Crypto
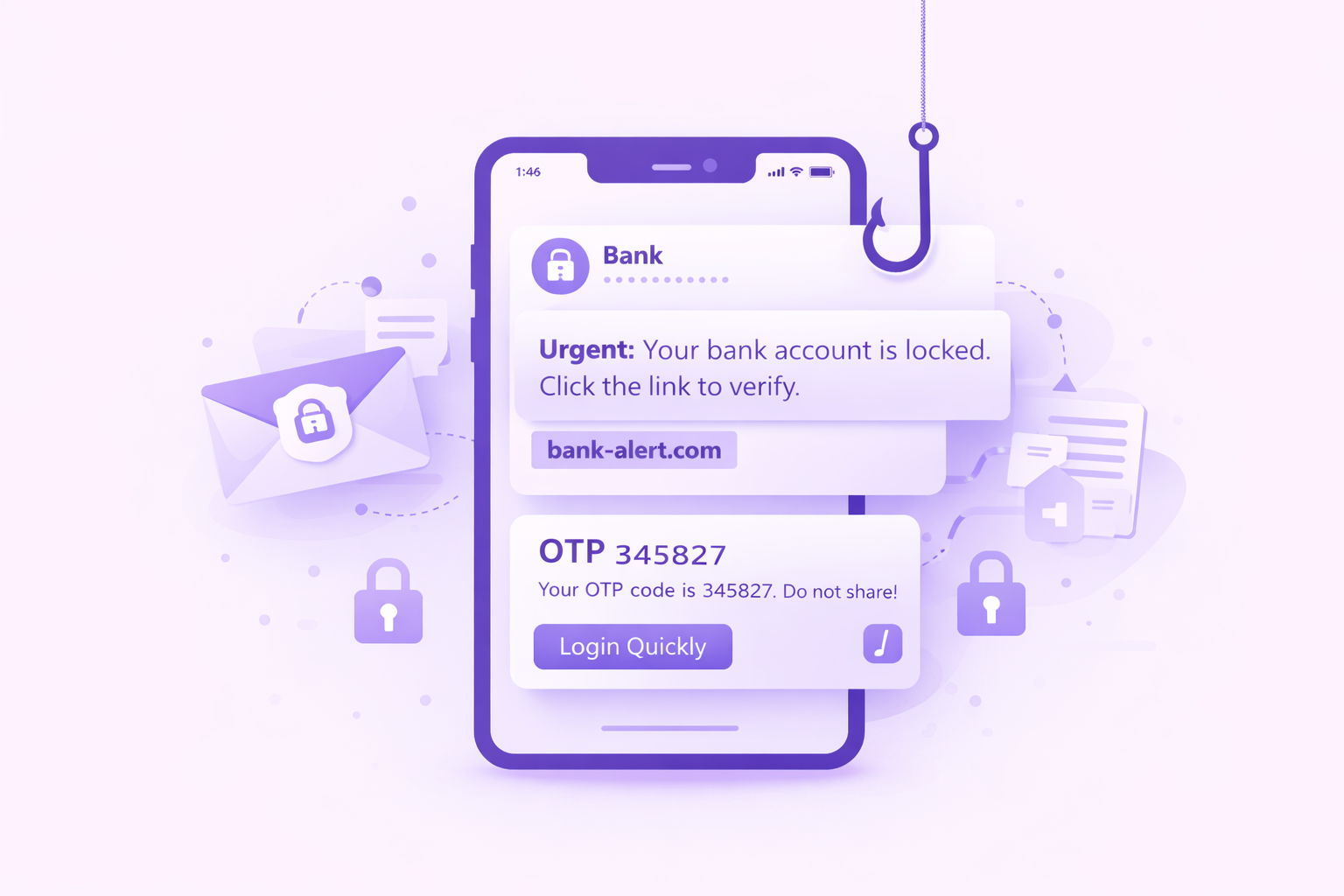
Crypto platforms are high-risk targets due to irreversible transactions and fast markets, with scams including fake exchanges, wallet drainers, impersonation, and fraudulent tokens.
How Crypto Platforms Are Targeted
Crypto platforms are prime targets for scams due to irreversible transactions, high value assets, and fast moving markets. Scammers exploit hype, market volatility, and limited consumer protections.
Common threats include fake exchanges, wallet drainers, impersonated support accounts, investment scams, and fraudulent token launches.
