Smishing and Vishing
Detect and disrupt smishing and vishing attacks that use SMS and voice calls to impersonate trusted organisations. Protect customers from social engineering scams through rapid identification and coordinated takedown
Detect and Disrupt Smishing and Vishing Campaigns
Smishing and vishing attacks use SMS messages and voice calls to impersonate trusted organisations, pressure victims, and drive immediate action. These scams often reference account issues, missed deliveries, payments, or urgent security alerts, and increasingly form part of broader, multi channel fraud campaigns.
Unlike phishing websites or fake apps, smishing and vishing threats move quickly and rely heavily on social engineering. By the time a campaign is visible, customers are often already being targeted. Rapid takedown and disruption are therefore critical.
unphish supports organisations by focusing on fast, coordinated enforcement to dismantle smishing and vishing campaigns once they are identified.
How smishing and vishing campaigns operate
Smishing and vishing campaigns use SMS messages and voice calls to impersonate trusted organisations and pressure victims into urgent actions. Common tactics used in these attacks include:
High-Volume SMS Campaigns
Smishing attacks distribute large volumes of fraudulent SMS messages impersonating trusted organisations. Messages often create urgency around payments, deliveries, or account alerts to push victims into immediate action.
Impersonation Voice Calls
Vishing campaigns use scripted phone calls where attackers pose as banks, support teams, or service providers. Victims are pressured to reveal sensitive information or approve fraudulent transactions.
Rapid Infrastructure Rotation
Attackers frequently rotate phone numbers, SMS sender IDs, and call scripts to evade blocking. This constant change allows campaigns to continue targeting victims even after initial detection.
Phishing and Fraud Redirection
Smishing and vishing messages often direct victims to phishing websites, fake support lines, or fraudulent payment channels designed to capture credentials, personal data, or financial details.
How unphish supports detection
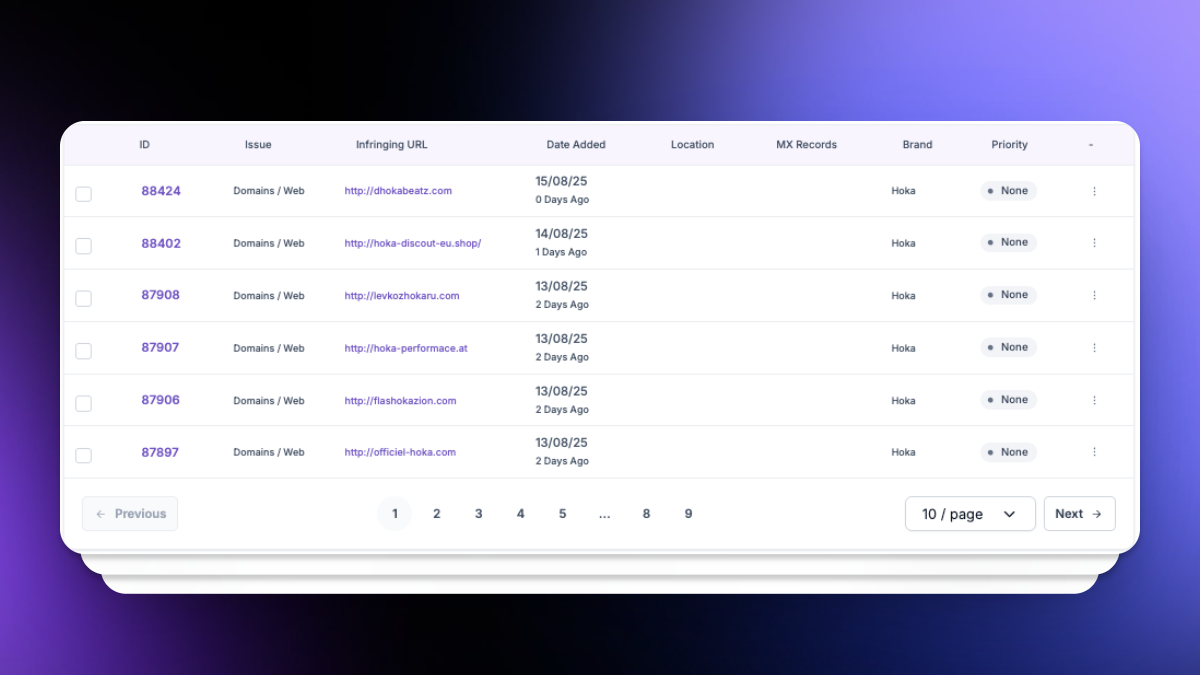
unphish is designed to ingest and operationalise referrals from multiple sources, including:
Customer Reported SMS and Phone Numbers
Internal Fraud and Security Referrals
Cases identified and escalated by internal fraud teams, contact centres, or security teams after detecting suspicious messages, calls, or customer activity.
