Piracy
Disrupt Digital Piracy at Scale
Digital piracy involves the unauthorised distribution, streaming, or sharing of copyrighted content across websites, torrent platforms, file sharing services, and social channels. For media companies, content owners, and digital platforms, piracy directly impacts revenue, licensing value, and contractual obligations, while also exposing customers to malware, scams, and unsafe content.
Piracy ecosystems are highly adaptive. Content is rapidly mirrored, re uploaded, and redistributed across multiple platforms to avoid detection and takedown. Effective disruption requires continuous monitoring and coordinated enforcement at scale.
unphish helps organisations identify and disrupt piracy activity by combining advanced detection techniques with integrated enforcement workflows.Common Channels Used for Digital Piracy
Online piracy operates across many digital platforms where copyrighted content is illegally distributed, streamed, or shared to large audiences
Illegal Streaming Platforms
Websites and embedded video players that provide unauthorised streaming of movies, TV shows, sports events, or premium digital content.
Torrent & Peer-to-Peer Networks
Decentralised sharing networks that allow users to upload and download pirated files directly between devices.
File Hosting & Download Sites
Cloud storage and file hosting services used to store pirated media and distribute it through public download links.
Social Media & Content Sharing Channels
Pages, groups, and channels on social platforms used to promote, share, or redirect users to pirated content sources.
How unphish detects piracy activity
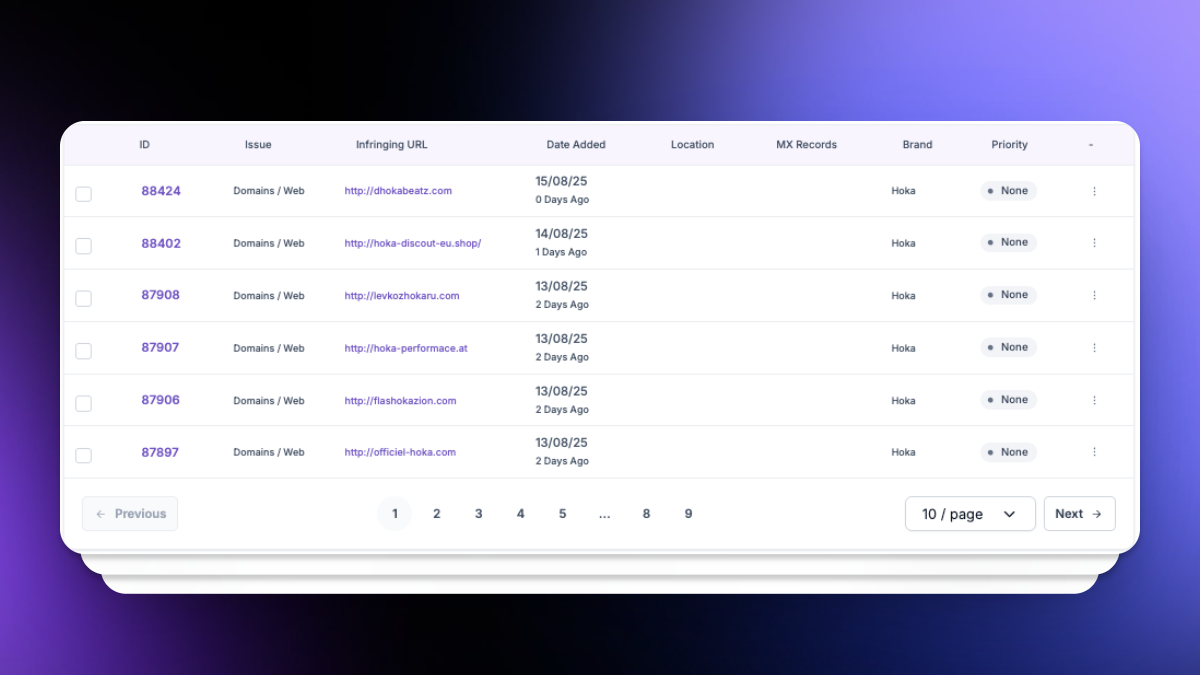
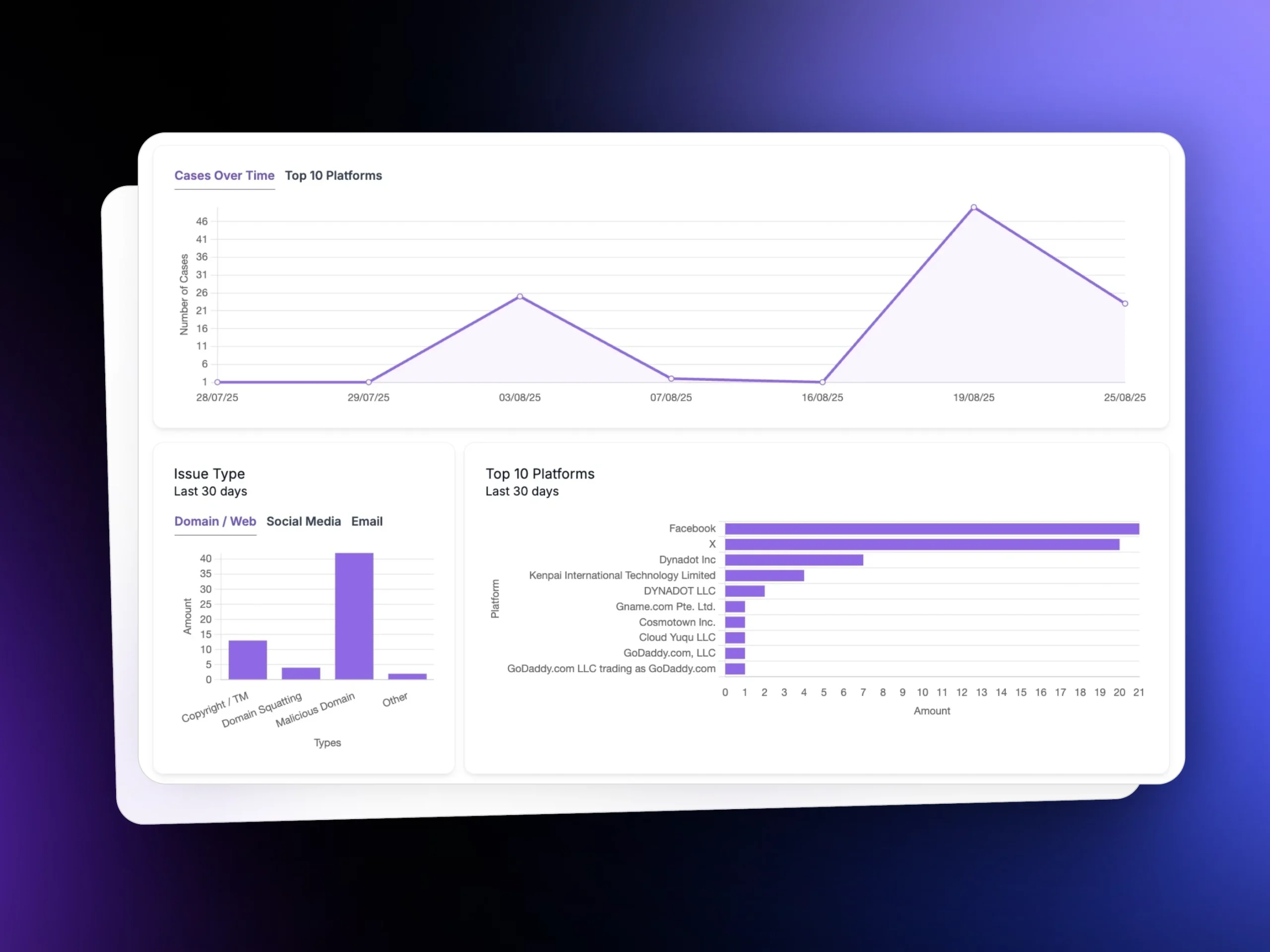
unphish uses a combination of automated monitoring and intelligence led analysis to identify pirated content and unauthorised distribution at scale. Detection capabilities include:
Pirated Content Discovery
Streaming Site Monitoring
Monitoring of streaming sites and embedded players distributing copyrighted material.
Platform & Social Channel Tracking
Piracy Infrastructure Mapping
Analysis of site structures and content reuse to uncover mirrored and related piracy sites.