Typical Scam Activity in Crypto Platforms

Key Capabilities for Banking and Financial Services
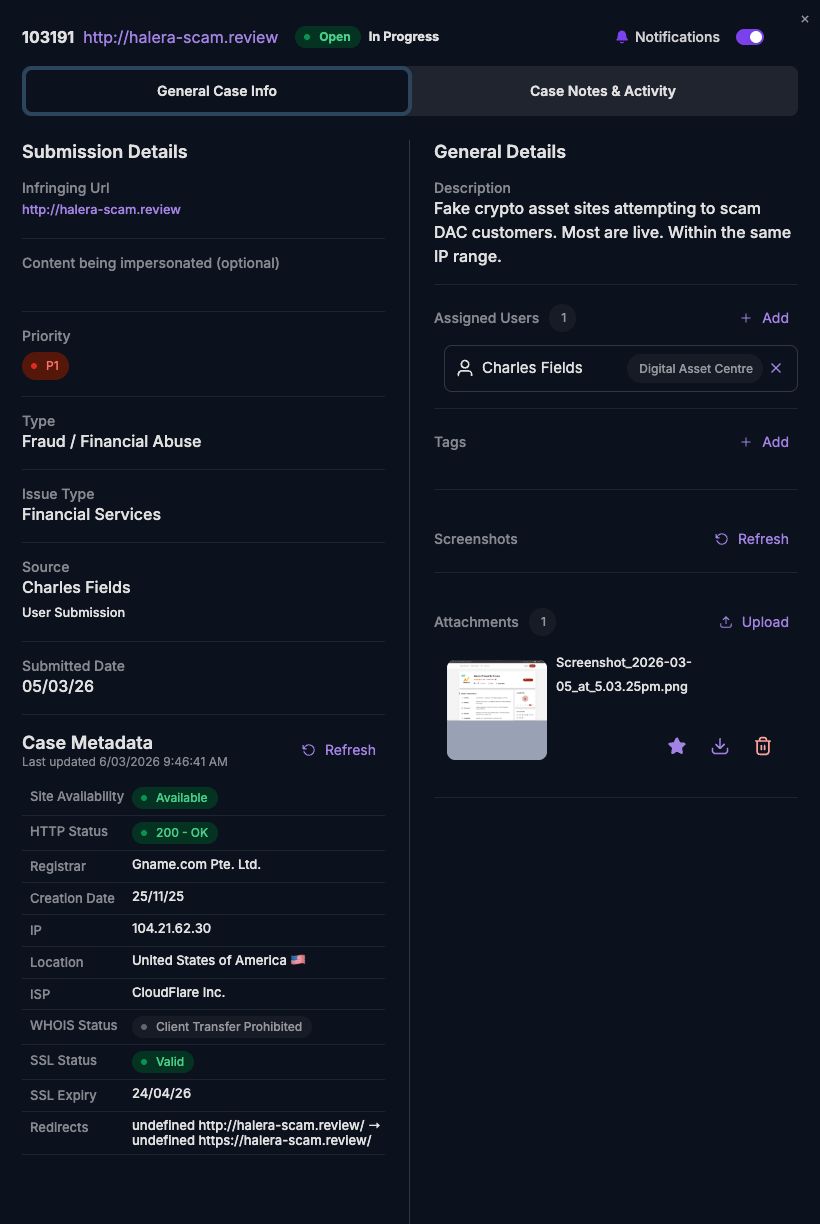
Detection of Fake Crypto Platforms and Phishing Pages
Continuous monitoring to identify fraudulent exchanges, wallet interfaces, and phishing pages designed to steal credentials and assets.
Removal of Impersonated Support and Executive Accounts
Rapid identification and takedown of fake support agents, admins, and executive impersonations across social and messaging platforms.
Monitoring of Scam Tokens and Airdrop Fraud
Detection of malicious token launches, fake airdrops, and promotional scams exploiting hype and user trust.
On-Chain and Off-Chain Threat Correlation
Linking blockchain activity with off-chain infrastructure such as domains, apps, and social accounts to uncover coordinated scam networks.
