Social Media
Protect brand credibility by detecting and removing social media impersonation across major platforms.
Social Media Impersonation Protection
Social media impersonation is one of the fastest growing and most damaging forms of online fraud. Criminals create fake profiles and pages that imitate trusted brands, executives, and customer support teams to engage directly with victims in real time. These impersonation accounts are used to deliver scams, harvest personal information, redirect payments, and exploit public trust at scale.
Because social platforms are designed for speed and reach, impersonation campaigns can spread rapidly and cause significant harm before they are detected or removed.
unphish enables organisations to identify and disrupt social media impersonation across major platforms, reducing customer exposure and protecting brand credibility.Common Social Media Impersonation Tactics
Impersonation accounts are designed to appear legitimate by copying brand identity, messaging style, and official content. These accounts interact directly with customers to deliver scams or collect sensitive information.
Fake Support Accounts
Fraudulent customer support profiles that reply to complaints or questions and redirect victims to scam links or payment requests.
Executive Impersonation
Attackers impersonate company executives or leadership accounts to request payments, credentials, or confidential business information.
Fraudulent Brand Pages
Fake brand pages promoting deceptive offers, giveaways, or investment opportunities designed to exploit customer trust.
Direct Message Scams
Impersonation accounts contacting customers through private messages with malicious links, fake services, or payment requests.
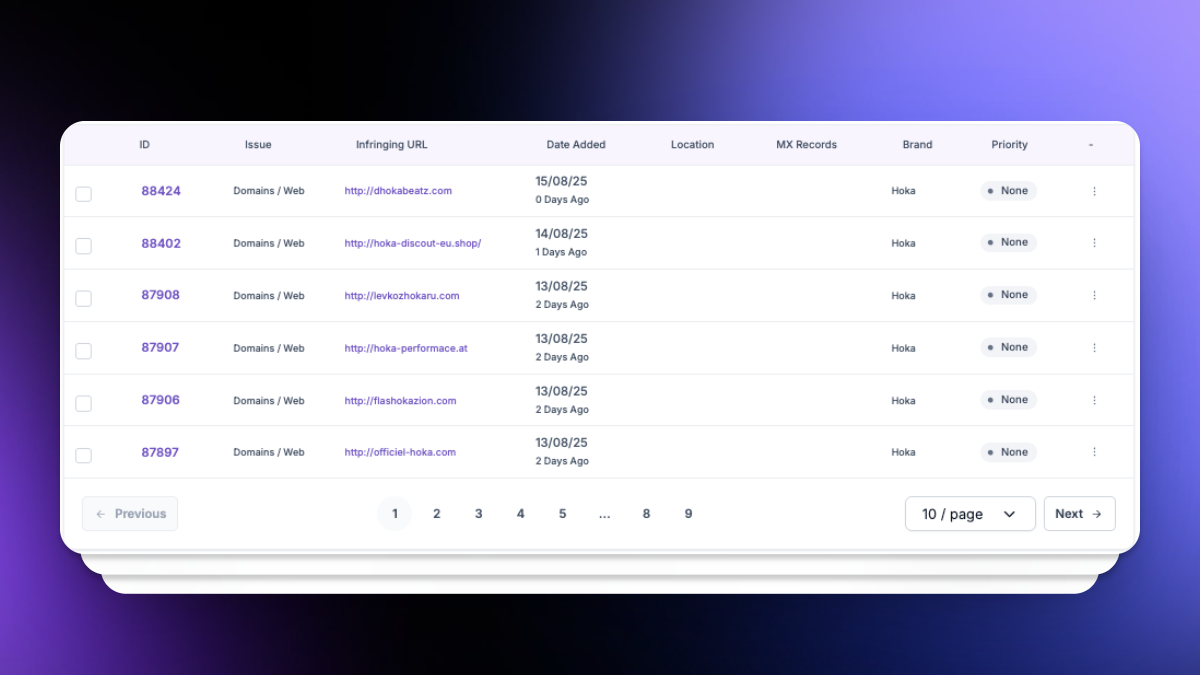
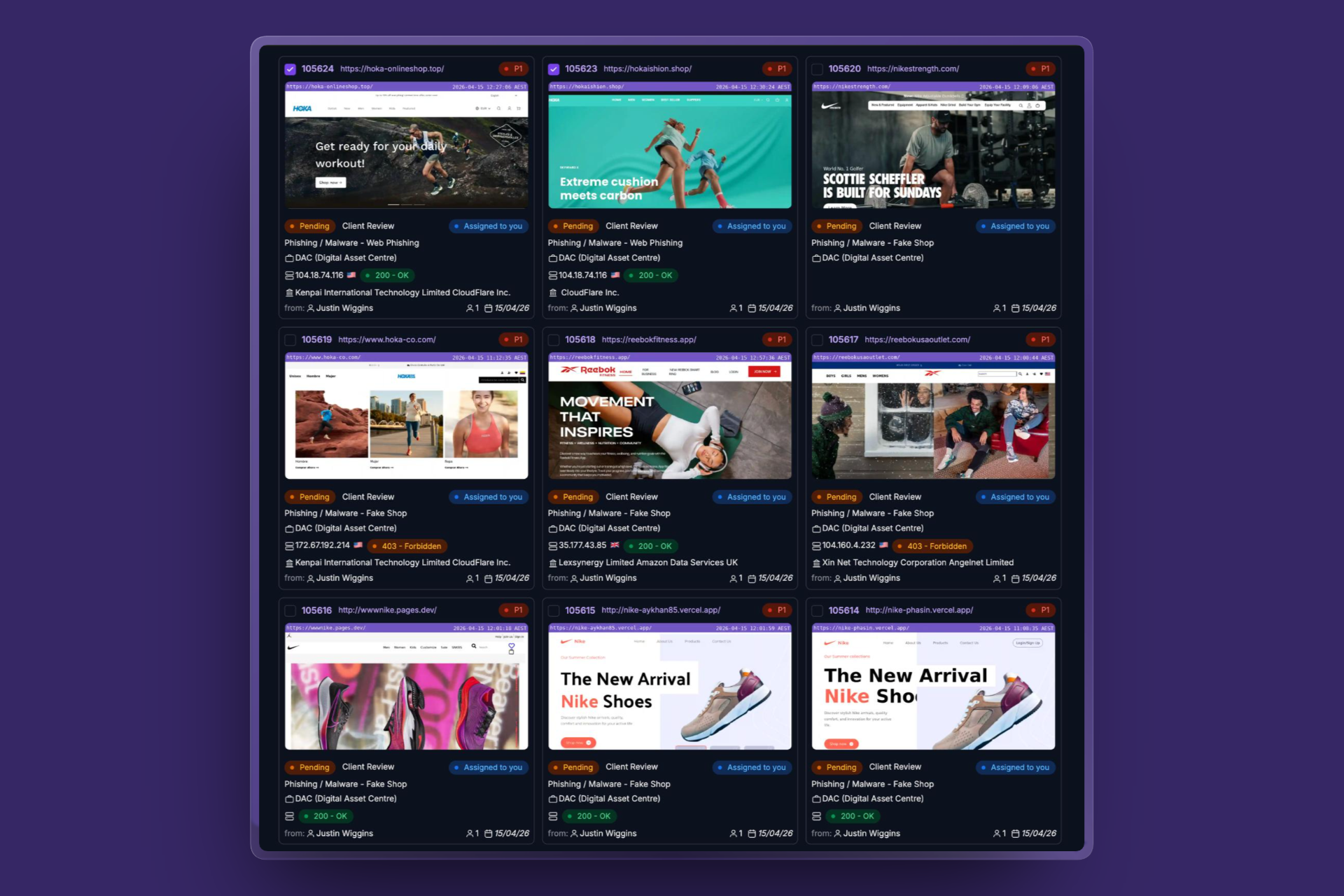
How unphish detects social media impersonation
unphish continuously monitors social media platforms for impersonation activity targeting your organisation, brands, and key individuals. Detection combines automated analysis with intelligence led techniques.
Profile & Page Identification
Impersonation Evidence Detection
Detection of copycat content, imagery, and behavioural patterns associated with impersonation.
Scam Activity Monitoring
Infrastructure Correlation
Correlation of social media findings with domains, websites, and phishing infrastructure.
