VIP / Executive Impersonation
Detect and disrupt scams where attackers impersonate executives to pressure employees into sending payments or sensitive data.
Executive Impersonation Threats
VIP and executive impersonation is a targeted form of fraud where attackers pose as senior leaders, board members, or high profile individuals to manipulate trust and authority. These scams are designed to bypass controls, accelerate decision making, and extract payments or sensitive information under the guise of urgency or confidentiality.
Because these attacks exploit organisational hierarchy and human behaviour rather than technical weaknesses, they are often highly effective and difficult to detect before damage occurs.
unphish helps organisations identify and disrupt executive impersonation by targeting the digital infrastructure and impersonation assets used to support these campaigns.How executive impersonation scams operate
Executive impersonation commonly appears in business email compromise, messaging platform abuse, social media impersonation, and voice based scams. Attackers study public information, reporting lines, and communication styles to appear credible. Typical tactics include:
High-Volume SMS Campaigns
Emails or messages requesting urgent payments or changes to bank details.
Impersonation Voice Calls
Impersonation of executives on messaging platforms to pressure finance or operations teams.
Rapid Infrastructure Rotation
Fake social media profiles posing as senior leaders engaging with employees or partners.
Phishing and Fraud Redirection
Vishing attacks using executive names to legitimise fraudulent requests.
How unphish detects executive impersonation
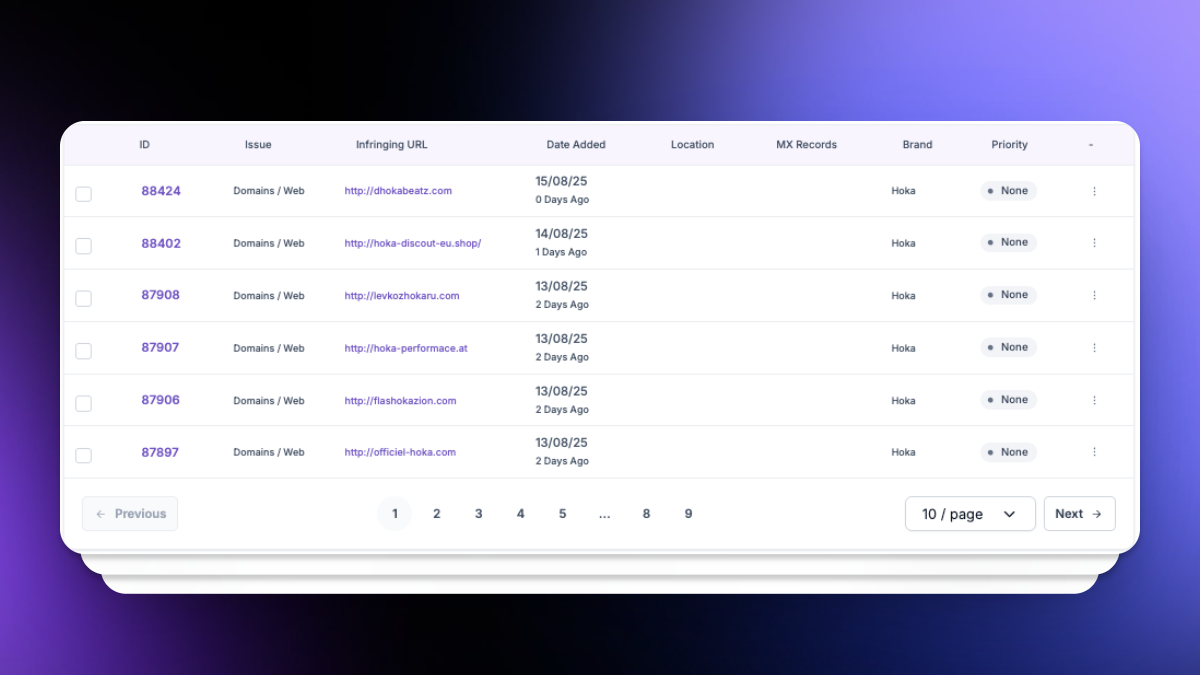
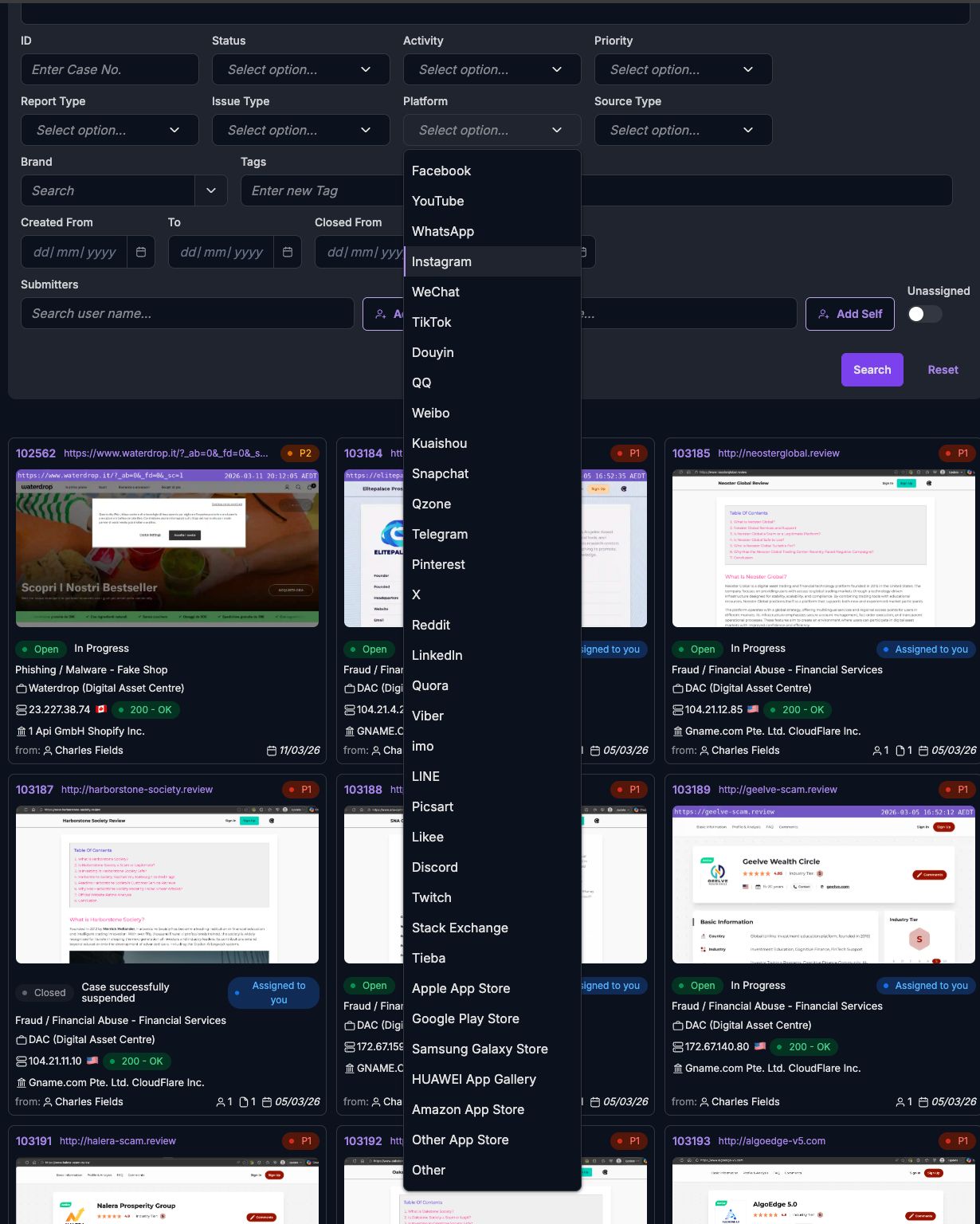
unphish monitors for unauthorised use of executive and VIP identities across domains, websites, and online platforms. Detection is driven by a combination of automated analysis and intelligence correlation, including:
Reported Scam SMS and Phone Numbers
Internal Fraud and Security Intelligence
Leveraging computational vision and pattern matching to detect deepfakes and images of key persons.
Partner Intelligence Monitoring
Detection of impersonation profiles on social media and messaging platforms.
Executive Impersonation Infrastructure Tracking
Monitoring for phishing pages and scam content referencing executives or senior leaders.
