Takedown
Remove Phishing Threats Before They Spread
unphish helps organisations identify, validate, and remove phishing sites, impersonation accounts, fake apps, and malicious infrastructure with speed and precision. Our takedown workflow is built to reduce exposure, protect customers, and limit brand damage.
Built for fast action, structured escalation, and measurable outcomes.
unphish combines automation, analyst oversight, and enforcement workflows designed for real-world abuse cases.
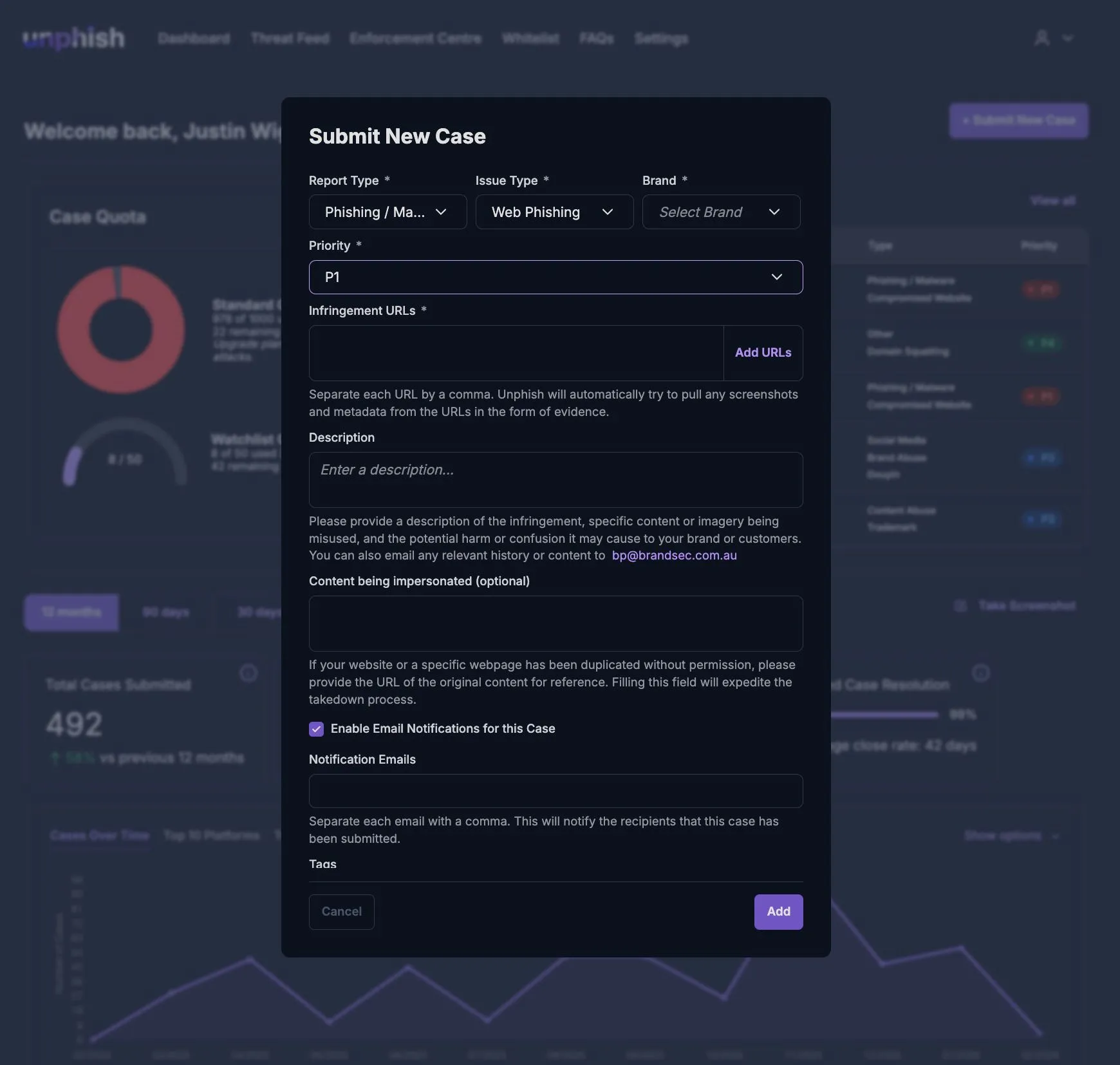
Automated Takedown Workflows
Launch enforcement actions as soon as a threat is validated.