Why Customers Choose unphish
| unphish | Fragmented / Reactive Approach | |
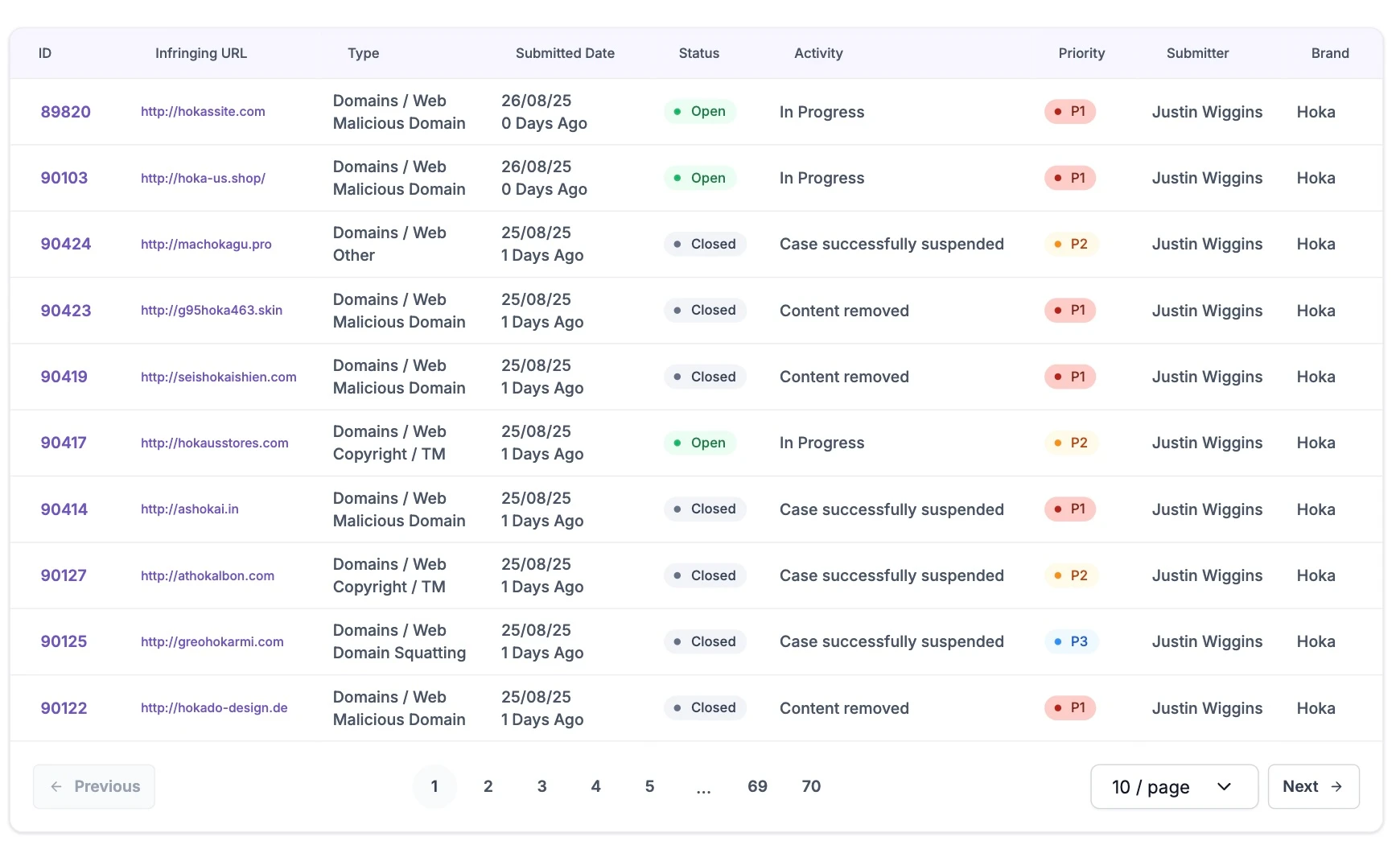
| Threat Visibility | Continuous monitoring across domains, hosting, social platforms, and attacker infrastructure. | Limited visibility based on complaints or isolated alerts. |
| Detection Speed | Automated detection and risk scoring identify threats early. | Threats are discovered late, often after impact. |