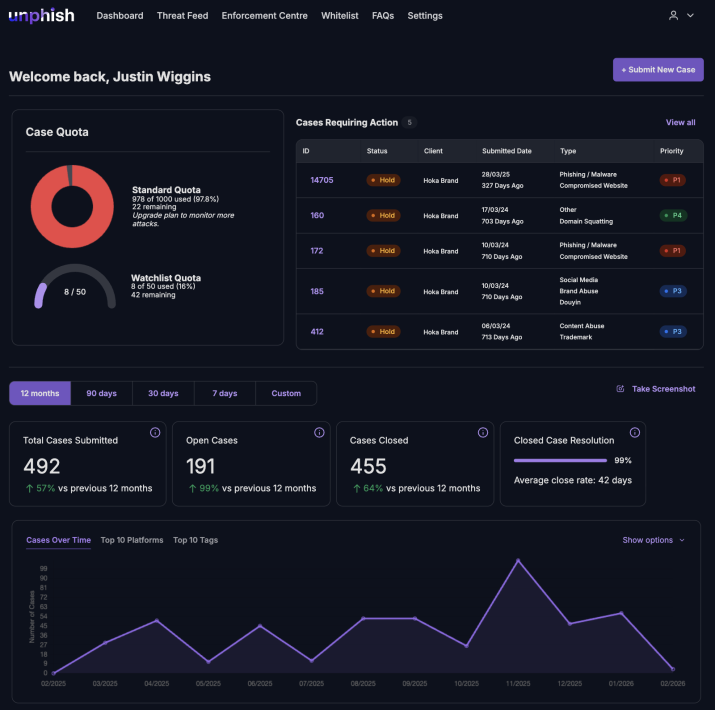
Why Customers Choose unphish
| unphish | Fragmented / Reactive Approach | |
| Threat Visibility | Continuous monitoring across domains, hosting, social platforms, and attacker infrastructure. | Limited visibility based on complaints or isolated alerts. |
| Detection Speed | Automated detection and risk scoring identify threats early. | Threats are discovered late, often after impact. |