Global Enforcement Coverage
Support takedowns across registrars, hosts, and platforms.
Evidence-Ready
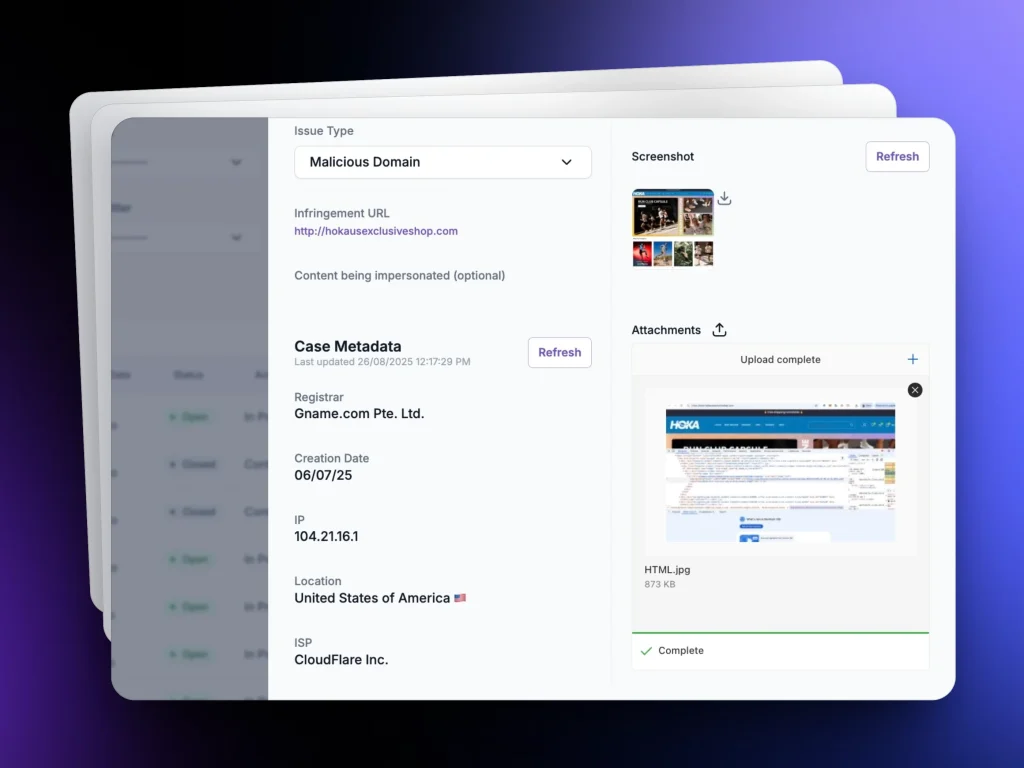
Case Files
Capture the details needed to support enforcement and escalation.
Ongoing
Monitoring
Track re-hosting, re-registration, and repeat abuse after removal.
