Threat Monitoring
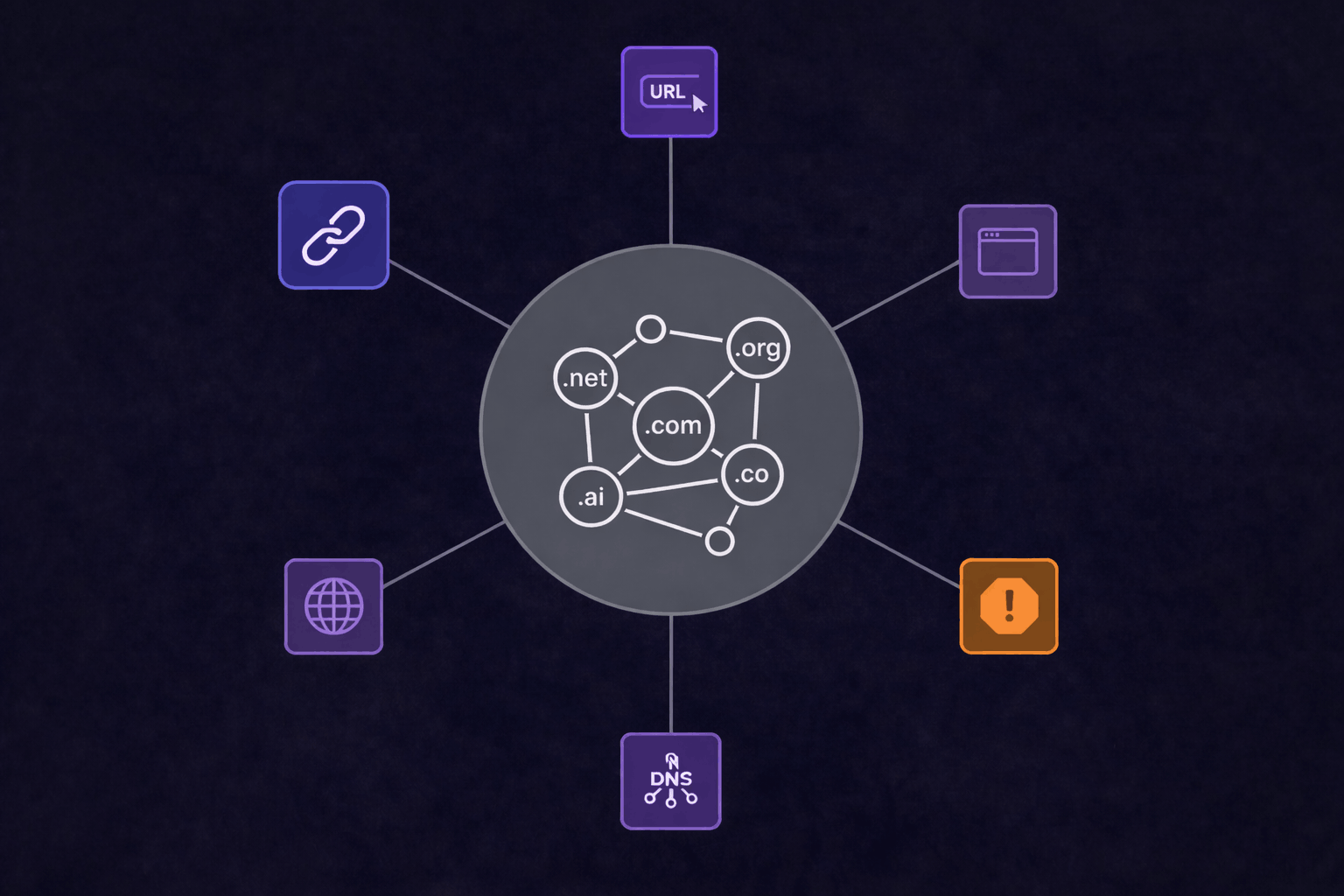
Stay ahead of threats to your brand with real-time monitoring across domains, websites, social media, and apps, so you can detect misuse quickly and take action before damage is done.