| Infrastructure Insight | Deep analysis reveals campaign links, infrastructure reuse, and attacker patterns. | Little or no visibility into shared infrastructure or repeat activity. |
| Enforcement Execution | Coordinated workflows enable faster, consistent takedown across platforms. | Manual submissions slow down response and create inconsistent outcomes. |
| Verification & Control | Automated validation confirms removal and tracks reappearance. | No structured verification or monitoring after takedown. |
| Operational Visibility | Unified dashboards provide clear status, timelines, and reporting. | Siloed tools limit visibility and create operational gaps. |
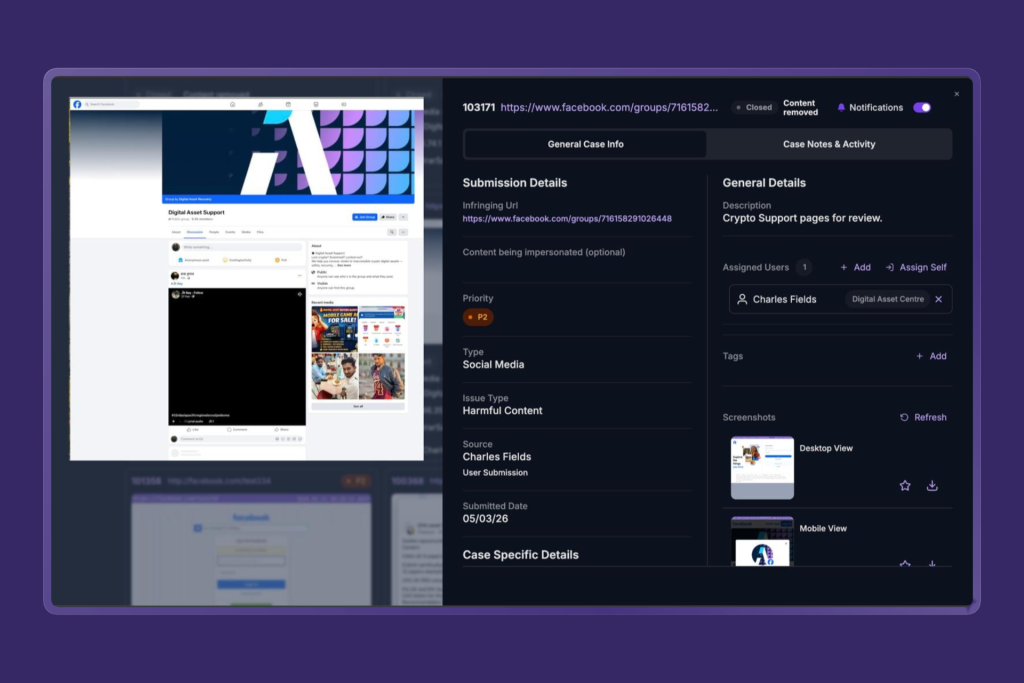
How unphish enforces against impersonation
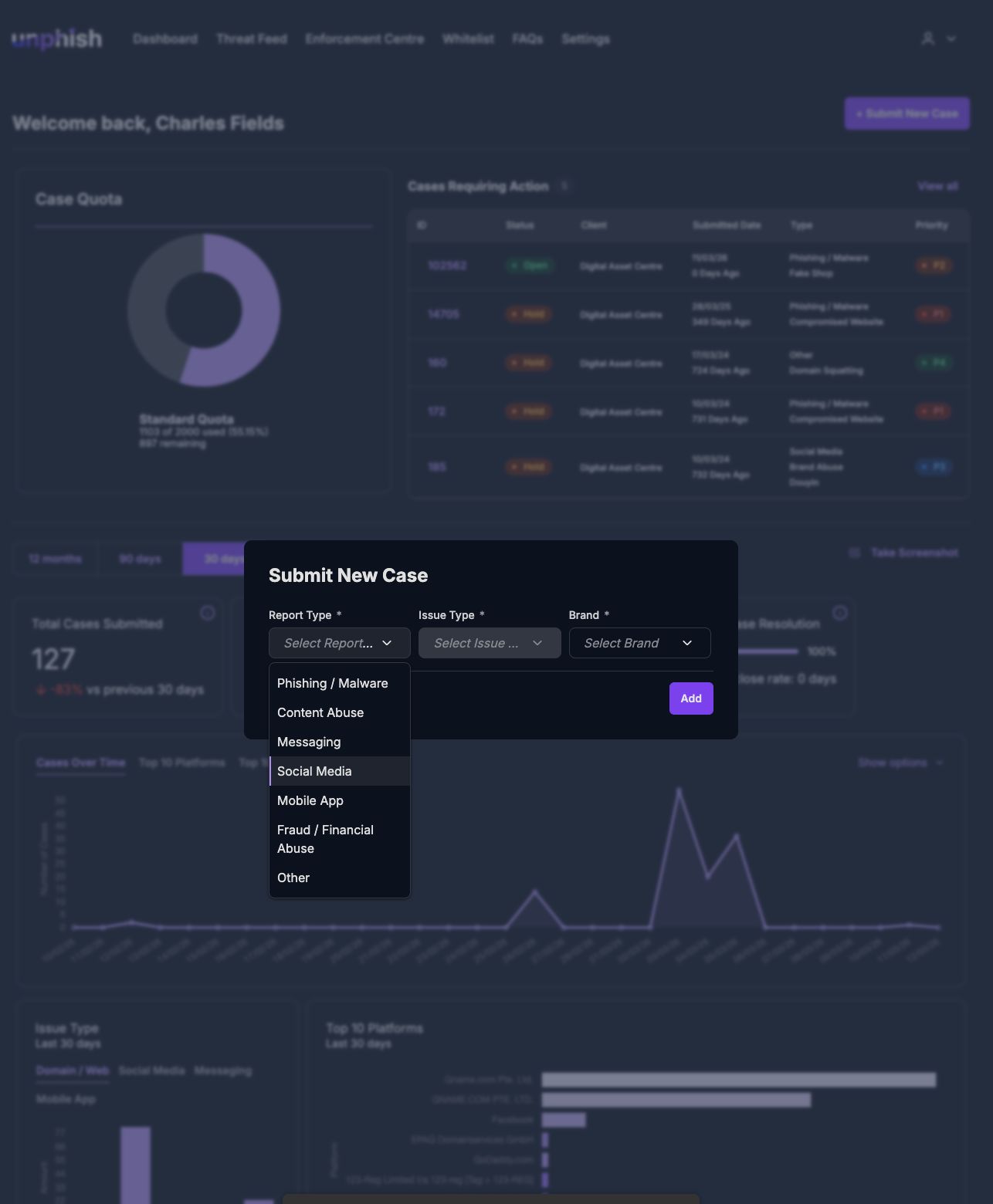
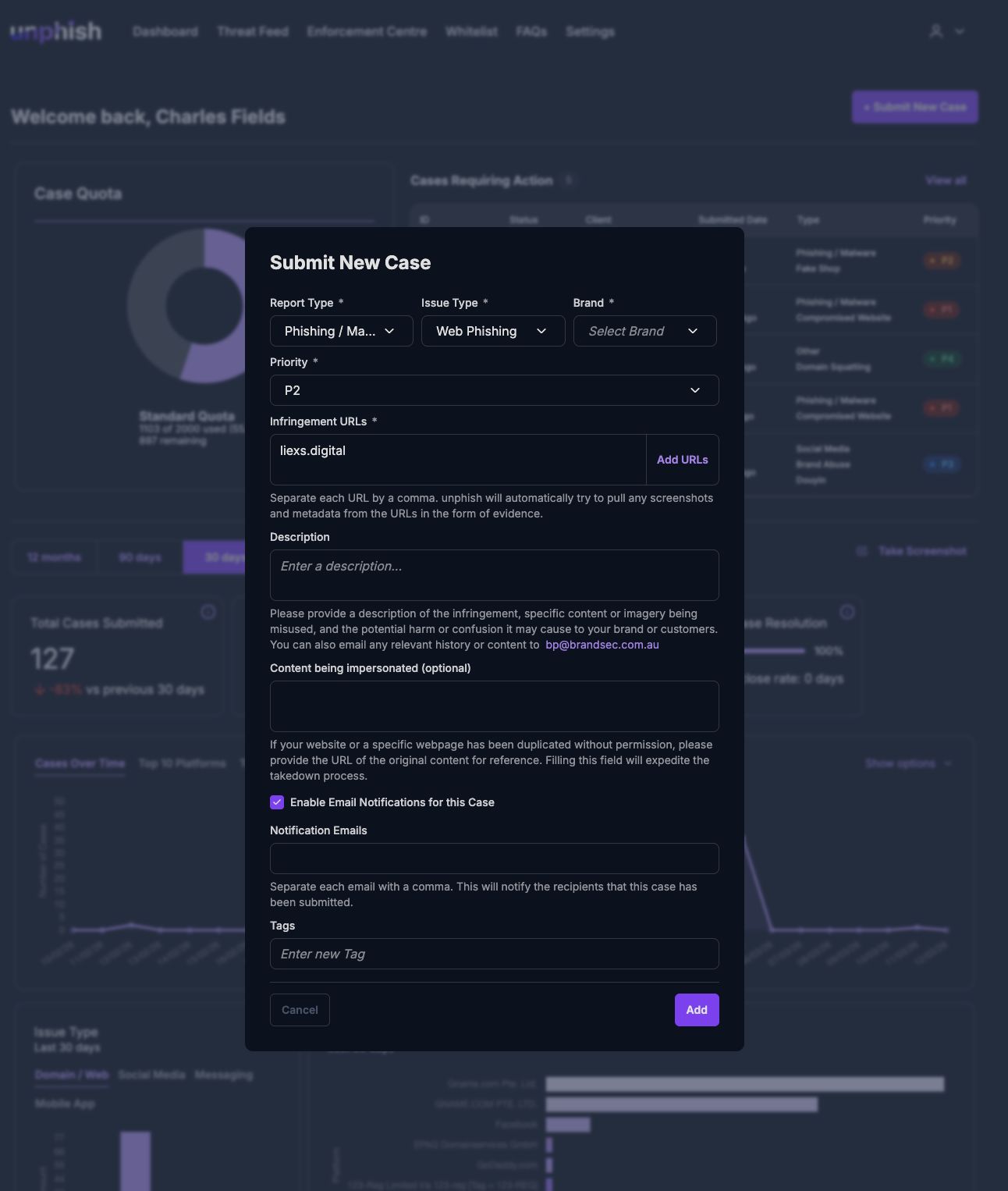
unphish streamlines the enforcement process by enabling rapid and consistent takedown of impersonation accounts.