From Detection to Removal in One Workflow
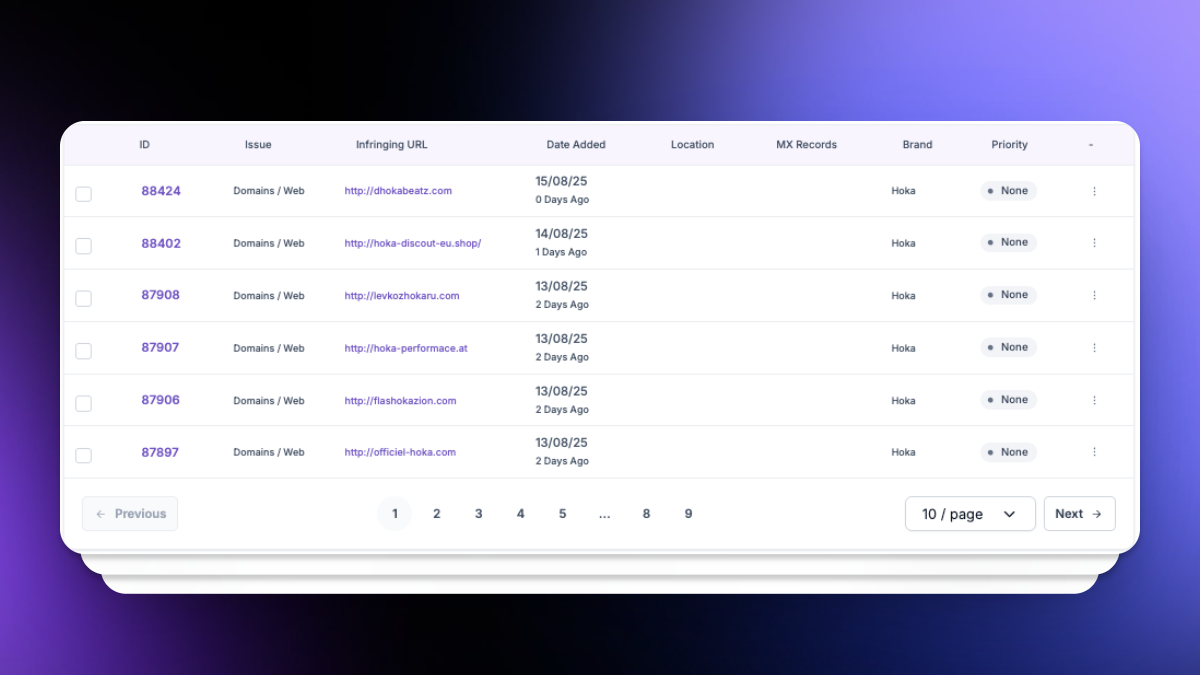
Identify the Threat
Validate the Case
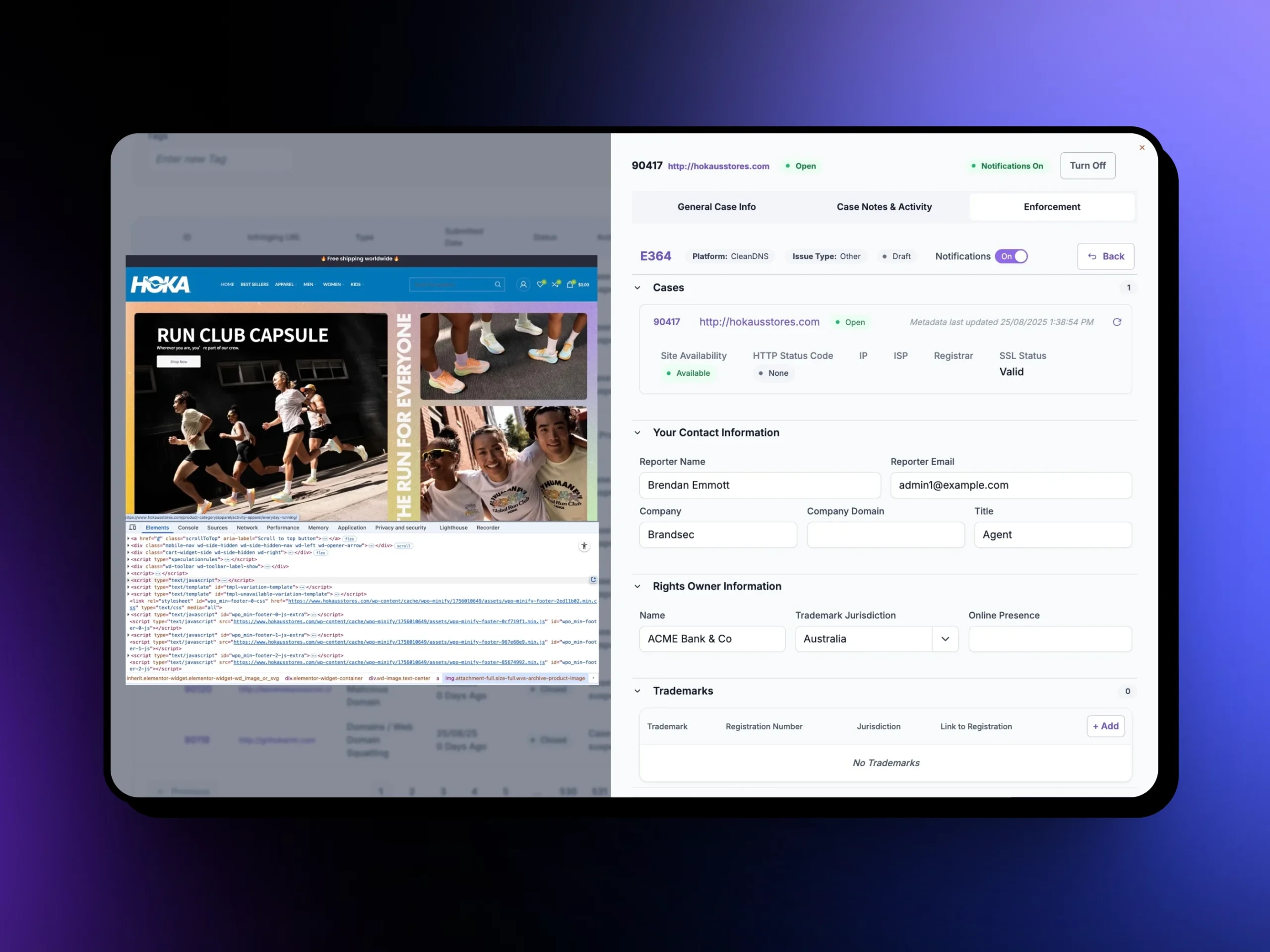
Trigger Takedown
Verify Removal
Complete Digital Risk Protection
Takedown across every place attackers try to hide.
