Threat Detection
Detect and stop phishing before it impacts your organisation. unphish identifies malicious domains and impersonation, then acts quickly to reduce customer harm, financial loss, and reputational risk.
Continuous Threat Detection Built for Infrastructure Disruption
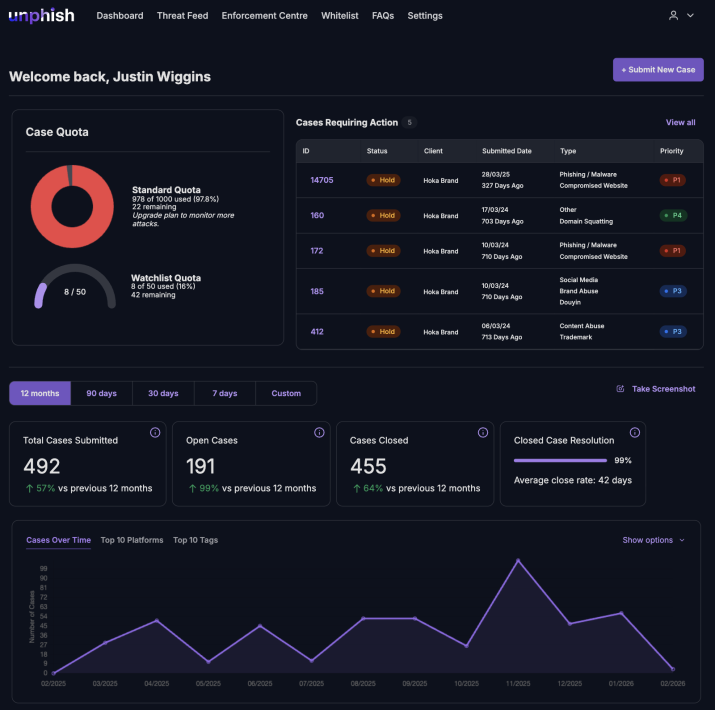
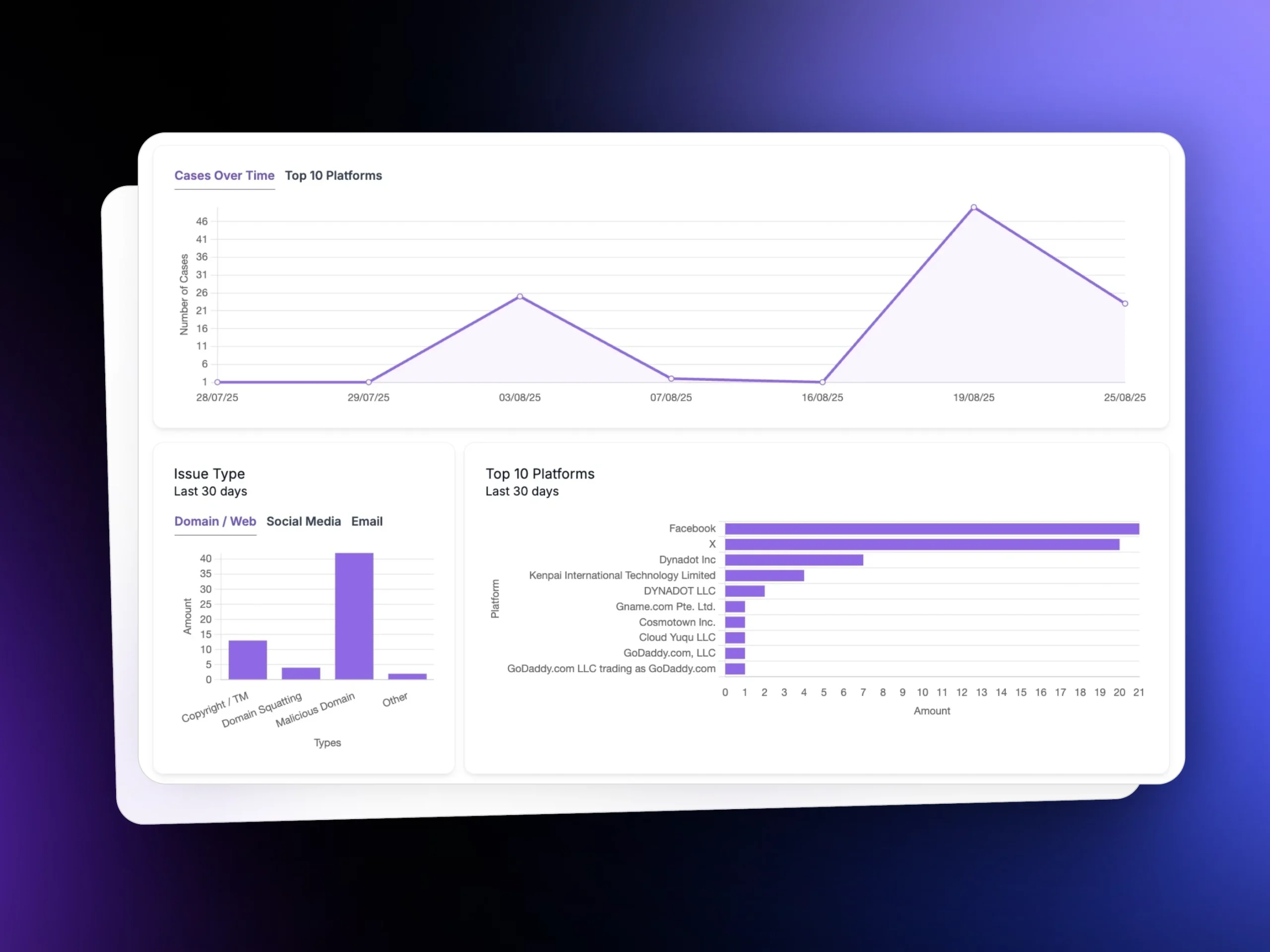
unphish delivers automated, intelligence-led threat detection across domains, social platforms, and hosting infrastructure. From initial signal to verified takedown, the platform connects detection, analysis, enforcement, and reporting into a single operational workflow.
Why Continuous Threat Detection Is Critical for Protecting Your Organisation
Modern phishing campaigns are automated and short-lived. Attackers register lookalike domains, clone login pages, and rotate hosting to bypass controls. Without continuous monitoring and fast enforcement, exposure grows quickly and customer risk increases.
Infrastructure-Level Abuse
Phishing extends beyond email. Attackers deploy lookalike domains, SSL certificates, and hosting infrastructure to mimic legitimate brands and evade controls. Early detection limits campaign spread and reduces customer exposure.
Impersonation at Scale
Cloned login pages, fake support accounts, and malicious ads exploit brand trust. Automated monitoring across web, social, and DNS layers helps identify impersonation quickly and disrupt campaigns before victims engage.
Operational and Regulatory Risk
Delayed detection increases fraud losses and regulatory scrutiny while placing sustained pressure on security and fraud teams. Fragmented tools slow response and make measurable disruption harder to demonstrate.