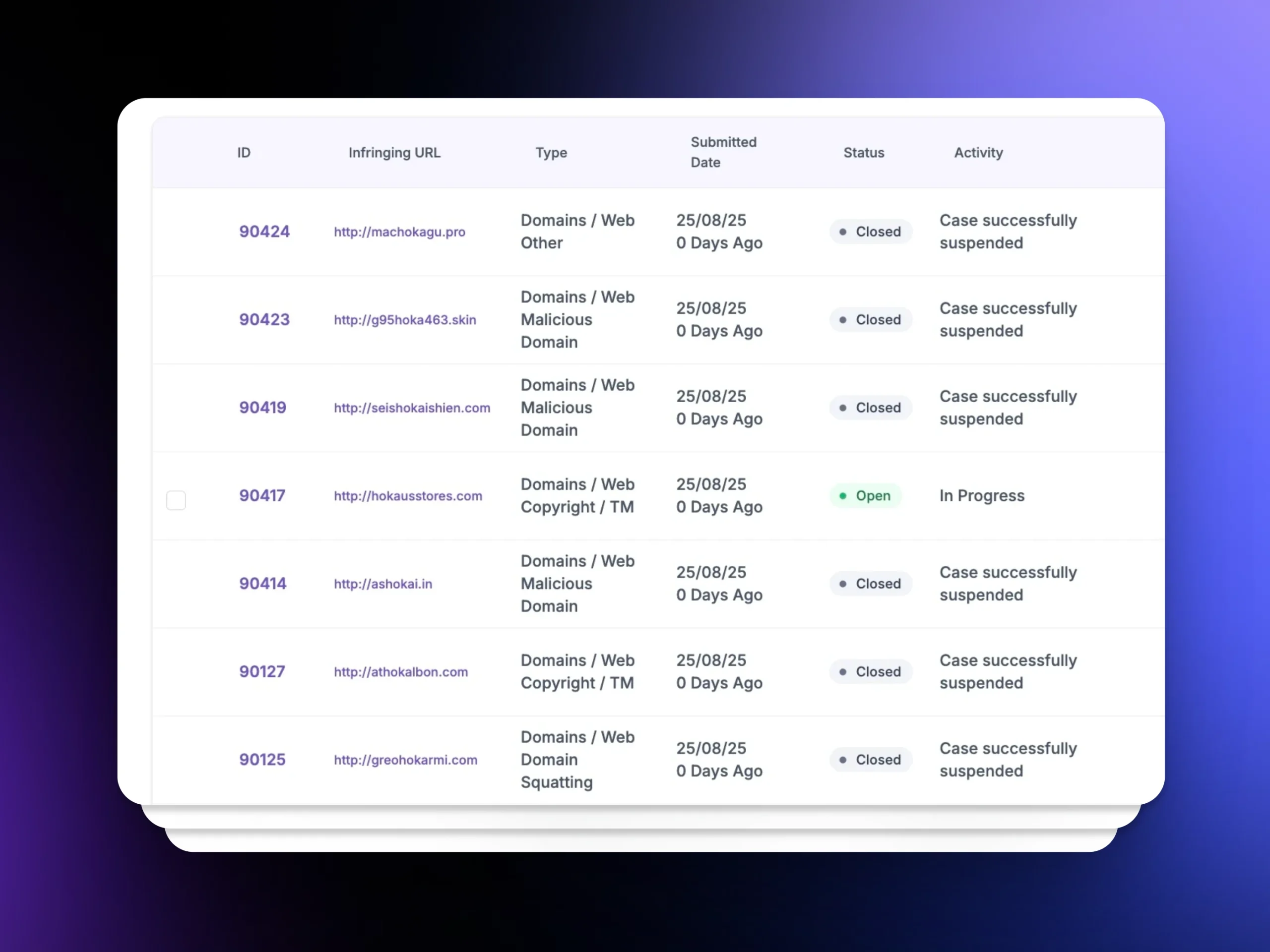
For each impersonation incident, unphish automatically captures platform specific evidence, including profile details, content, imagery, linked infrastructure, and interaction history. This evidence supports fast and defensible enforcement actions aligned to platform policies.
Enforcement actions include
unphish enables rapid enforcement actions to remove abusive assets and disrupt ongoing brand abuse.
Fake Social Profile & Page Removal
Removal of fake social profiles and pages impersonating brands or executives
Coordinated Impersonation Disruption
Disruption of coordinated impersonation campaigns across multiple accounts
Repeat Offender Enforcement
Escalation of repeat offenders using shared infrastructure or identities
Priority Scam Takedown Support
Support for high priority or time sensitive takedowns during active scam campaigns
Why social media impersonation protection matters
Customers increasingly expect to engage with organisations on social platforms. When impersonation accounts intercept those interactions, the result is financial loss, reputational damage, and erosion of trust.
unphish helps organisations maintain control of their social presence by reducing impersonation visibility, protecting customers from direct engagement scams, and providing clear oversight of enforcement activity.
By treating social media impersonation as a core threat rather than a communications issue, unphish enables security, fraud, and brand teams to respond faster and with greater confidence.

FAQs
Key questions about how unphish detects, investigates, and disrupts social media impersonation
1. How quickly can impersonation accounts be removed?
2. Does unphish monitor multiple social media platforms?
3. Can enforcement actions be prioritised during active scams?
4. How does unphish identify coordinated impersonation campaigns?
Stop Social Media Impersonation Before It Spreads
Detect and remove fake profiles, impersonation pages, and scam campaigns targeting your brand across major social platforms.