Continuous Threat Visibility Across Digital Channels
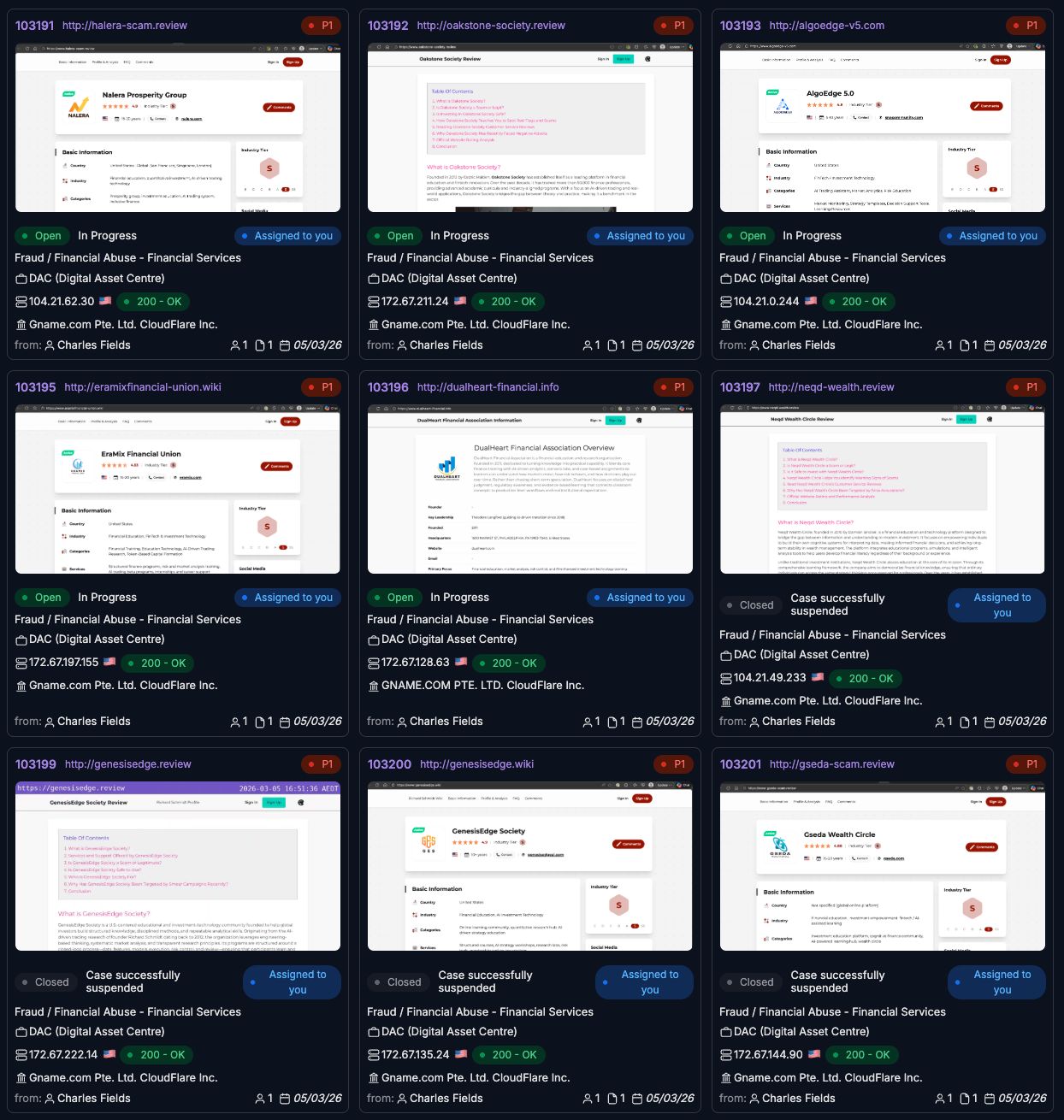
Organisations face threat activity across an ever-expanding digital landscape. Phishing campaigns, domain abuse, impersonation accounts, mobile applications, and brand misuse can emerge in any region, at any time, and on multiple platforms simultaneously.