Why Customers Choose unphish
| unphish | Fragmented / Reactive Approach | |
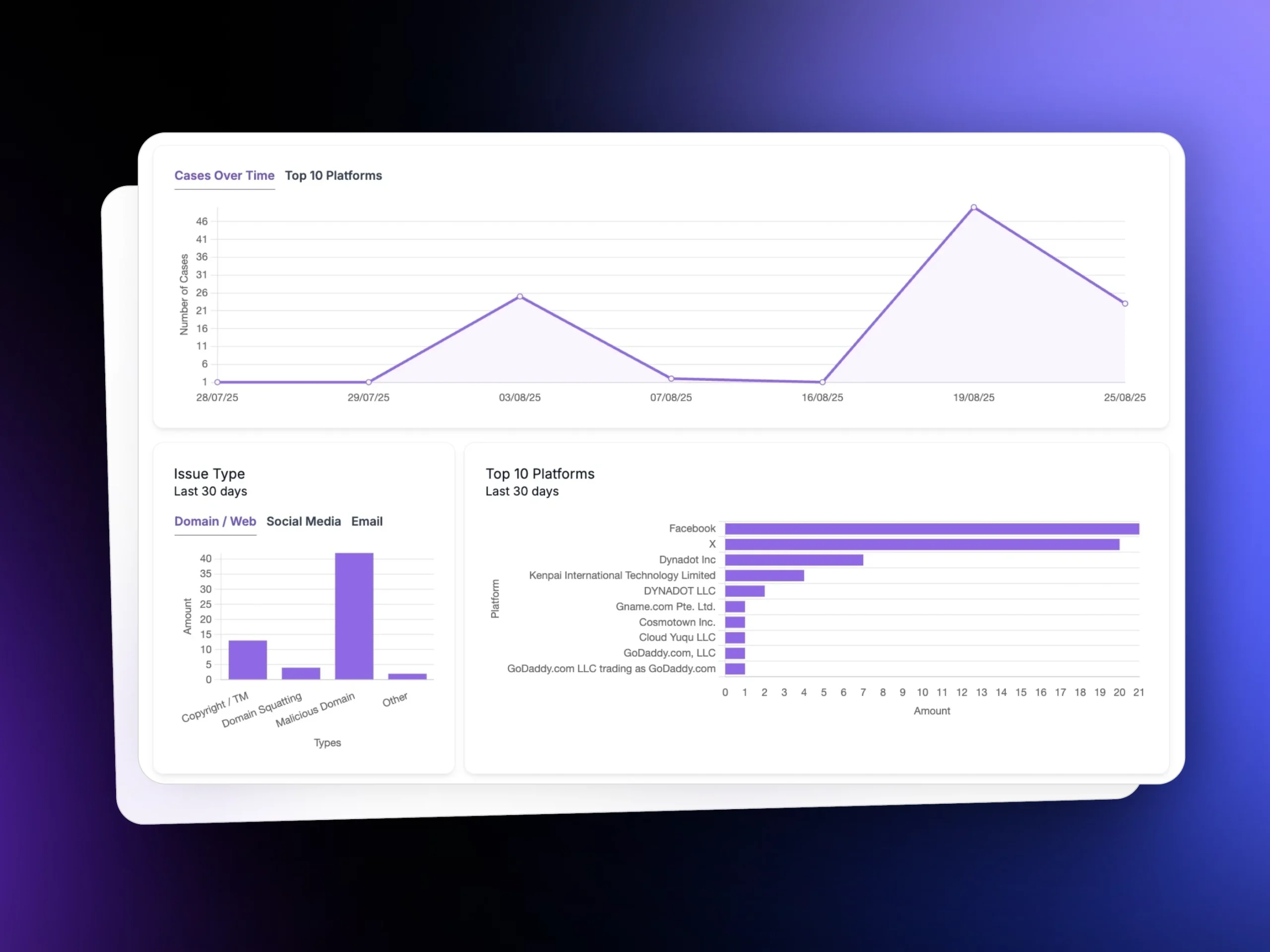
| Threat Visibility | Continuous monitoring across domains, hosting, social platforms, and attacker infrastructure. | Limited visibility based on complaints or isolated alerts. |
| Detection Speed | Automated detection and risk scoring identify threats early. | Threats are discovered late, often after impact. |
| Infrastructure Insight | Deep analysis reveals campaign links, infrastructure reuse, and attacker patterns. | Little or no visibility into shared infrastructure or repeat activity. |
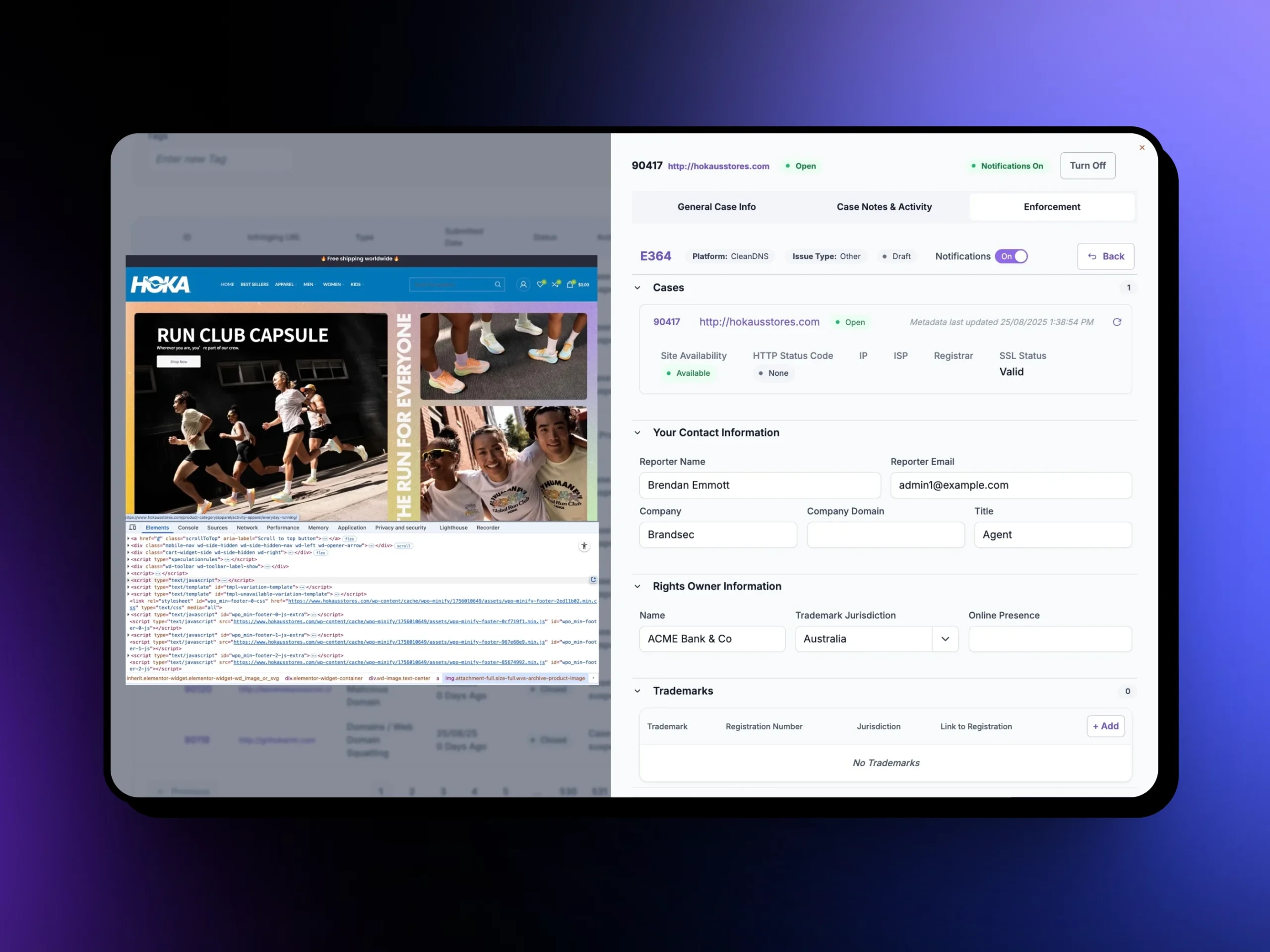