| Infrastructure Insight | Deep analysis reveals campaign links, infrastructure reuse, and attacker patterns. | Little or no visibility into shared infrastructure or repeat activity. |
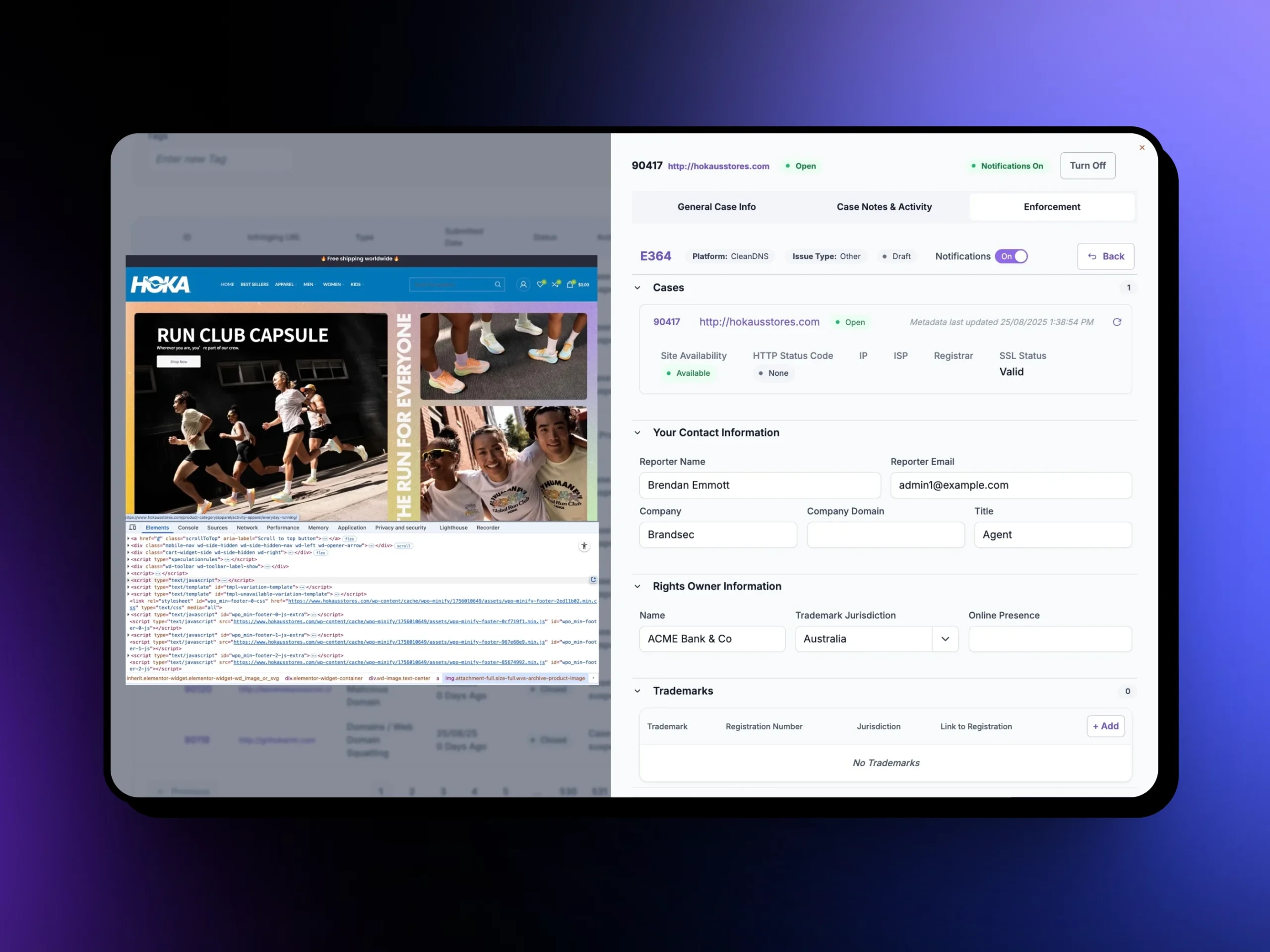
| Enforcement Execution | Coordinated workflows enable faster, consistent takedown across platforms. | Manual submissions slow down response and create inconsistent outcomes. |
| Verification & Control | Automated validation confirms removal and tracks reappearance. | No structured verification or monitoring after takedown. |