Why Customers Choose unphish
| unphish | Fragmented / Reactive Approach | |
| Threat Visibility | Continuous monitoring across domains, hosting, social platforms, and attacker infrastructure. | Limited visibility based on complaints or isolated alerts. |
| Detection Speed | Automated detection and risk scoring identify threats early. | Threats are discovered late, often after impact. |
| Infrastructure Insight | Deep analysis reveals campaign links, infrastructure reuse, and attacker patterns. | Little or no visibility into shared infrastructure or repeat activity. |
| Enforcement Execution | Coordinated workflows enable faster, consistent takedown across platforms. | Manual submissions slow down response and create inconsistent outcomes. |
| Verification & Control | Automated validation confirms removal and tracks reappearance. | No structured verification or monitoring after takedown. |
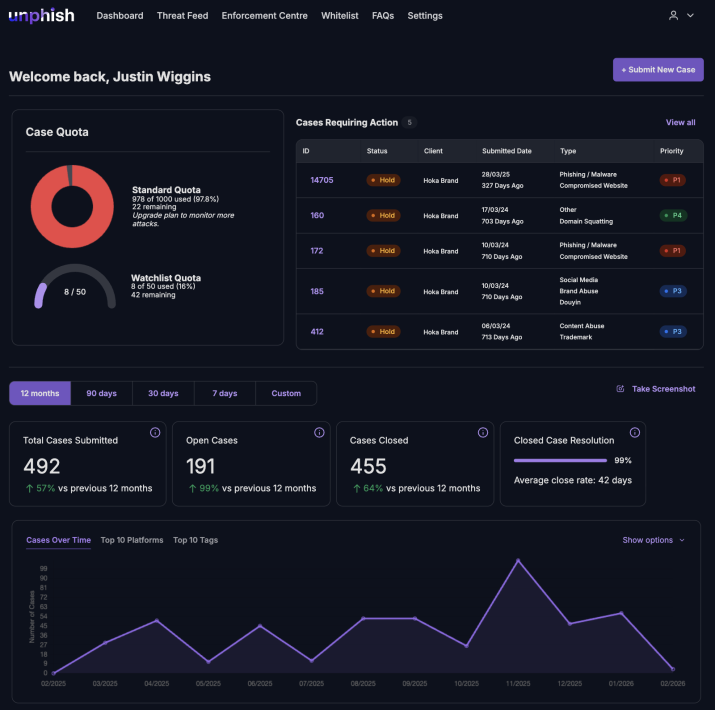
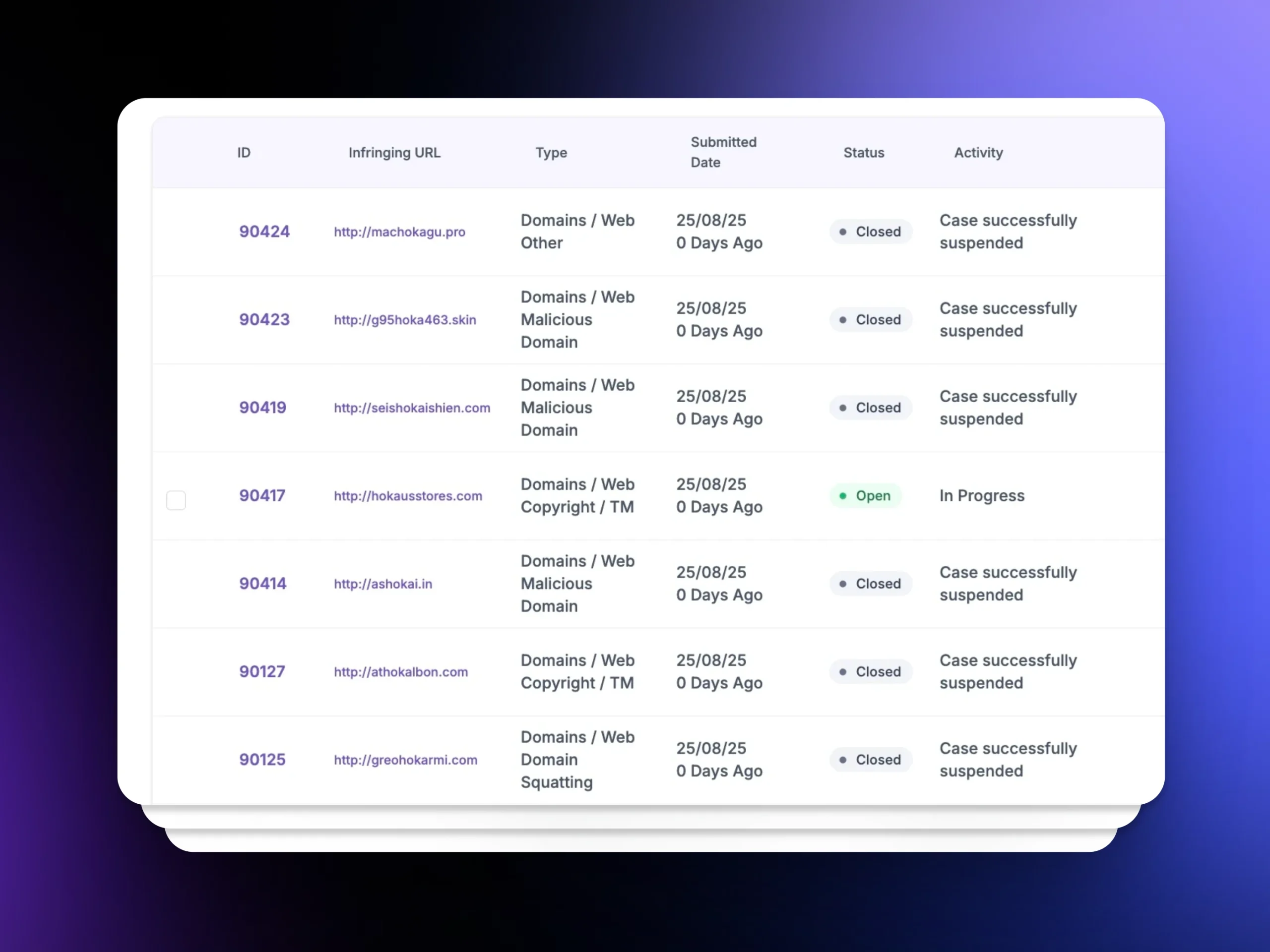
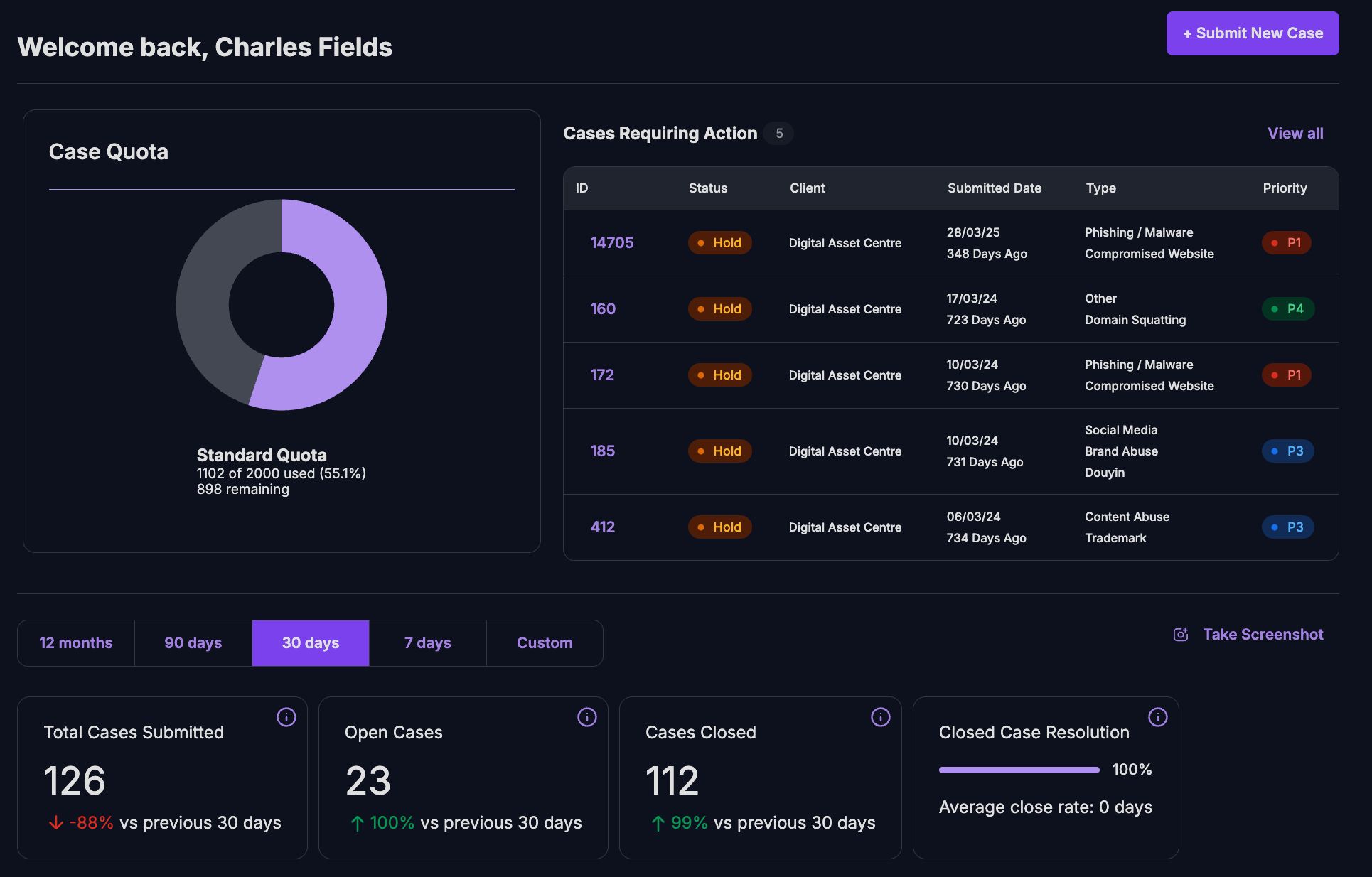
| Operational Visibility | Unified dashboards provide clear status, timelines, and reporting. | Siloed tools limit visibility and create operational gaps. |