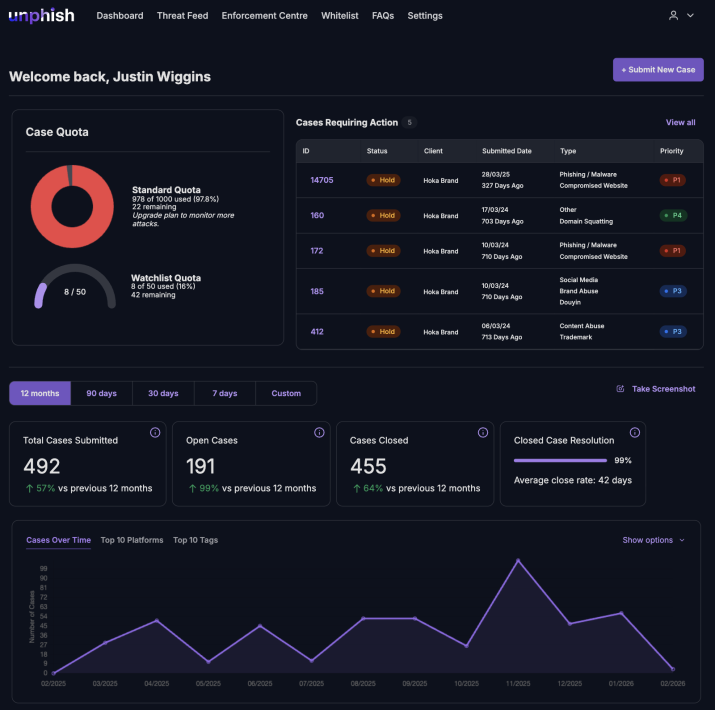
unphish Threat Monitoring provides real-time visibility into malicious activity across digital ecosystems, enabling security teams to detect emerging threats early and act before they impact users or brand reputation.
From Detection to Decisive Action
Monitoring is only effective when it drives action. unphish connects detection to structured investigation and enforcement workflows, transforming threat signals into operational outcomes.
Coordinated Response
Structured case data and validated evidence enable teams to align quickly, reducing friction across security, legal, and enforcement functions.
Faster Time to Action
Automated evidence capture and workflow integration reduce the gap between discovery and disruption.
Informed Decision-Making
Context-rich threat intelligence supports accurate prioritisation and confident response across incident teams.
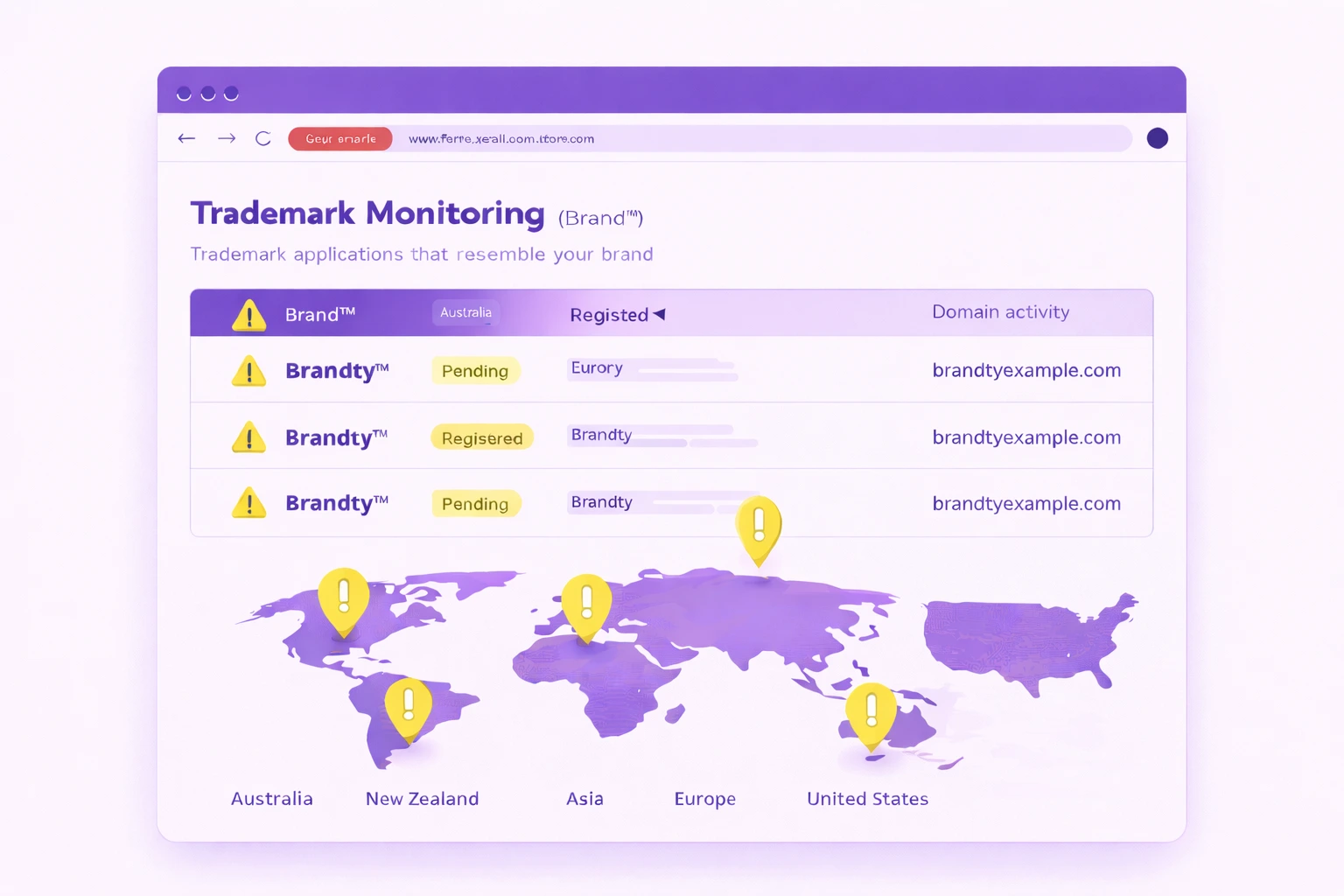
Trademark Monitoring
Monitor trademark registrations worldwide to identify identical or similar filings before they impact your brand. unphish provides early visibility across major jurisdictions, including Australia, New Zealand, Asia, Europe, and the United States, enabling proactive protection strategies.
Track new applications that resemble your brand, monitor competitor filings, and automatically correlate trademark registrations with domain name activity to identify potential abuse at its earliest stage.
Unified Detection and Enforcement
unphish combines monitoring, validation, enforcement, and reporting into a single operational platform. Built for scale and precision, it enables continuous threat visibility and measurable disruption across digital channels.
Why Customers Choose unphish
Trusted when speed and accuracy matter most. unphish replaces manual processes with a structured takedown workflow that reduces exposure and improves response across digital channels.
