Dark and Deep Web
Identifying Threats Beyond the Open Internet
The dark and deep web host a wide range of criminal activity that directly impacts organisations, customers, and brands. These environments are used to trade stolen data, sell scam tooling, coordinate fraud campaigns, and advertise services that enable phishing, impersonation, and other forms of cyber enabled crime.
While much of this activity occurs outside traditional visibility, it often underpins attacks that later surface on the open internet. Early visibility into dark and deep web activity enables organisations to disrupt threats before they reach customers or operational systems.
unphish provides continuous monitoring and intelligence across dark and deep web environments to support proactive disruption and enforcement.
Common dark and deep web threats
Threat actors use dark and deep web forums, marketplaces, and messaging channels to enable a wide range of illicit activity, including:
Phishing Kit and Scam Tool Sales
Sale and exchange of phishing kits, scam scripts, and impersonation templates
Stolen Credentials and Data Trading
Trading of stolen credentials, personal data, and account access
Fraud Service Advertising
Advertising of services supporting smishing, vishing, and fraud operations
Fake Certificate and Document Sales
Sale of fake certificates, documents, and verification artefacts
Attack Infrastructure Coordination
Coordination of attacks and sharing of infrastructure and techniques
Impersonation of Training and Certification Providers
Websites, profiles, and services impersonating legitimate training or certification providers to deceive candidates and organisations.
How unphish monitors dark and deep web activity
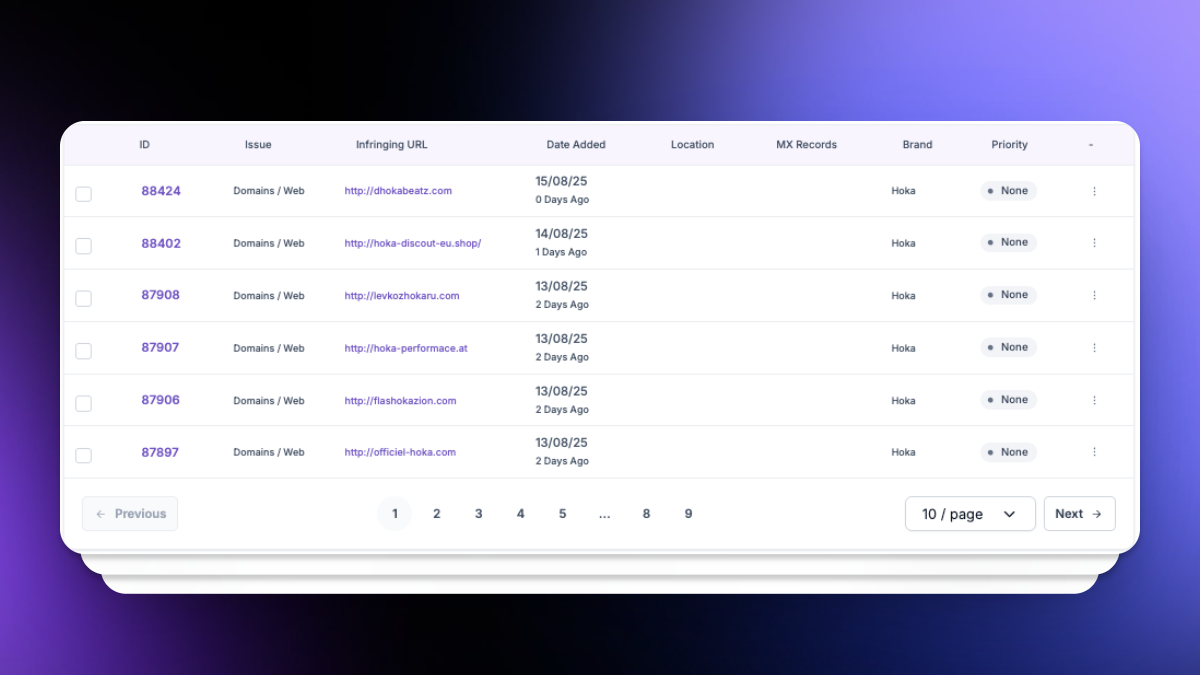
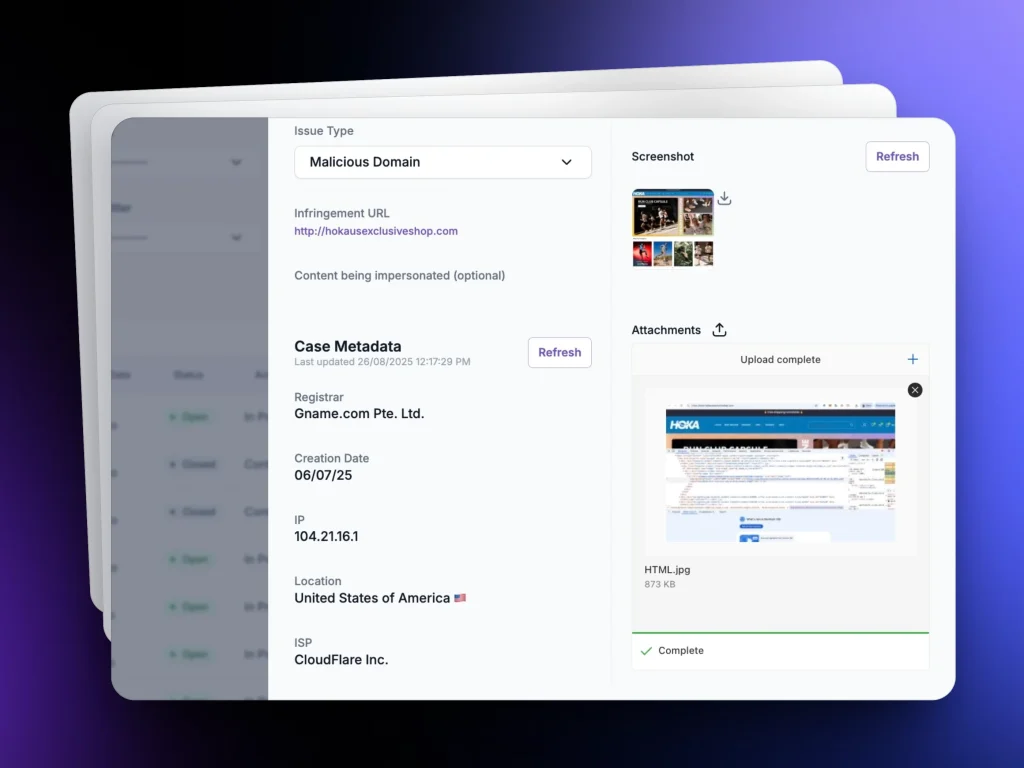
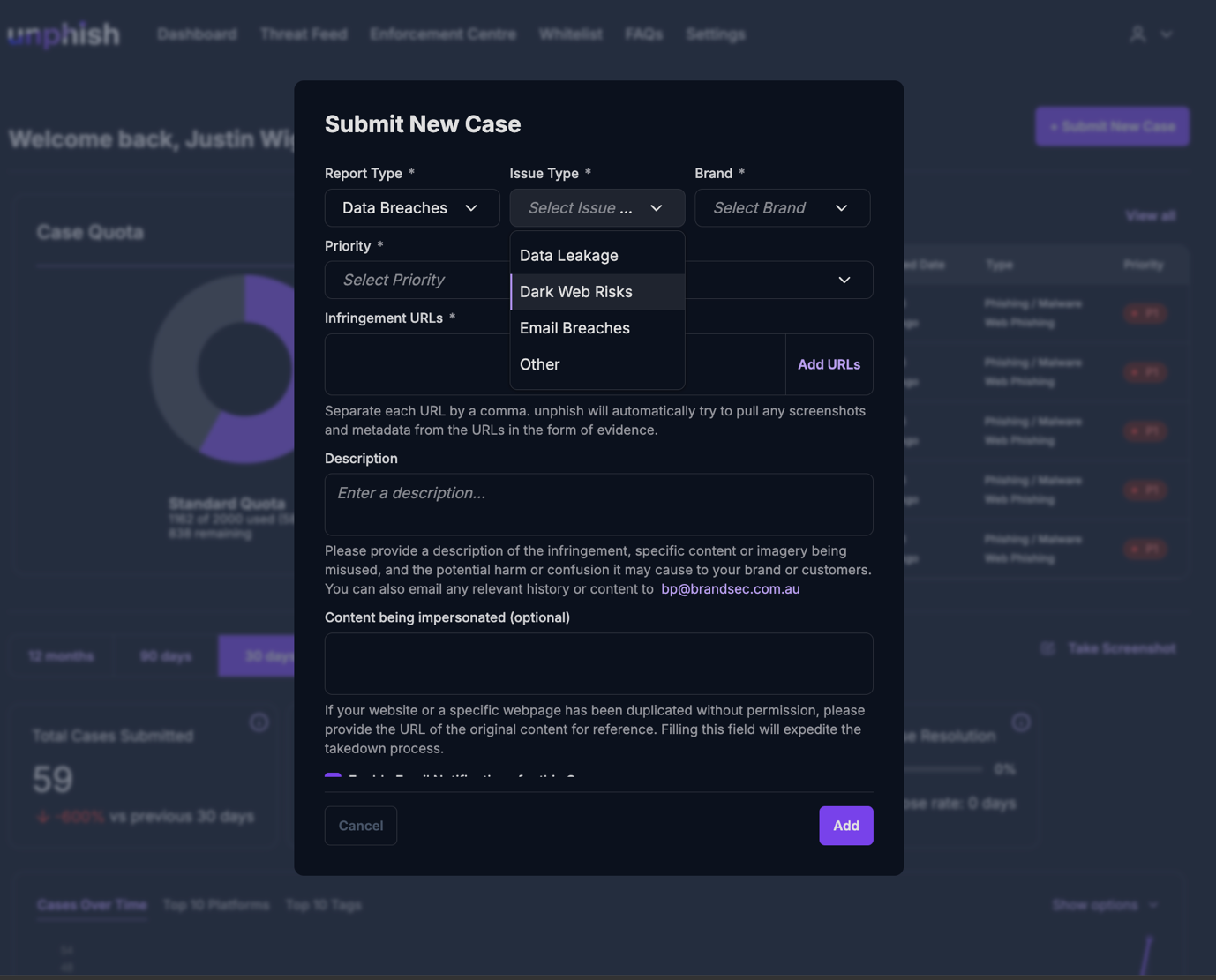