From Signal to Verified Disruption
Automated Threat Detection
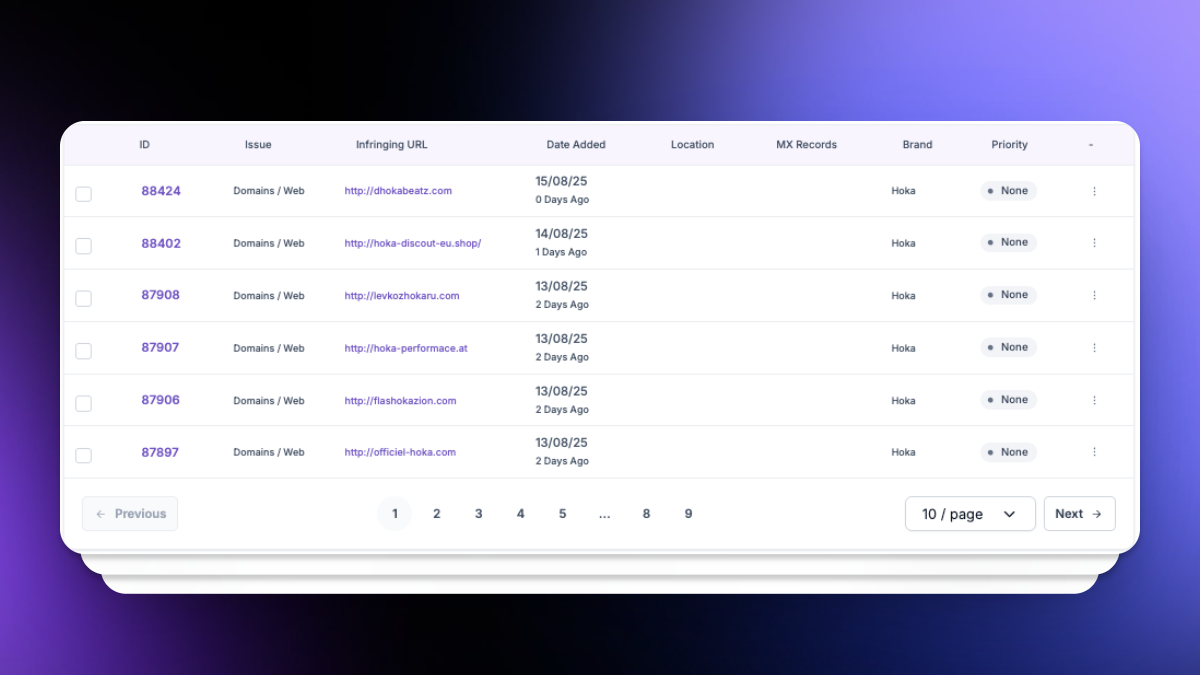
unphish continuously monitors domains, social media platforms, phishing databases, and DNS intelligence feeds to identify early indicators of brand abuse and phishing infrastructure. Detection spans newly registered domains, impersonation accounts, and malicious hosting environments.
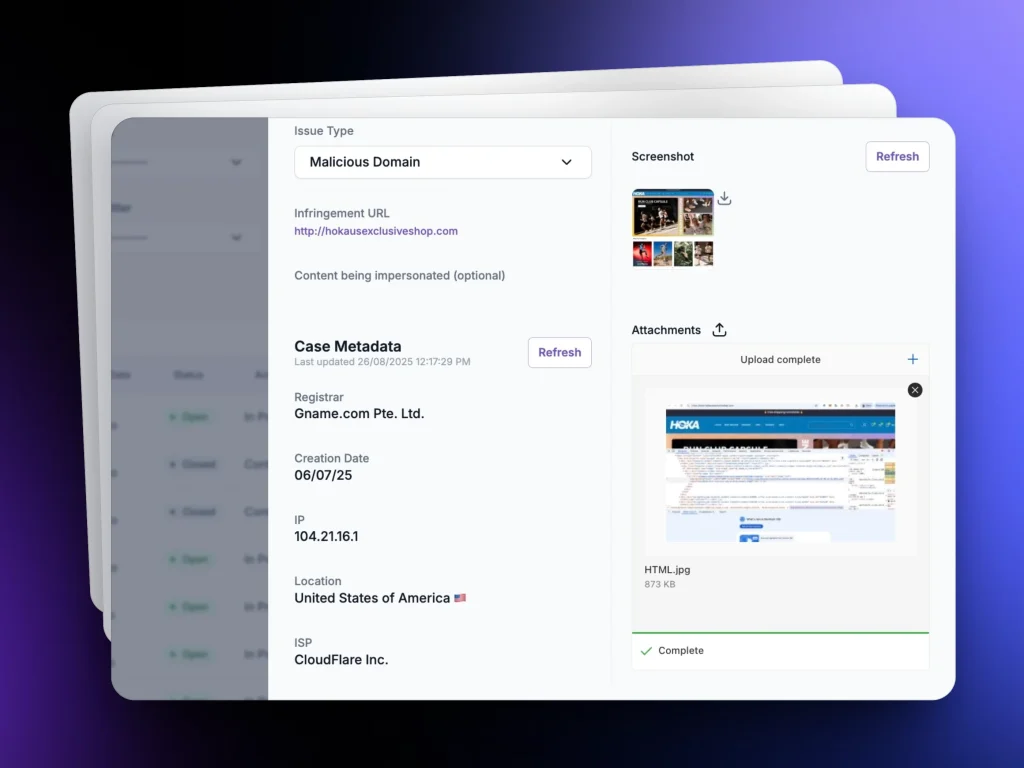
Data Enrichment
Each detection is automatically enriched with structured intelligence including WHOIS data, DNS records, HTML capture, SSL certificates, hosting details, passive DNS history, screenshots, and bad neighbourhood analysis. This creates a defensible, evidence-ready threat record.
