Scams
A Smarter Approach to Managing Scam Threats
Scams are rarely one dimensional. Modern scam operations combine multiple tactics, channels, and infrastructure to exploit trust, urgency, and familiarity. What constitutes a scam threat varies significantly by organisation, industry, customer base, and geography.
Rather than treating scams as a fixed category, unphish enables organisations to define and respond to scams based on their unique threat profile.
This approach ensures protection is aligned to how scammers actually target your organisation and customers.
How scam activity differs by organisation
Scammers tailor their methods to the environment they are operating in. A scam profile for a financial institution will differ from that of a retailer, government agency, education provider, or technology platform. Common scam types include:
Investment and Crypto Scams
Fraudsters promote fake investment opportunities or cryptocurrency schemes designed to lure victims with promises of high returns and quick profits.
Romance Scams
Attackers build fake online relationships to gain trust and manipulate victims into sending money, financial information, or account access.
Scam Service Marketplaces
Cybercriminals advertise tools, services, and infrastructure that support scam operations, including phishing kits, messaging campaigns, and impersonation resources.
How unphish detects and disrupts scams
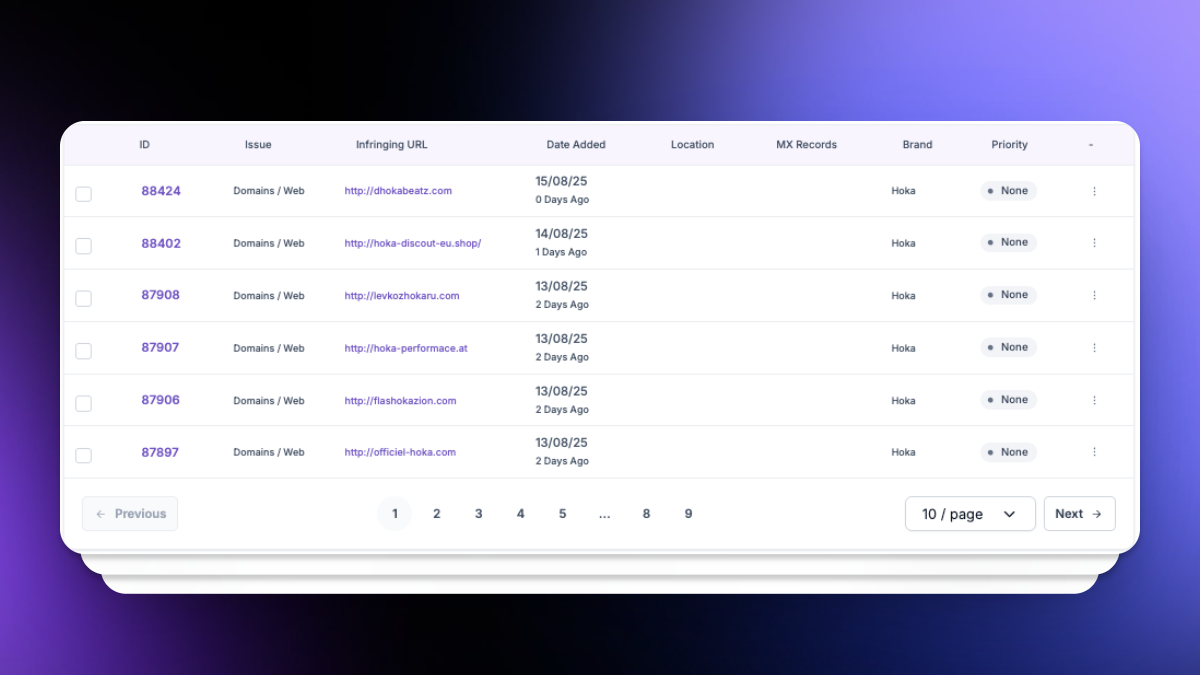
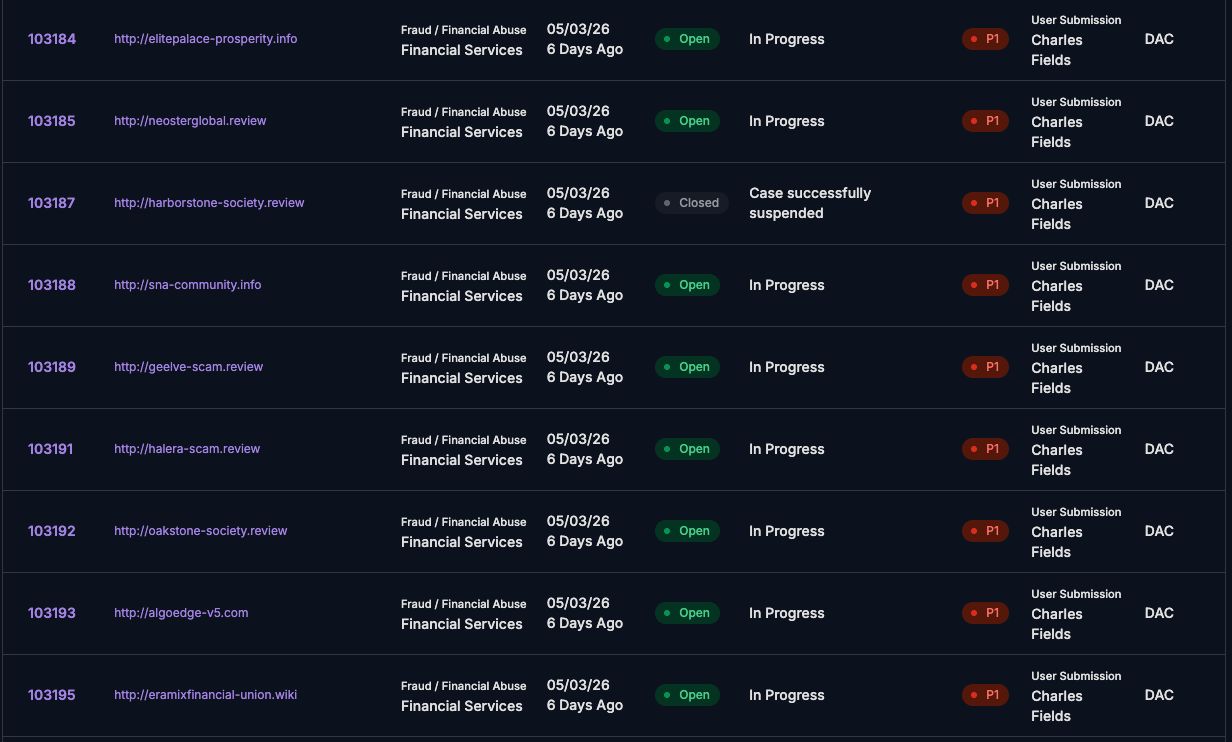
Based on your scam threat profile, unphish continuously monitors for relevant scam activity across domains, websites, social media, app stores, messaging platforms, and underground environments.