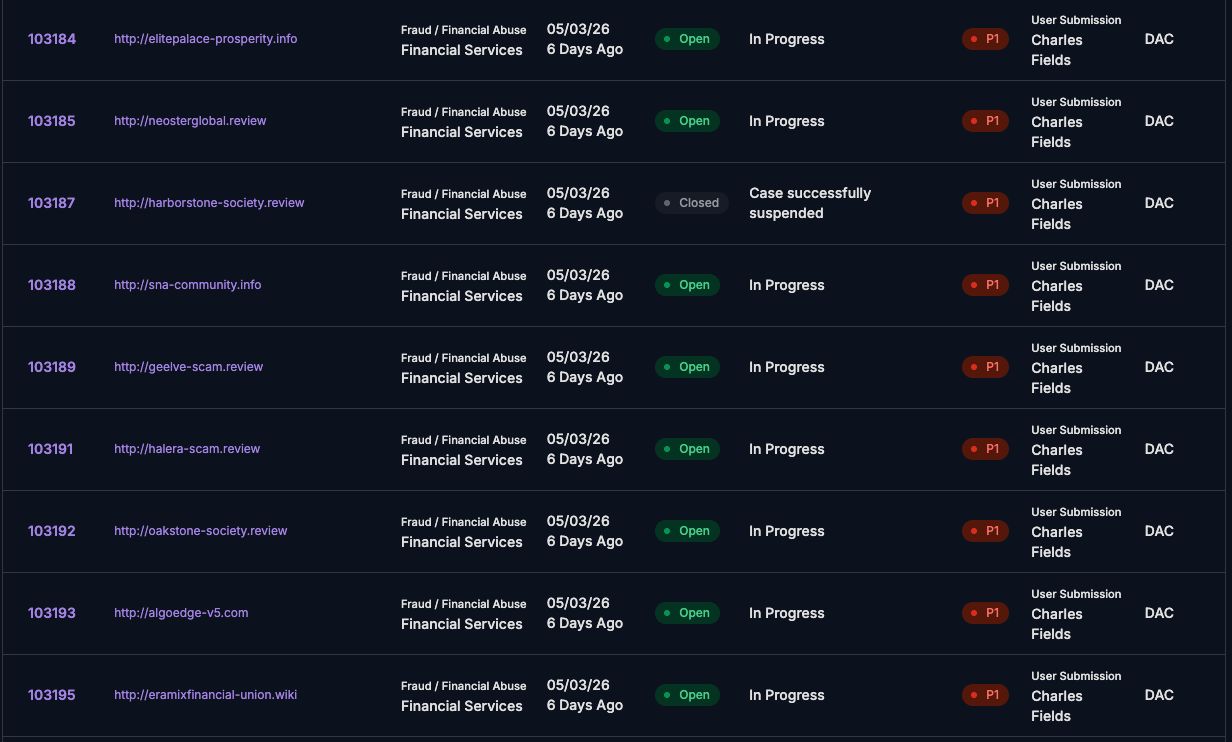
Rapid Takedown of High-Risk Threats
Fast, prioritised takedown workflows to disrupt time-sensitive threats like wallet drainers, phishing campaigns, and fake platforms.
Cross-Platform Scam Infrastructure Disruption
Coordinated enforcement across hosting providers, registrars, and platforms to dismantle scam operations at scale.
Proactive Protection for Crypto Platforms
unphish helps crypto platforms identify scam infrastructure early and disrupt impersonation, wallet drainer, and fraud campaigns before they scale. This reduces user exposure, prevents asset loss, and enables faster response with clear visibility into emerging threats.
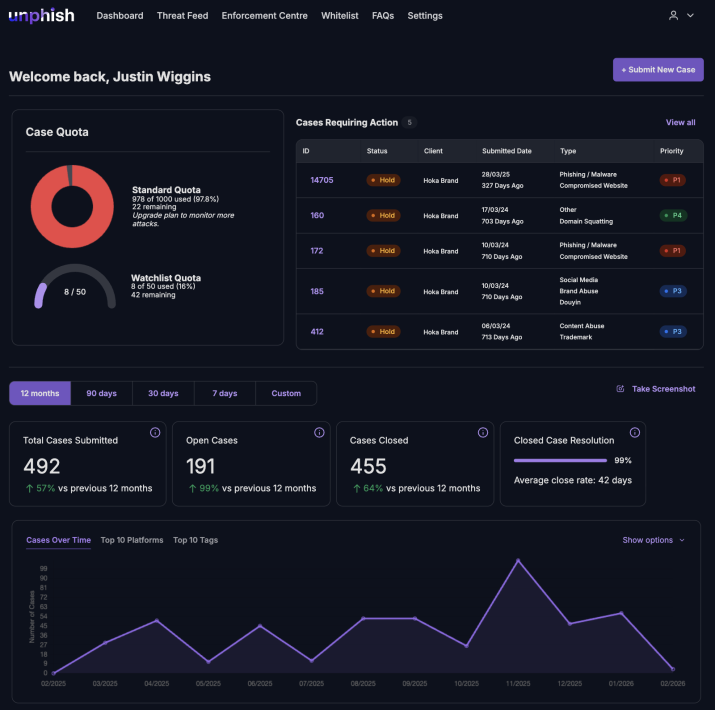
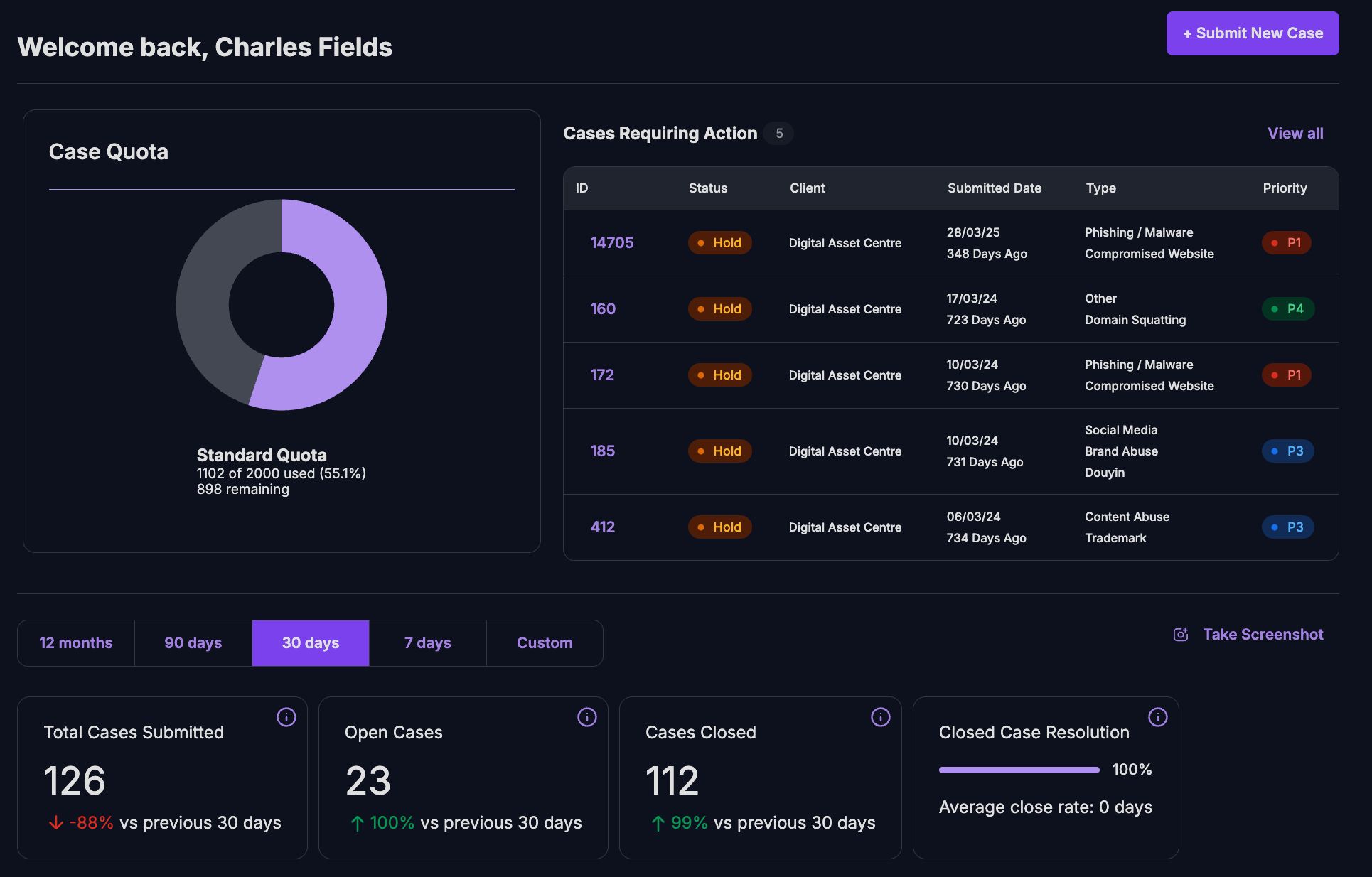
Why Customers Choose unphish
| unphish | Fragmented / Reactive Approach | |
| Threat Visibility | Continuous monitoring across domains, hosting, social platforms, and attacker infrastructure. | Limited visibility based on complaints or isolated alerts. |
| Detection Speed | Automated detection and risk scoring identify threats early. | Threats are discovered late, often after impact. |
| Infrastructure Insight | Deep analysis reveals campaign links, infrastructure reuse, and attacker patterns. | Little or no visibility into shared infrastructure or repeat activity. |
| Enforcement Execution | Coordinated workflows enable faster, consistent takedown across platforms. | Manual submissions slow down response and create inconsistent outcomes. |
| Verification & Control | Automated validation confirms removal and tracks reappearance. | No structured verification or monitoring after takedown. |
| Operational Visibility | Unified dashboards provide clear status, timelines, and reporting. | Siloed tools limit visibility and create operational gaps. |
Reduce User Exposure During High-Risk Crypto Fraud Events
During market surges, token launches, and coordinated scam campaigns, crypto fraud spreads rapidly across platforms. unphish shortens the detection-to-enforcement cycle, disrupts malicious infrastructure quickly, and limits user exposure before significant asset loss occurs.
Protect Your Users and Crypto Ecosystem
See how unphish detects, validates, and disrupts phishing, impersonation, and crypto fraud campaigns across wallets, exchanges, and digital channels through a single, coordinated workflow.