AI-Driven Risk Assessment
Advanced analysis layers apply risk scoring, impersonation detection, and pattern recognition to distinguish high-risk phishing activity from benign registrations. Reused infrastructure, cloned login pages, and coordinated campaigns are identified at scale.
Client or Analyst Validation
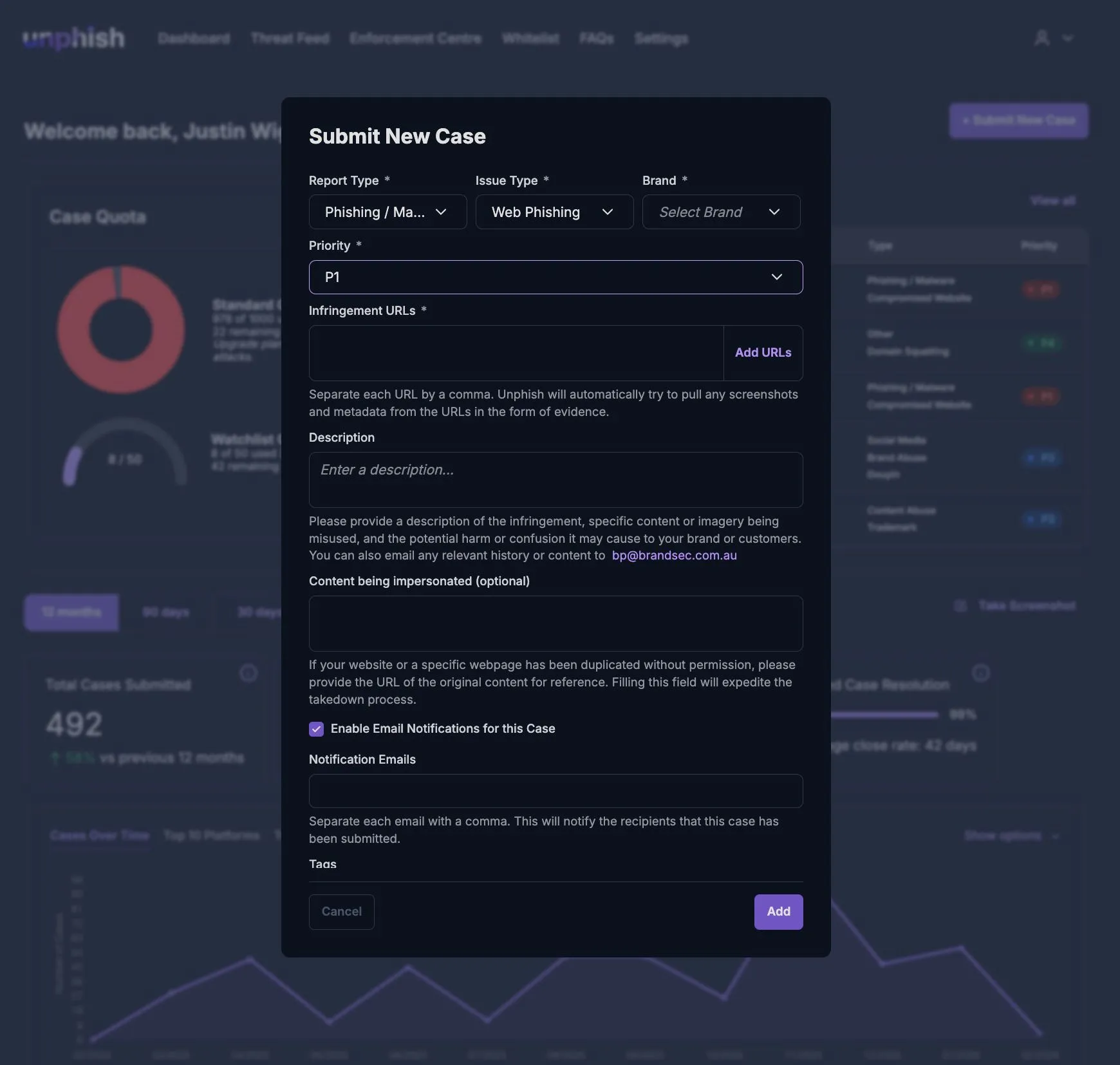
Security or fraud teams can review flagged threats, approve enforcement, ignore false positives, or move assets to watchlists. This structured review stage ensures oversight without slowing response times.