unphish conducts continuous monitoring across relevant dark and deep web sources to identify activity linked to your organisation, brands, and threat profile. Monitoring combines automated collection with analyst driven intelligence, including:
Cybercrime Forum & Marketplace Tracking
Brand and Platform Impersonation Detection
Identification of mentions of brand names, executives, products, and domains.
Data Leak & Credential Monitoring
Fraud Tooling & Infrastructure Analysis
Analysis of tooling, services, and infrastructure being offered or discussed.
Why Customers Choose unphish
| unphish | Fragmented / Reactive Approach | |
| Threat Visibility | Continuous monitoring across domains, hosting, social platforms, and attacker infrastructure. | Limited visibility based on complaints or isolated alerts. |
| Detection Speed | Automated detection and risk scoring identify threats early. | Threats are discovered late, often after impact. |
| Infrastructure Insight | Deep analysis reveals campaign links, infrastructure reuse, and attacker patterns. | Little or no visibility into shared infrastructure or repeat activity. |
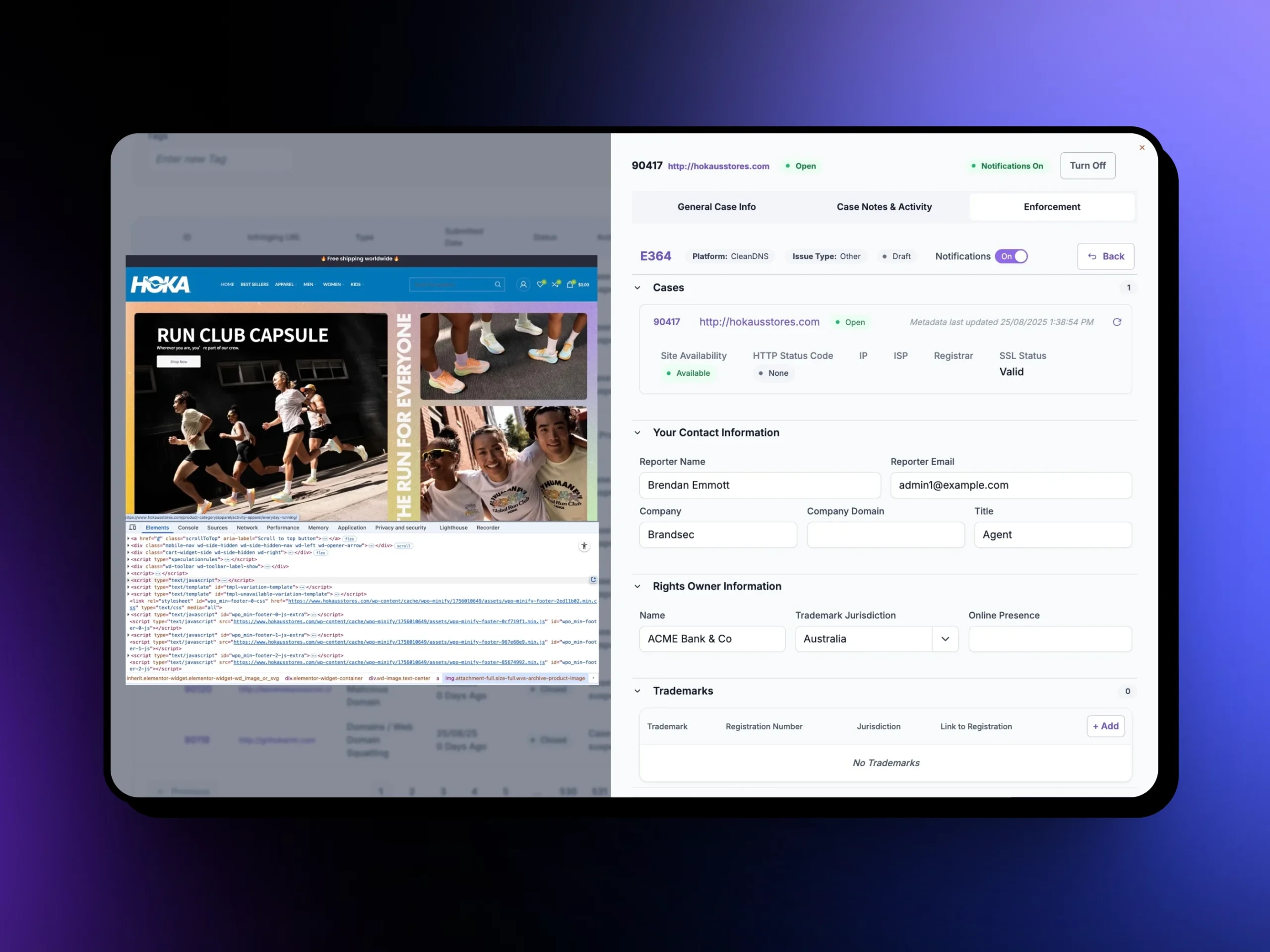
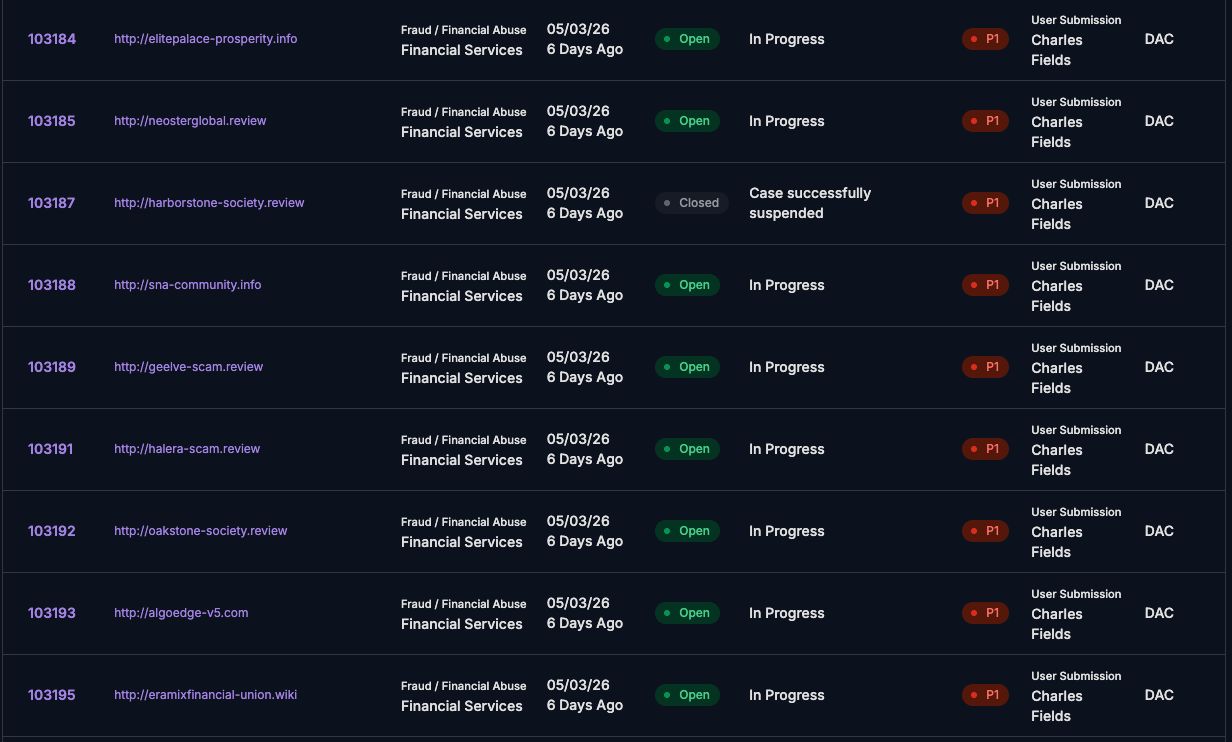
| Enforcement Execution | Coordinated workflows enable faster, consistent takedown across platforms. | Manual submissions slow down response and create inconsistent outcomes. |
| Verification & Control | Automated validation confirms removal and tracks reappearance. | No structured verification or monitoring after takedown. |
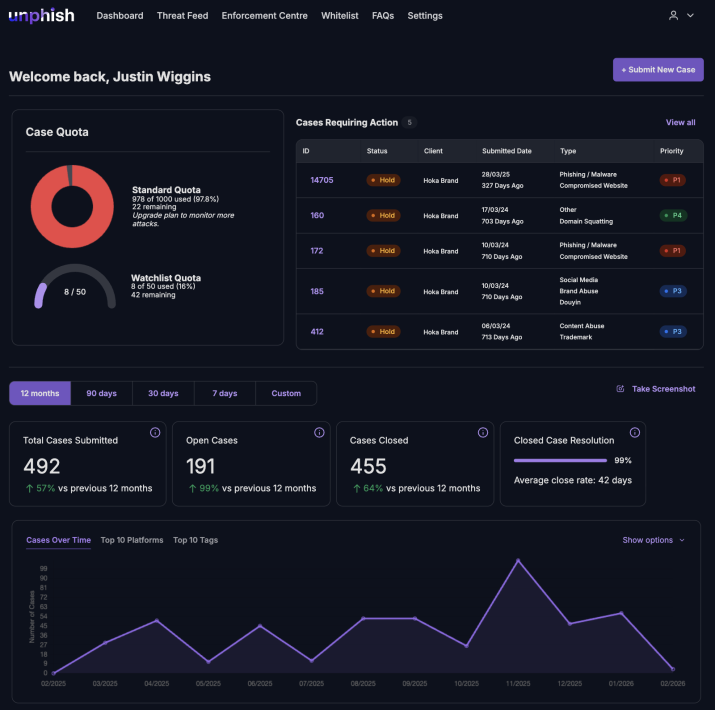
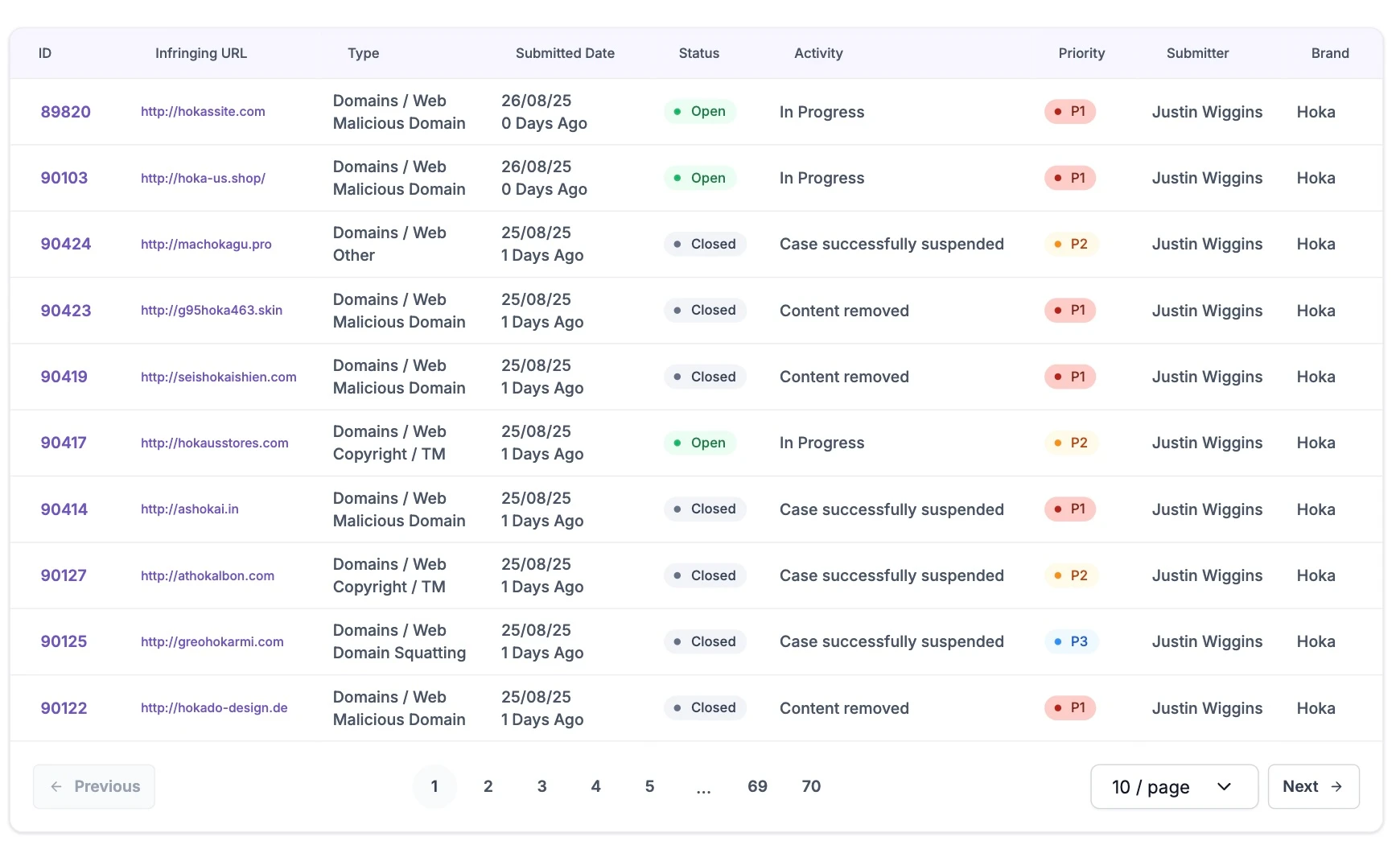
| Operational Visibility | Unified dashboards provide clear status, timelines, and reporting. | Siloed tools limit visibility and create operational gaps. |
How unphish supports disruption and enforcement