unphish helps remove threats wherever they appear online.
Website Takedown
Remove phishing sites, cloned login pages, and fraudulent domains.
Social Media Takedown
Take down fake profiles, impersonation accounts, and malicious posts.
Mobile App Takedown
Identify and remove fraudulent apps published to mobile marketplaces.
Ad and Campaign Abuse
Disrupt malicious ads and deceptive campaigns used to funnel victims.
Seamless Communication and Tools
Keep every stakeholder aligned throughout the takedown process.
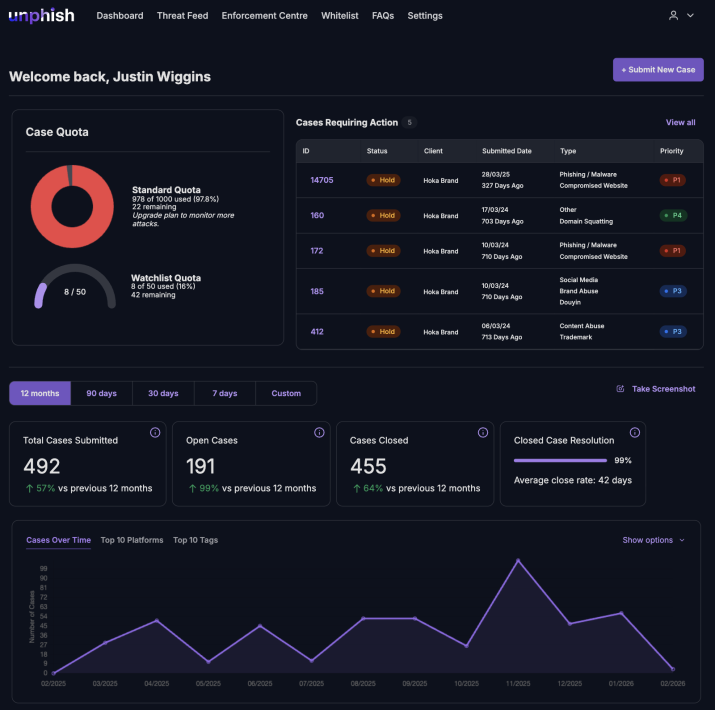
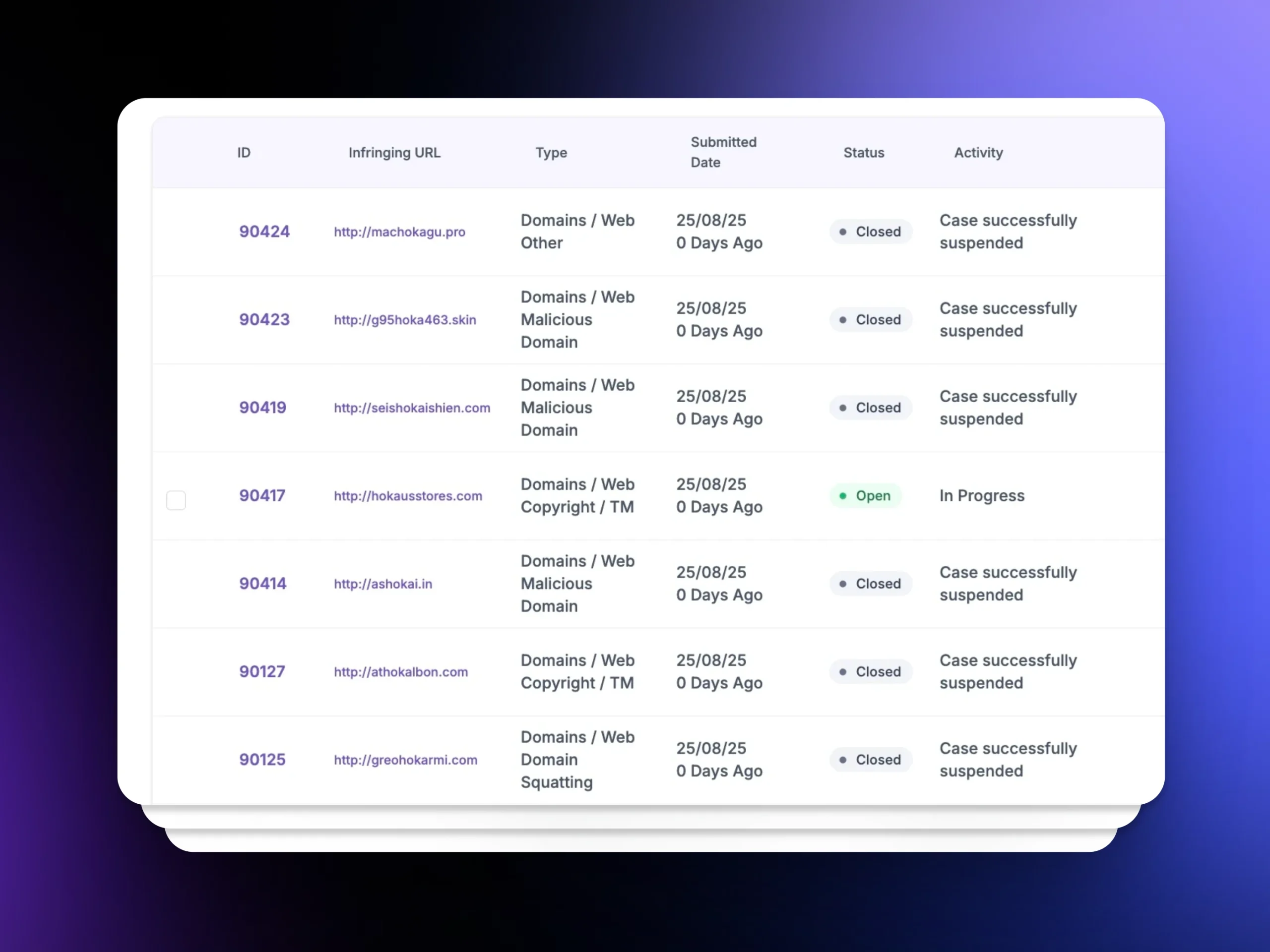
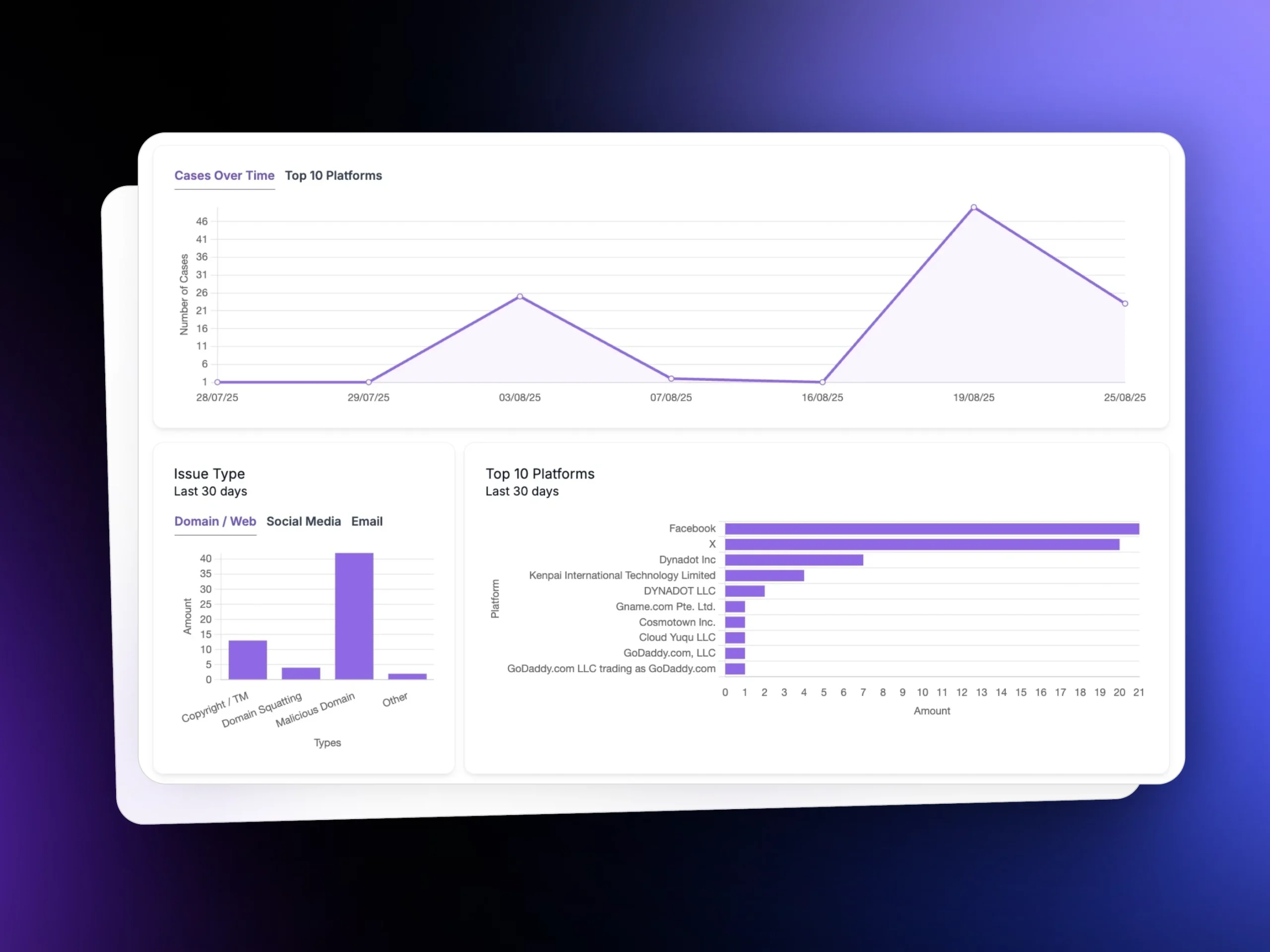
Dashboard Visibility
Track case status from submission to resolution.
Alerts and Updates
Stay informed as enforcement progresses.
Centralised Case Management
Keep evidence, notes, and actions in workflow.
Why Customers Choose unphish