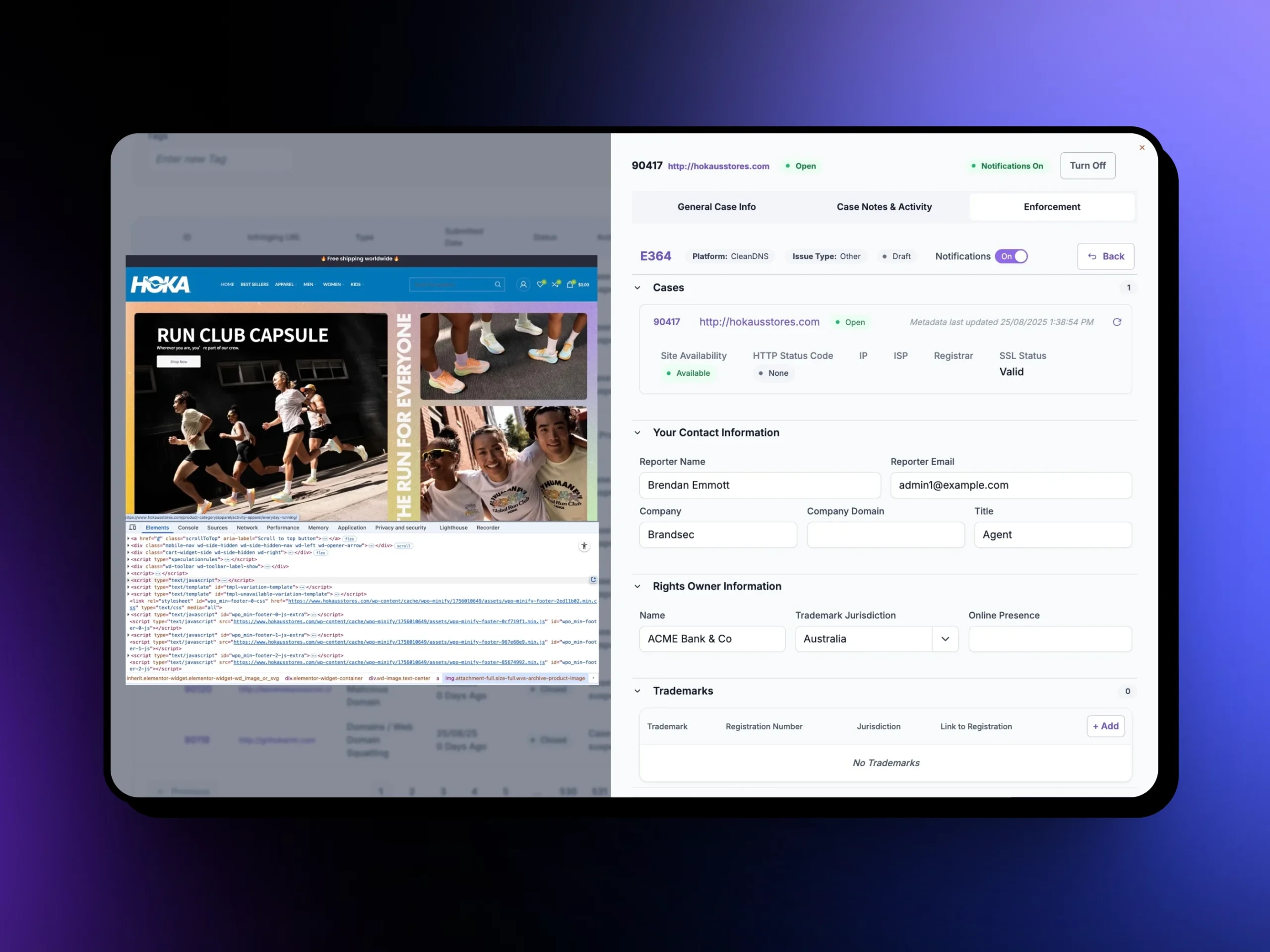
Automated Enforcement
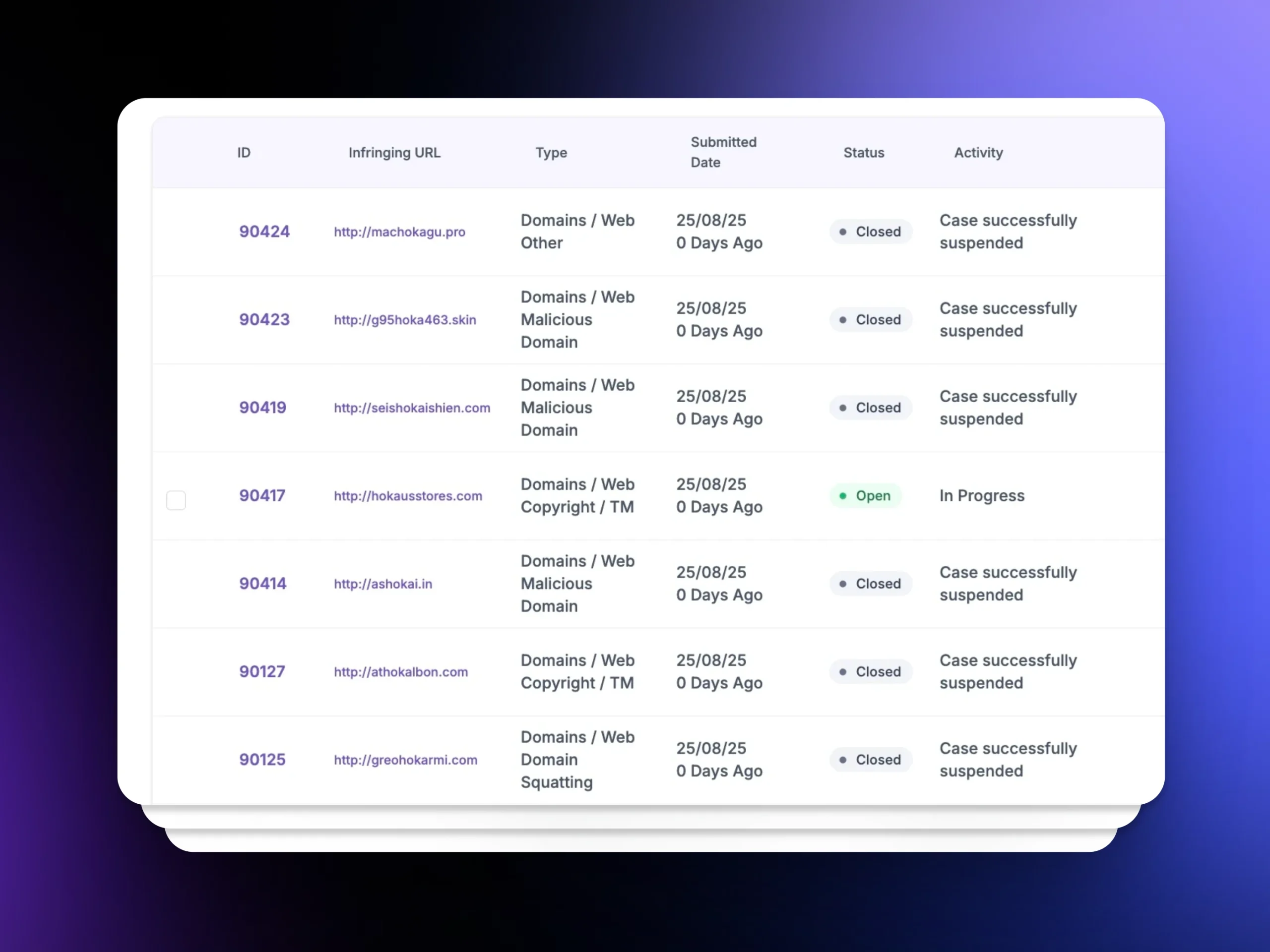
Once validated, enforcement workflows are initiated across registrars, hosting providers, CleanDNS, XARF channels, and social platforms. Structured submissions accelerate takedown and reduce exposure windows.
Takedown Verification
Post-enforcement validation confirms content removal through automated checks, screenshot confirmation, and DNS status monitoring. Rebuild attempts or infrastructure shifts are tracked to prevent repeat abuse.
Why organisations choose unphish for phishing site removal.
Enterprise-grade detection and enforcement designed to reduce exposure time and deliver measurable disruption.
| unphish | Fragmented / Reactive Approach | |
| Threat Visibility | Continuous monitoring across domains, hosting, social platforms, and attacker infrastructure. | Limited visibility based on user complaints or isolated alerts. |
| Speed of Detection | Automated signal correlation and risk scoring identify campaigns early. | Delayed discovery after customer impact or internal escalation. |