| unphish | Fragmented / Reactive Approach | |
| Threat Visibility | Continuous monitoring across domains, hosting, social platforms, and attacker infrastructure. | Limited visibility based on complaints or isolated alerts. |
| Detection Speed | Automated detection and risk scoring identify threats early. | Threats are discovered late, often after impact. |
| Infrastructure Insight | Deep analysis reveals campaign links, infrastructure reuse, and attacker patterns. | Little or no visibility into shared infrastructure or repeat activity. |
| Enforcement Execution | Coordinated workflows enable faster, consistent takedown across platforms. | Manual submissions slow down response and create inconsistent outcomes. |
| Verification & Control | Automated validation confirms removal and tracks reappearance. | No structured verification or monitoring after takedown. |
| Operational Visibility | Unified dashboards provide clear status, timelines, and reporting. | Siloed tools limit visibility and create operational gaps. |
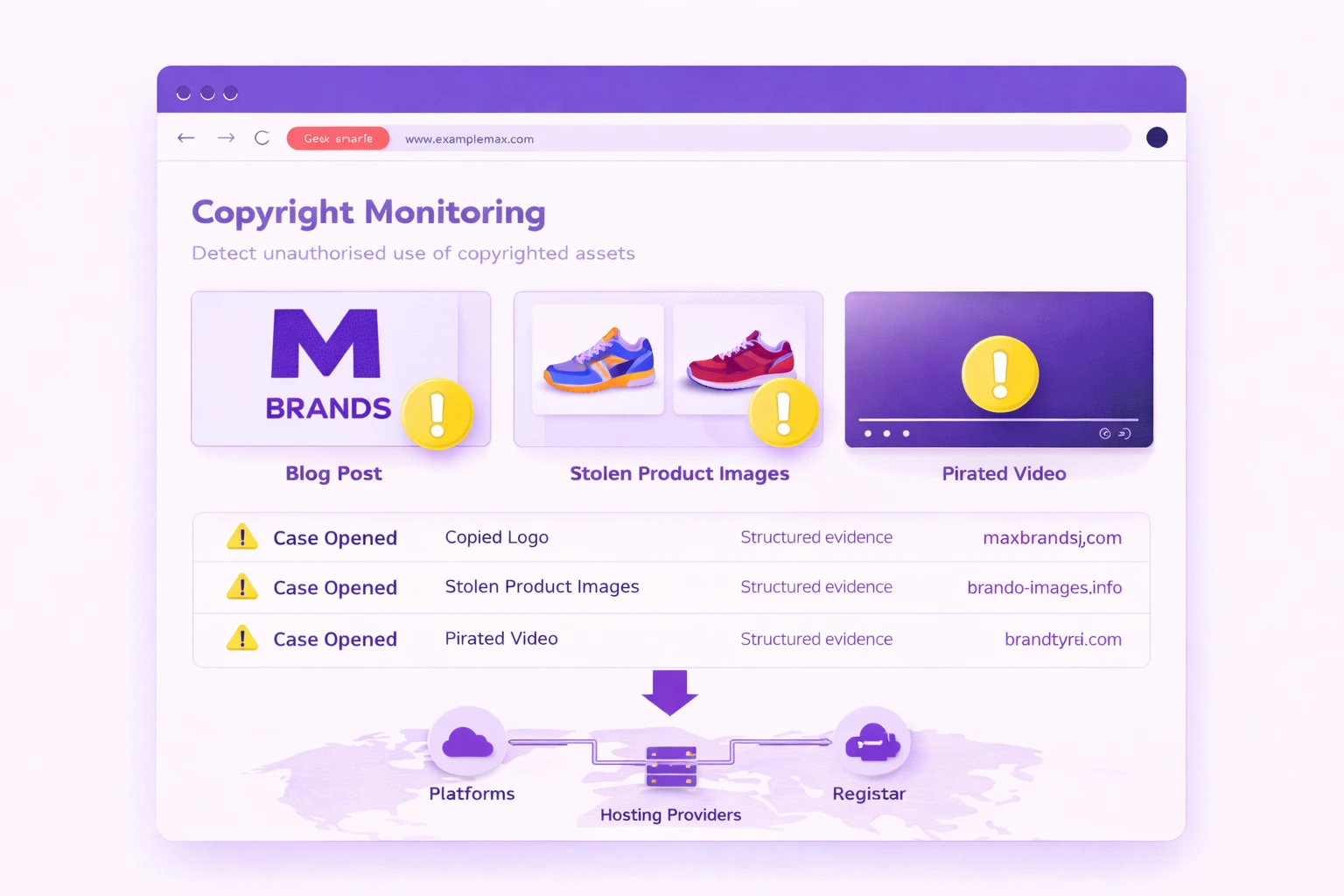
Copyright Monitoring
Detect and document unauthorised use of copyrighted assets, including logos, product imagery, video, and written content across digital channels. Structured evidence collection supports rapid enforcement action with platforms, hosting providers, and registrars, enabling swift removal of malicious or deceptive content and reducing ongoing reputational risk.
Operationalise Your Threat Monitoring