How unphish enforces and disrupts piracy
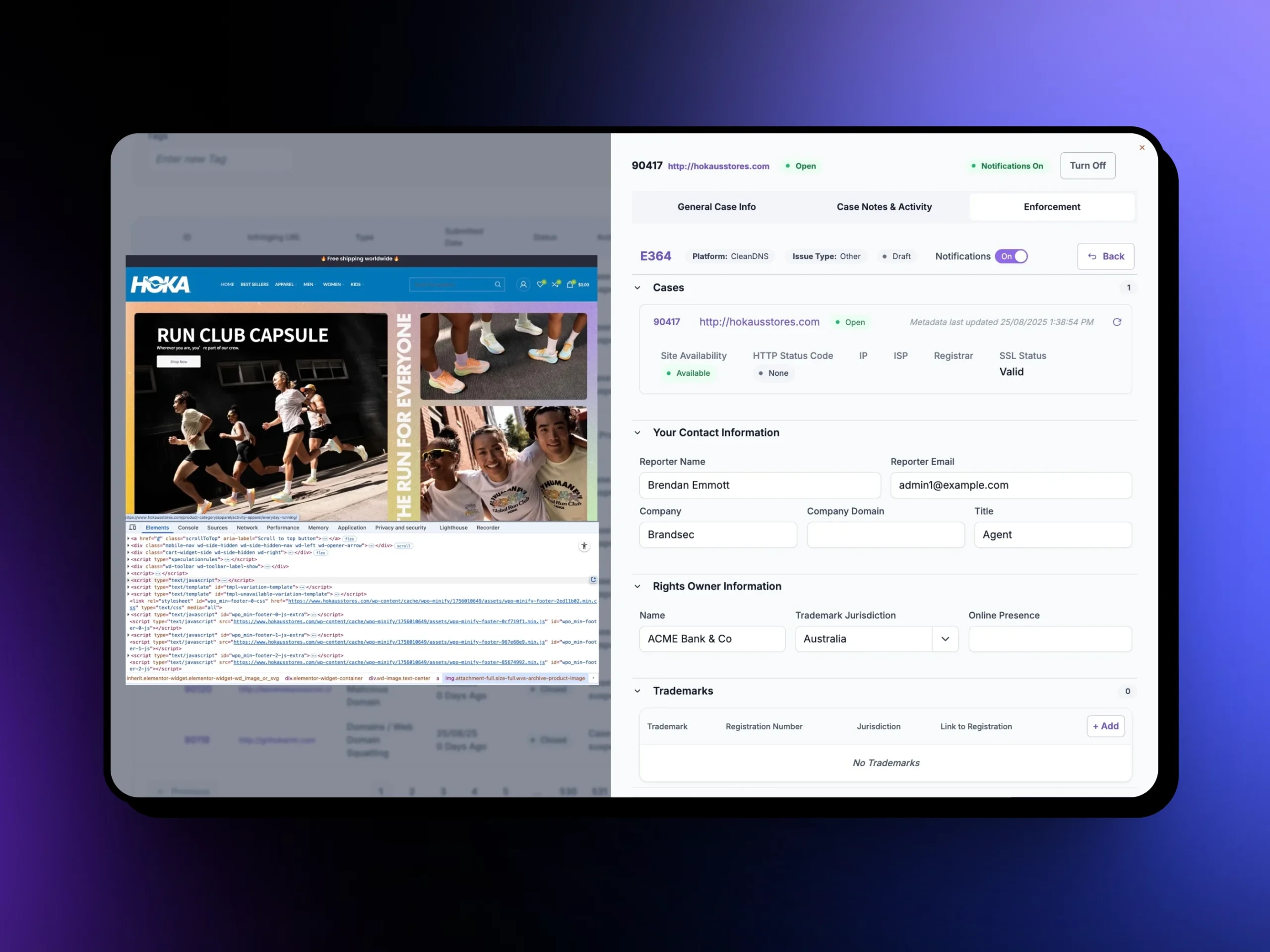
unphish integrates enforcement directly into the platform to enable rapid and repeatable disruption of piracy operations.
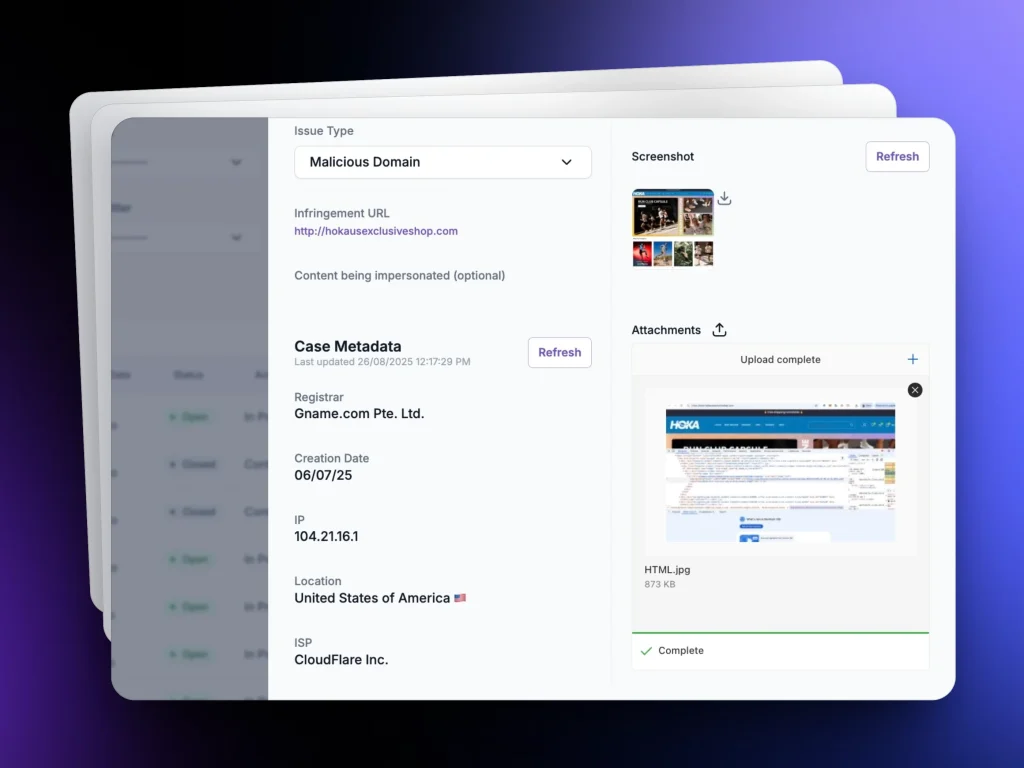
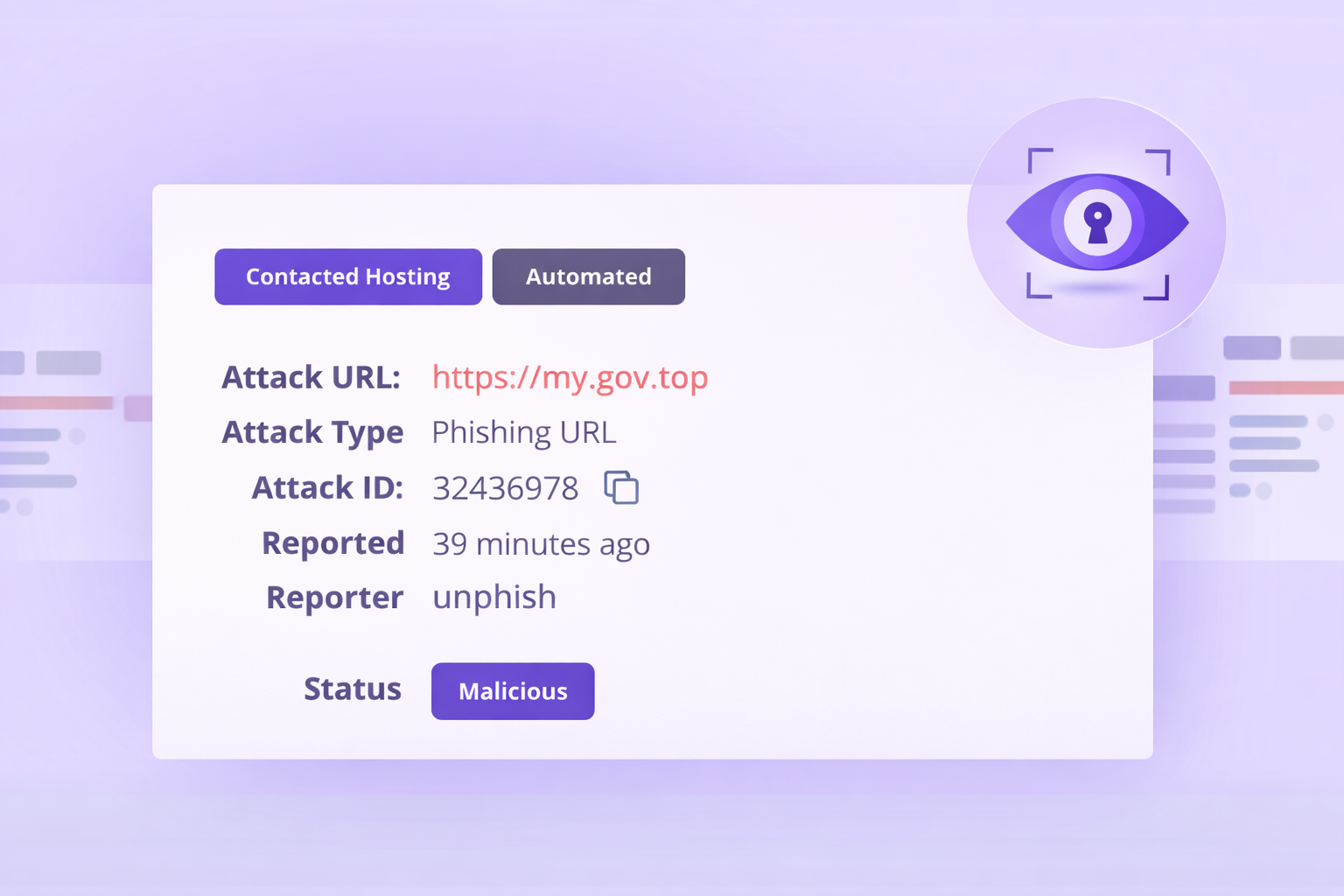
For each piracy incident, unphish automatically captures and preserves evidence, including visual proof of infringement, content references, hosting details, and distribution methods. This evidence supports defensible enforcement actions across a wide range of service providers.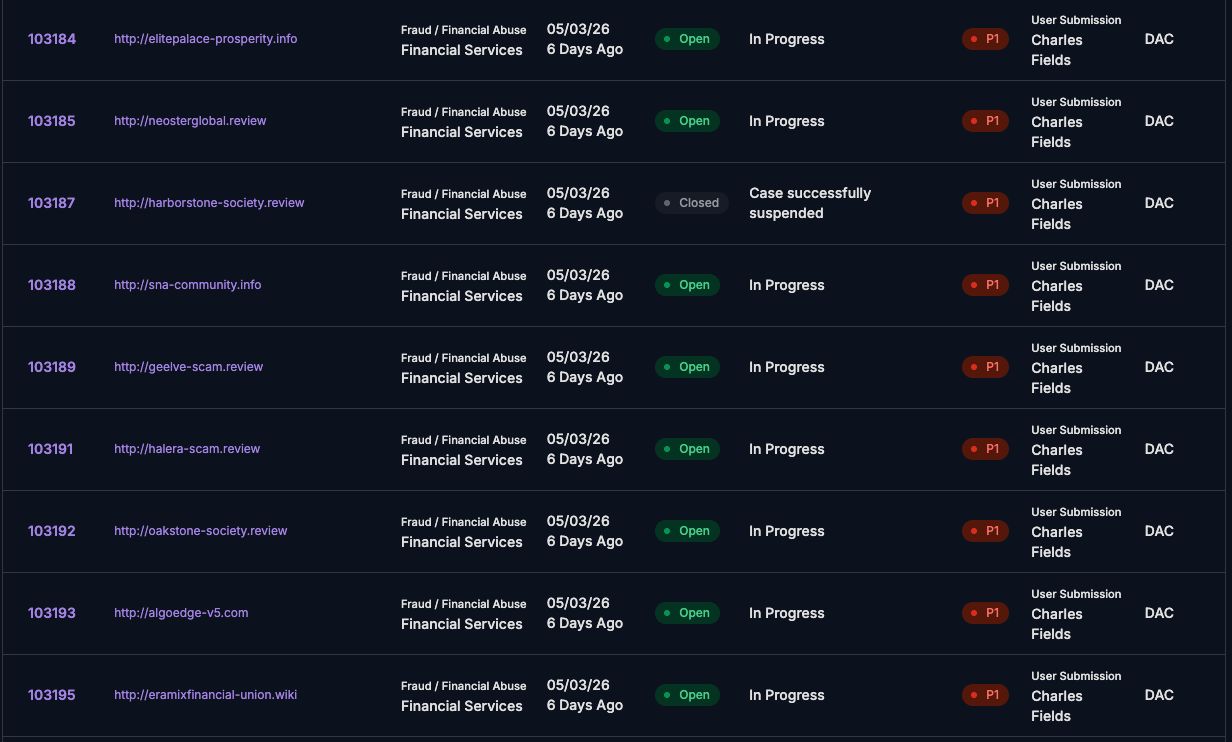