| Infrastructure Insight | Enrichment with DNS, SSL, hosting artefacts, and reuse analysis reveals campaign networks. | Little or no visibility into shared infrastructure or repeat offenders. |
| Enforcement Execution | Integrated enforcement workflows reduce exposure windows across registrars, hosts, and platforms. | Manual submissions and inconsistent handling delay takedown. |
| Verification & Control | Automated validation confirms removal and monitors rebuild attempts. | No structured verification or rebuild tracking. |
| Operational Oversight | Unified dashboards provide measurable disruption metrics and audit-ready reporting. | Siloed tools create blind spots and limited governance visibility. |
Why Customers Choose unphish
| unphish | Fragmented / Reactive Approach | |
| Threat Visibility | Continuous monitoring across domains, hosting, social platforms, and attacker infrastructure. | Limited visibility based on complaints or isolated alerts. |
| Detection Speed | Automated detection and risk scoring identify threats early. | Threats are discovered late, often after impact. |
| Infrastructure Insight | Deep analysis reveals campaign links, infrastructure reuse, and attacker patterns. | Little or no visibility into shared infrastructure or repeat activity. |
| Enforcement Execution | Coordinated workflows enable faster, consistent takedown across platforms. | Manual submissions slow down response and create inconsistent outcomes. |
| Verification & Control | Automated validation confirms removal and tracks reappearance. | No structured verification or monitoring after takedown. |
| Operational Visibility | Unified dashboards provide clear status, timelines, and reporting. | Siloed tools limit visibility and create operational gaps. |
FAQs
Everything you need to know about how unphish identifies, analyzes, and responds to emerging threats across digital environments.
1. How does unphish detect threats?
2. Does unphish rely on customer or employee reporting?
3. How does unphish reduce false positives?
4. Can threats be prioritised by risk?
5. What happens after a threat is identified?
6. How is detection performance measured?
Stop Threats Before They Impact Your Brand
Move from isolated alerts to coordinated threat disruption. Detect malicious domains, validate risk with structured intelligence, and initiate rapid enforcement through a single operational workflow designed to reduce exposure and protect customers faster.