Dark and deep web activity rarely exists in isolation. unphish focuses on linking intelligence from these environments to actionable enforcement on the open internet.
Enforcement activities include
Where dark web activity is tied to active or emerging threats, unphish supports disruption by:
Phishing and Impersonation Infrastructure Takedown
Identifying and takedown of phishing sites, impersonation assets, and scam infrastructure.
Fraud Service and Marketplace Disruption
Disrupting services and marketplaces that support active campaigns.
Malicious Domains and Platform Takedown
Targeting domains, hosting providers, and platforms linked to dark web activity.
Coordinated Threat Escalation and Response
Supporting escalation and coordination with internal teams or external partners.
Why dark and deep web monitoring matters
Threats that appear on the open web often originate in the dark and deep web. Without visibility into these environments, organisations are left reacting after damage has already occurred.
unphish helps organisations move upstream by providing early insight into criminal activity, supporting faster response, and enabling more effective disruption of scams and cyber enabled fraud.
By connecting dark and deep web intelligence with enforcement workflows, unphish delivers a more proactive and operational approach to threat prevention.
FAQs
Common questions about how unphish detects, investigates, and disrupts dark and deep web threat activity.
1. How does unphish detect dark and deep web threats?
2. What happens after dark web threats are identified?
3. Can unphish identify organised cybercrime networks on the dark web?
4. How does unphish help disrupt dark web enabled attacks?
Detect and Disrupt Dark & Deep Web Threats
Identify stolen data, fraud services, and cybercrime activity emerging across dark and deep web channels before they escalate into attacks targeting your organisation and customers.