Enforcement actions include
unphish enables rapid enforcement to identify and disrupt piracy networks, remove infringing content, and disable the infrastructure used to distribute copyrighted material.
Fake Profile and Account Removal
Takedown of pirated content from websites and file sharing platforms.
Impersonation Website Takedowns
Removal or blocking of illegal streaming services to prevent unauthorized access.
Scam Numbers and Domains Disabled
Disruption of torrent distribution through targeted enforcement requests.
Repeat Campaign Disruption
Escalation against repeat offenders using shared infrastructure or mirrored sites.
Why piracy protection matters
Piracy is not just a content issue. It undermines revenue, weakens licensing models, and exposes users to additional cyber risks.
unphish helps organisations protect their digital assets by reducing the availability and visibility of pirated content, disrupting large scale distribution networks, and supporting rights holders with clear, auditable enforcement activity.
By combining advanced detection, including computer vision and image recognition, with coordinated takedown workflows, unphish delivers a practical and scalable approach to combating online piracy.
FAQs
Common questions about how unphish detects, investigates, and disrupts digital piracy activity
1. How does unphish detect piracy activity?
2. What happens after pirated content is identified?
3. Can unphish handle large-scale piracy networks?
4. How does unphish help disrupt piracy operations?
Stop Digital Piracy Faster
Detect and disrupt illegal distribution of copyrighted content across streaming sites, torrent networks, and file sharing platforms before it spreads at scale.