| Enforcement Execution | Coordinated workflows enable faster, consistent takedown across platforms. | Manual submissions slow down response and create inconsistent outcomes. |
| Verification & Control | Automated validation confirms removal and tracks reappearance. | No structured verification or monitoring after takedown. |
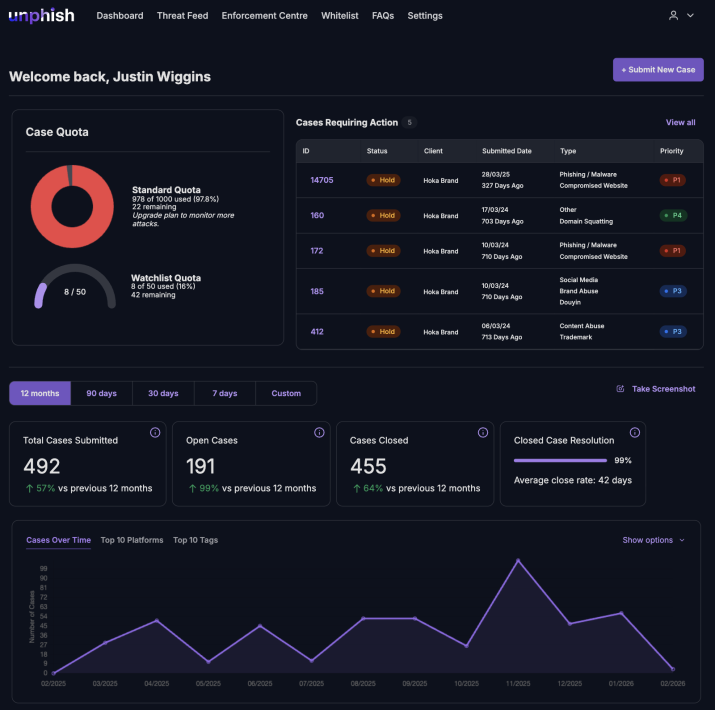
| Operational Visibility | Unified dashboards provide clear status, timelines, and reporting. | Siloed tools limit visibility and create operational gaps. |
How unphish enforces and disrupts executive impersonation
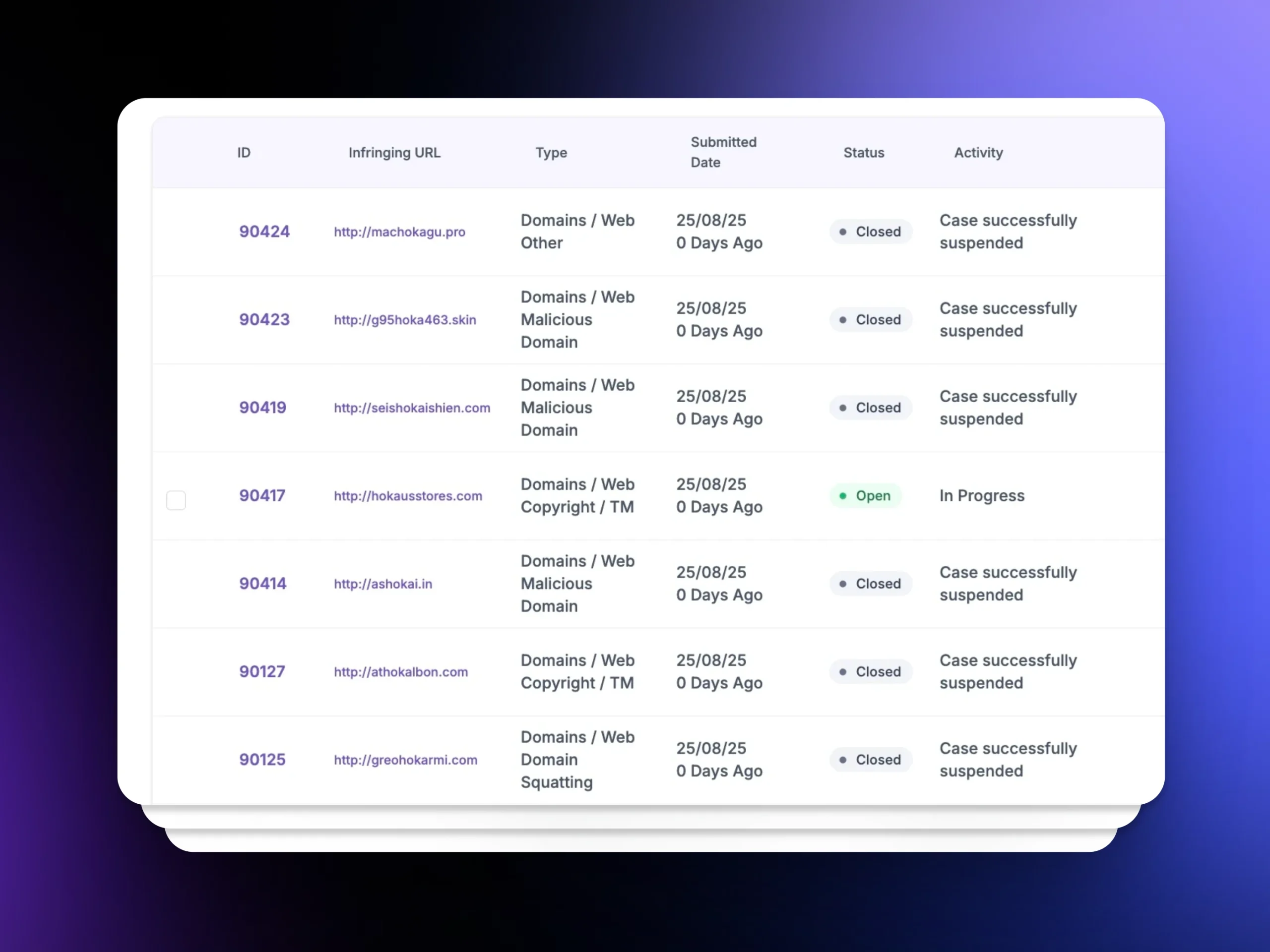
unphish integrates enforcement directly into the platform to support rapid takedown of impersonation assets.