Trusted when speed and accuracy matter most. unphish replaces manual processes with a structured takedown workflow that reduces exposure and improves response across digital channels.
| unphish | Fragmented / Reactive Approach | |
| Threat Visibility | Continuous monitoring across domains, hosting, social platforms, and attacker infrastructure. | Limited visibility based on complaints or isolated alerts. |
| Detection Speed | Automated detection and risk scoring identify threats early. | Threats are discovered late, often after impact. |
| Infrastructure Insight | Deep analysis reveals campaign links, infrastructure reuse, and attacker patterns. | Little or no visibility into shared infrastructure or repeat activity. |
| Enforcement Execution | Coordinated workflows enable faster, consistent takedown across platforms. | Manual submissions slow down response and create inconsistent outcomes. |
| Verification & Control | Automated validation confirms removal and tracks reappearance. | No structured verification or monitoring after takedown. |
| Operational Visibility | Unified dashboards provide clear status, timelines, and reporting. | Siloed tools limit visibility and create operational gaps. |
FAQs
Answers to common questions about takedown workflows, enforcement, and how unphish helps organisations remove threats effectively.
1. What types of threats can unphish help take down?
2. How fast can takedown begin?
3. Do you support global takedowns?
4. Can unphish verify removal after takedown?
5. Is reporting included?
Stop Threats Before They Spread Across Your Digital Ecosystem
Move from fragmented abuse handling to a structured takedown process built for speed, clarity, and scale.