often after impact. |
| Infrastructure Insight | Deep analysis reveals campaign links, infrastructure reuse, and attacker patterns. | Little or no visibility into shared infrastructure or repeat activity. |
| Enforcement Execution | Coordinated workflows enable faster, consistent takedown across platforms. | Manual submissions slow down response and create inconsistent outcomes. |
| Verification & Control | Automated validation confirms removal and tracks reappearance. | No structured verification or monitoring after takedown. |
| Operational Visibility | Unified dashboards provide clear status, timelines, and reporting. | Siloed tools limit visibility and create operational gaps. |
FAQs
Everything you need to know about how unphish detects, mitigates, and tracks phishing threats.
1. How quickly can phishing sites be removed?
2. Does unphish rely on end user reporting?
3. Can enforcement be prioritised?
4. How does unphish reduce repeat phishing campaigns?
Disrupt Phishing Campaigns Before They Scale
Phishing threats move fast. unphish detects, validates, and takes down malicious infrastructure before attackers reach your customers – all through a single automated workflow.