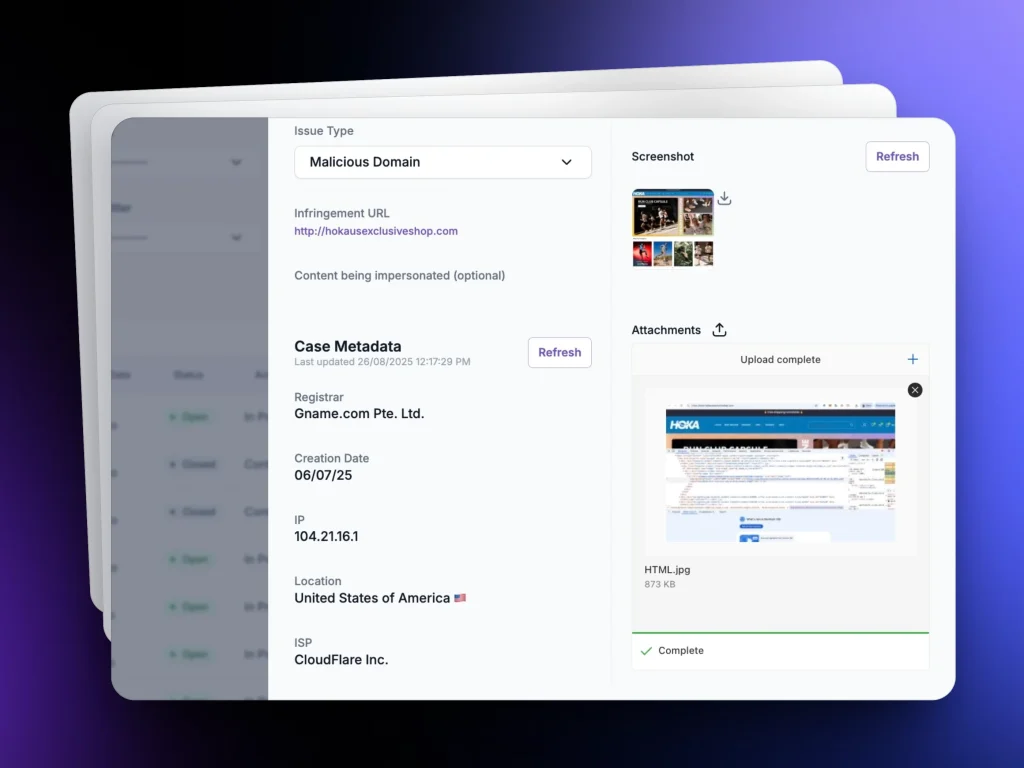
For each incident, unphish automatically captures evidence such as impersonation profiles, websites, message content, domains, and hosting details. This evidence supports fast, defensible enforcement actions aligned to platform and provider policies.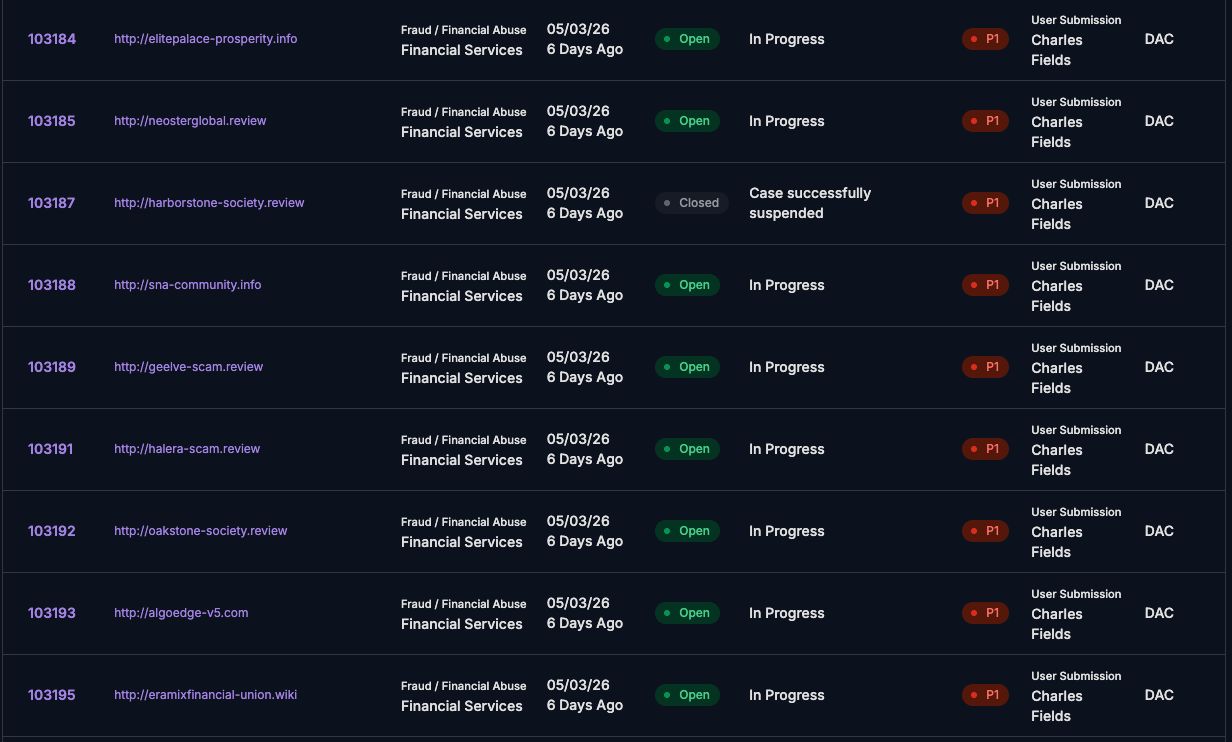
Enforcement actions include
unphish enables rapid enforcement to disrupt VIP / Executive Impersonation campaigns and remove supporting scam infrastructure.
Fake Profile and Account Removal
Removal of fake social media and messaging platform profiles
Impersonation Website Takedowns
Takedown of phishing websites impersonating executives or leadership teams
Scam Numbers and Domains Disabled
Suspension of domains and infrastructure used in impersonation campaigns
Repeat Campaign Disruption
Disruption of repeat campaigns by identifying shared infrastructure and patterns
Why executive impersonation protection matters
Executive impersonation can result in significant financial loss, regulatory exposure, and internal trust issues. Even failed attempts can undermine confidence in leadership communications.
unphish helps organisations reduce this risk by limiting the ability for attackers to convincingly impersonate executives online, protecting employees and partners from manipulation, and providing clear oversight of enforcement activity.
By addressing executive impersonation as a digital threat rather than a one off incident, unphish strengthens organisational resilience against targeted, high impact scams.

FAQs
Common questions about how unphish detects, investigates, and disrupts executive impersonation scams.
1. How does unphish detect executive impersonation attacks?
2. What happens after an executive impersonation campaign is identified?
3. Can unphish handle coordinated or large-scale impersonation campaigns?
4. How are executive impersonation campaigns disrupted?
Stop Executive Impersonation Campaigns Faster
Detect and disrupt scams where attackers impersonate executives to pressure employees or customers into sending payments or sensitive information.