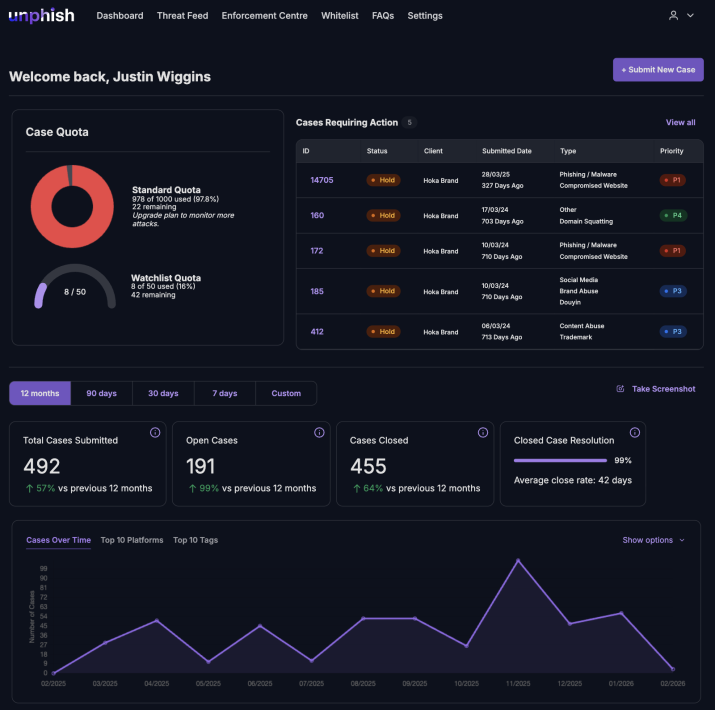
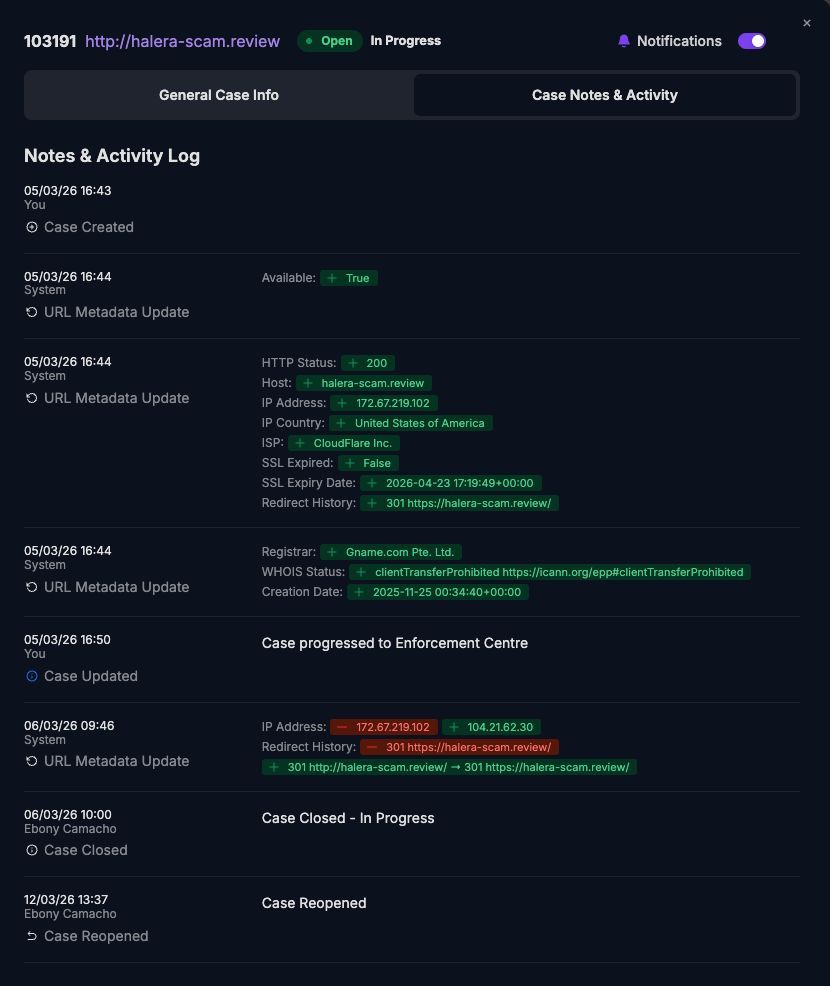
| Operational Visibility | Unified dashboards provide clear status, timelines, and reporting. | Siloed tools limit visibility and create operational gaps. |
Disrupting Smishing and Vishing Campaigns
unphish focuses on dismantling the infrastructure that enables smishing and vishing rather than treating each message or call in isolation.