Cybercrime Forum & Marketplace Tracking
Brand and Platform Impersonation Detection
Intelligence led analysis and correlation across channels.
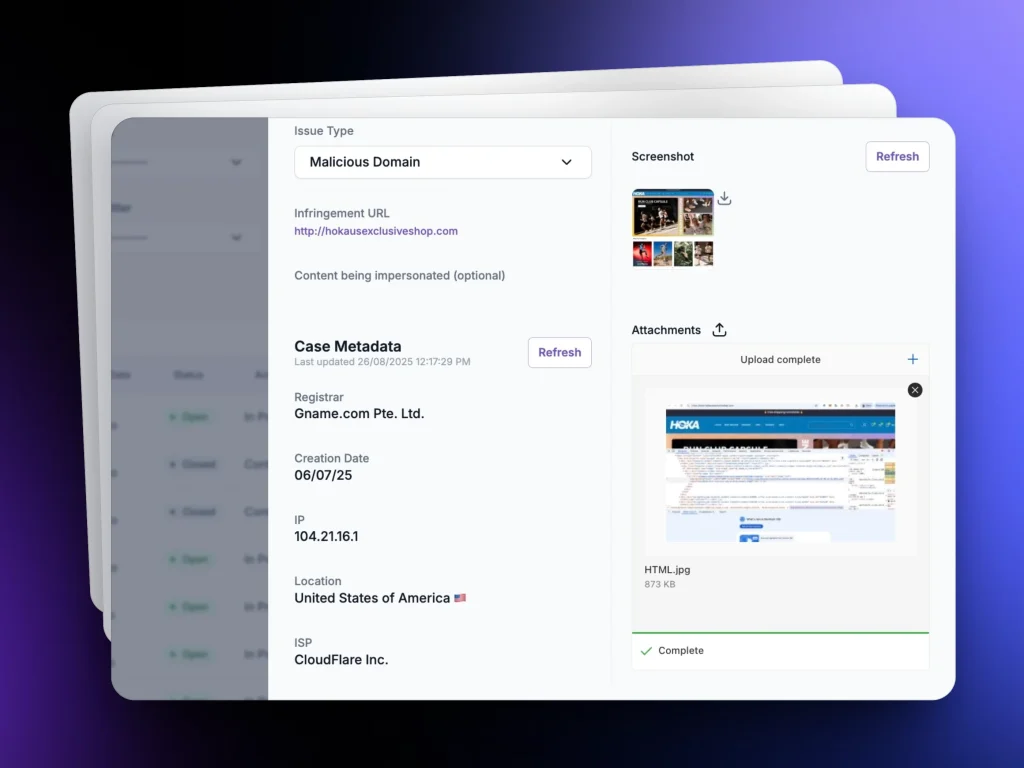
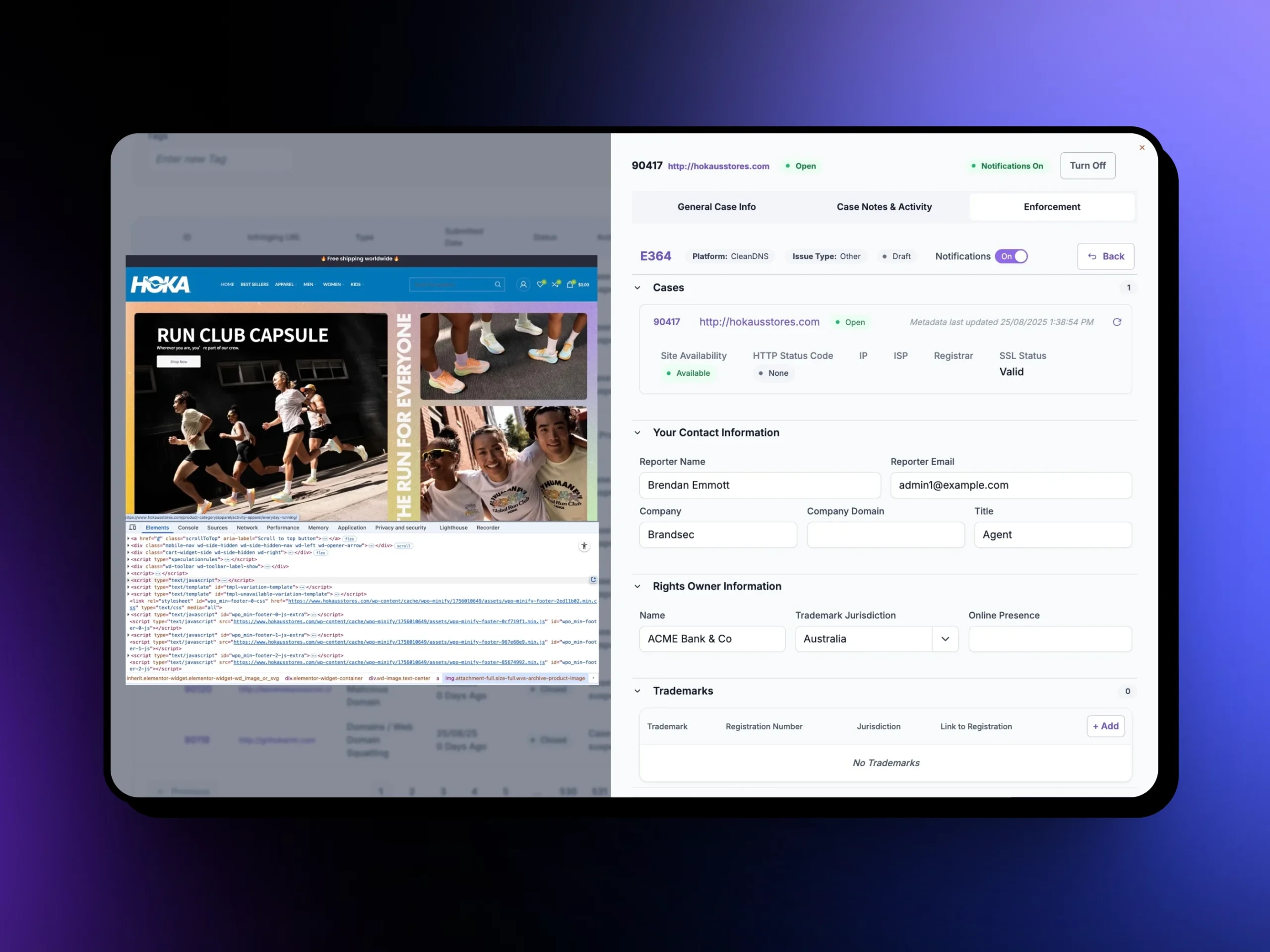
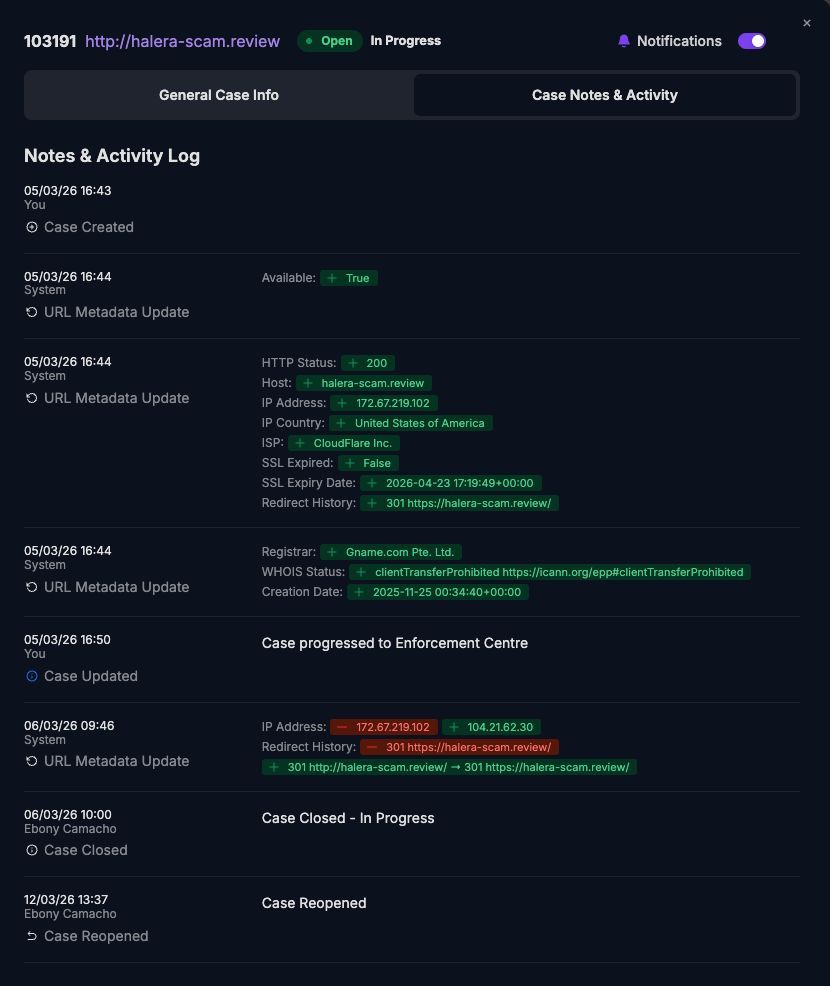
Once scam activity is identified, unphish enables rapid and coordinated disruption through integrated enforcement workflows.
This includes takedown of scam infrastructure, removal of impersonation assets, and disruption of repeat campaigns using shared tooling or hosting.