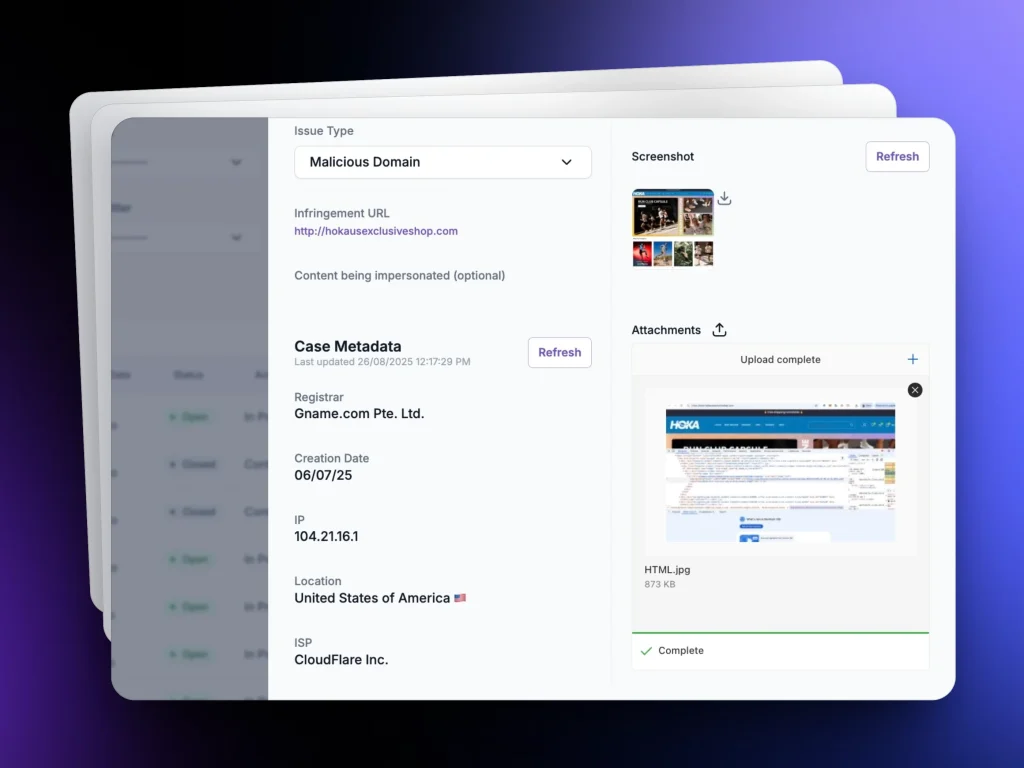
For each campaign, unphish automatically gathers evidence from referrals and linked infrastructure, including message content, phone numbers, domains, hosting details, and redirection paths. This evidence supports fast and defensible enforcement actions.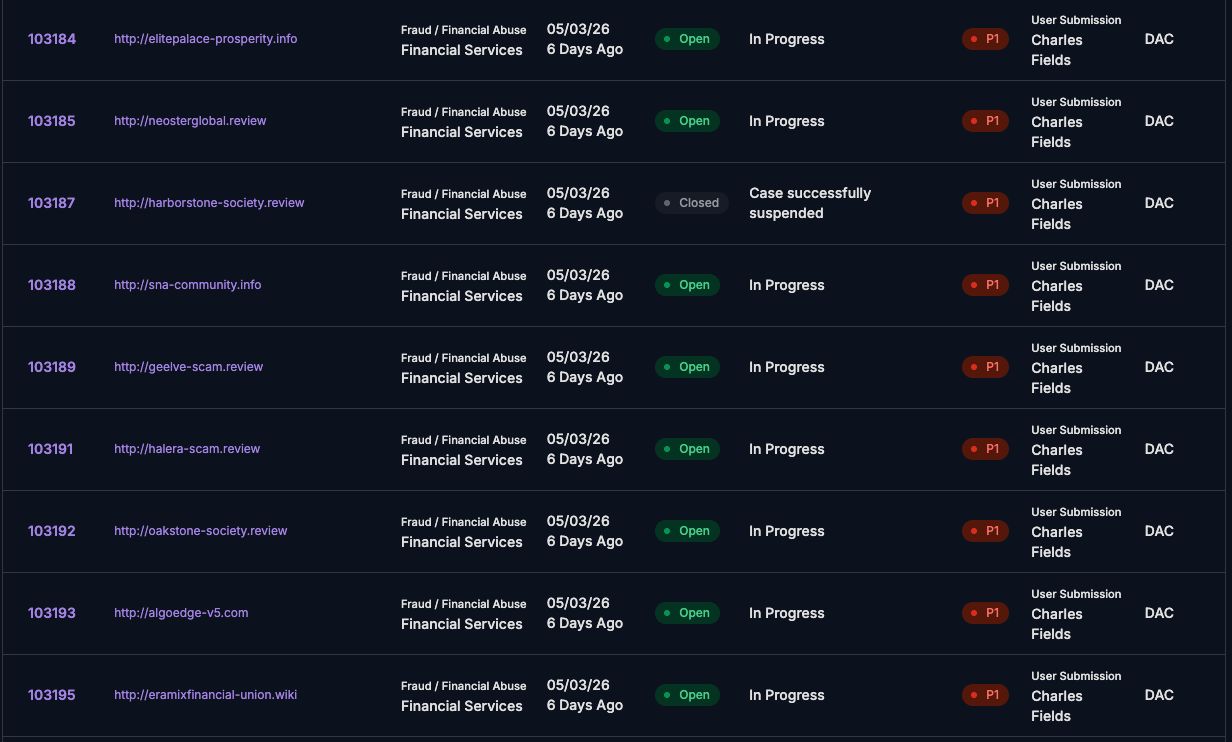
Disruption activities may include
unphish enables rapid enforcement to disrupt smishing and vishing campaigns and remove supporting scam infrastructure.
Phishing Website and Landing Page Takedowns
Takedown of phishing websites and landing pages linked from SMS or voice campaigns
Domain and Hosting Suspension
Suspension of domains and hosting services supporting scam operations
Scam Number and Sender ID Disabling
Coordination with telecommunications to disable scam numbers or sender IDs
Repeat Campaign Infrastructure Disruption
Identification and disruption of repeat campaigns using shared infrastructure
Why rapid takedown matters
Smishing and vishing rely on urgency and scale. The longer infrastructure remains active, the more victims are impacted.
unphish helps organisations reduce harm by shortening the lifespan of scam campaigns, limiting customer exposure, and providing clear visibility of enforcement actions taken.
By focusing on referral driven response and infrastructure level disruption, unphish enables a practical and effective defence against some of the most persistent scam techniques in use today.
FAQs
Key questions about how unphish detects, investigates, and disrupts smishing and vishing campaigns targeting organisations
1. How does unphish detect smishing and vishing campaigns?
2. What happens after a smishing or vishing campaign is identified?
3. Can unphish handle large-scale or coordinated campaigns?
4. How are smishing and vishing campaigns disrupted?
Stop Smishing and Vishing Campaigns Faster
Detect and disrupt SMS and voice-based fraud targeting your brand.