Why Customers Choose unphish
| unphish | Fragmented / Reactive Approach | |
| Threat Visibility | Continuous monitoring across domains, hosting, social platforms, and attacker infrastructure. | Limited visibility based on complaints or isolated alerts. |
| Detection Speed | Automated detection and risk scoring identify threats early. | Threats are discovered late, often after impact. |
| Infrastructure Insight | Deep analysis reveals campaign links, infrastructure reuse, and attacker patterns. | Little or no visibility into shared infrastructure or repeat activity. |
| Enforcement Execution | Coordinated workflows enable faster, consistent takedown across platforms. | Manual submissions slow down response and create inconsistent outcomes. |
| Verification & Control | Automated validation confirms removal and tracks reappearance. | No structured verification or monitoring after takedown. |
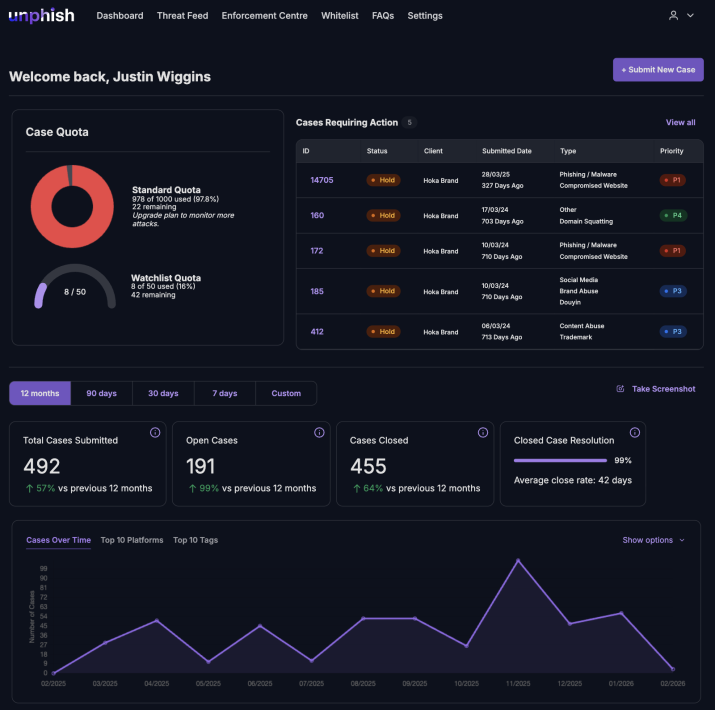
| Operational Visibility | Unified dashboards provide clear status, timelines, and reporting. | Siloed tools limit visibility and create operational gaps. |
How unphish define scam threat profile
unphish works with organisations to define a scam threat profile based on real world targeting, historical incidents, and risk exposure. This profile determines what threats are monitored, prioritised, and disrupted.
Defining Your Organisation’s Scam Threat Profile
unphish works with organisations to build a scam threat profile based on real targeting patterns, past incidents, and risk exposure. This profile helps determine which threats should be monitored, prioritised, and disrupted.
Brand and Executive Impersonation
Identifying how scammers imitate your brand, products, services, or leadership to mislead customers and partners.
Scam Distribution Channels
Understanding the platforms and channels scammers use to reach your customers, including email, messaging apps, websites, and social media.
High-Impact Scam
Types
Prioritising scam types most likely to cause financial loss, customer harm, or reputational damage.
Geographic and Risk Considerations
Assessing regional targeting, regulatory factors, and organisational risk tolerance to ensure informed.
Why a threat profile driven approach matters
Scam activity evolves constantly. New tactics emerge, platforms change, and attacker behaviour adapts to enforcement pressure.
A fixed, one size fits all approach quickly becomes ineffective.
unphish enables organisations to adapt by evolving their scam use cases in line with changing threat activity, business priorities, and customer risk.
By aligning detection and enforcement to an organisation’s specific scam threat profile, unphish delivers more meaningful protection, faster outcomes, and greater resilience against cyber enabled fraud.
FAQs
Common questions about how unphish detects, investigates, and disrupts scam threat activity.
1. How does unphish detect scam threats targeting organisations?
2. What happens after a scam threat is identified?
3. Can unphish identify organised scam networks?
4. How does unphish help disrupt scam campaigns?
Detect and Disrupt Scam Threats Early
Identify scam campaigns, impersonation activity, and fraud infrastructure targeting your organisation before they reach customers or cause financial and reputational harm.